Sathurbot: Distributed Attack to WordPress Sites
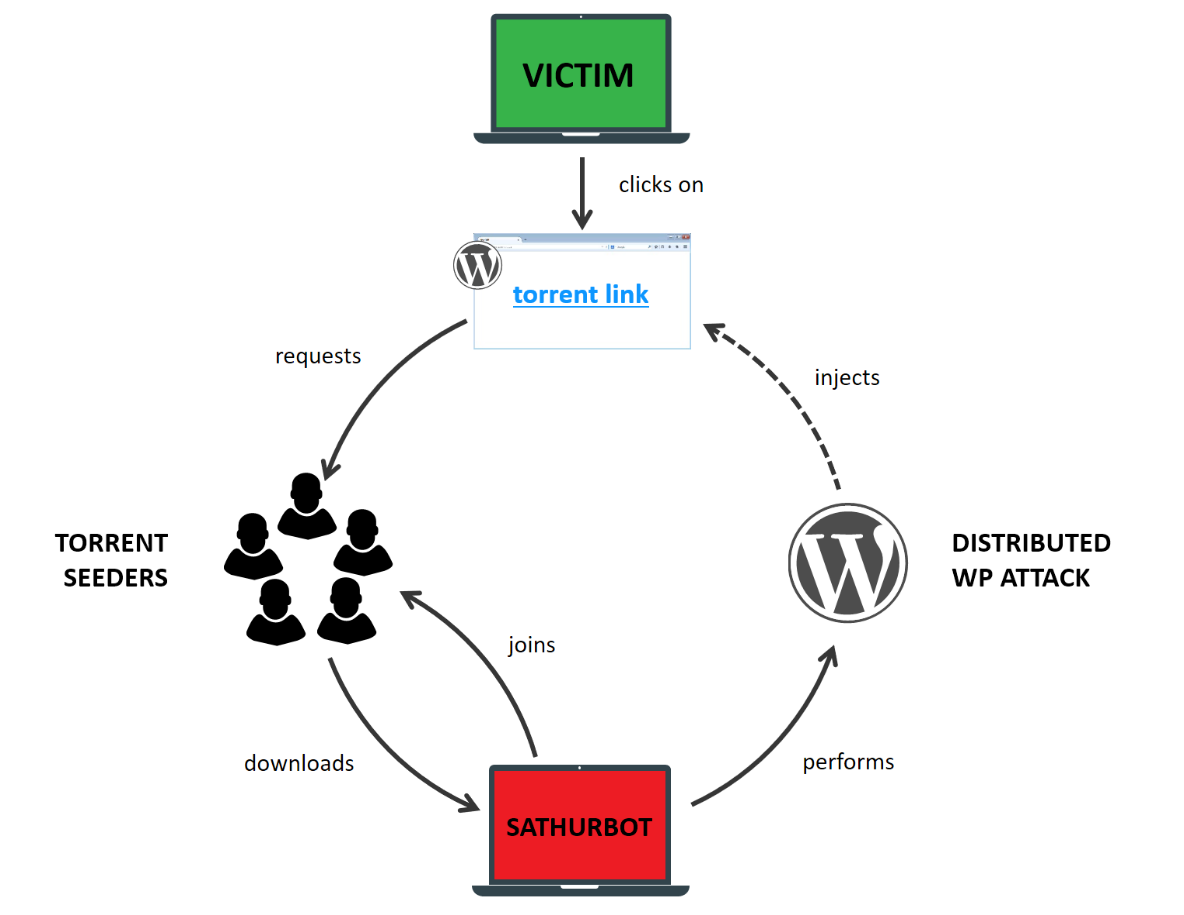
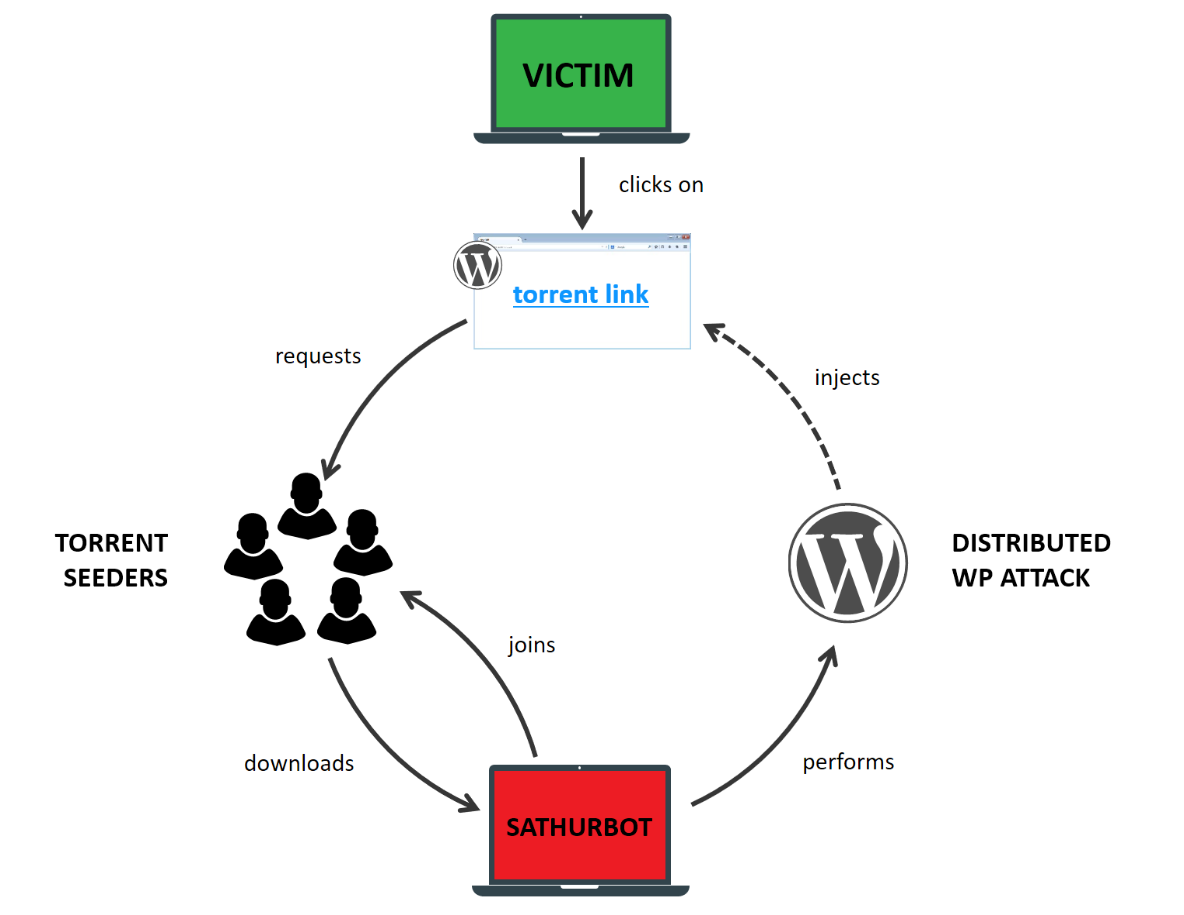
Search for movies and software on torrents carries some risk. There is a chance to get links to torrents posted on sites that have nothing to do with file sharing. They just work on WordPress and have been compromised.
The report tells about the ecosystem of Sathurbot Trojan - spreading through torrents and brute-force attacks on WordPress sites.
')
Sathurbot spreads through hidden torrent pages on compromised sites. The user gets on these pages from the search results when trying to find a movie or software. Some pages use https:


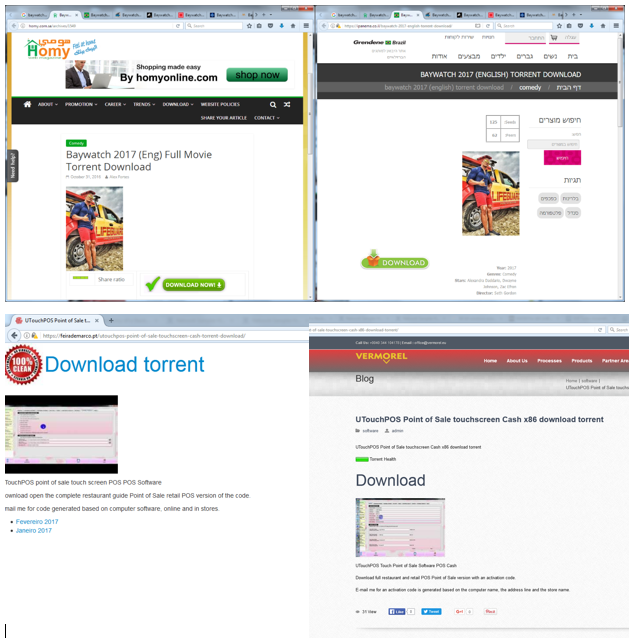
Starting the download, you will find many distributors, downloaded torrents do not cause any special suspicions.
A torrent with a movie contains a video file, a text document with instructions and an installer for a codec, a torrent with a software — an installer and an instruction. The problem in the installer - running this executable file loads the Sathurbot DLL library into the system.
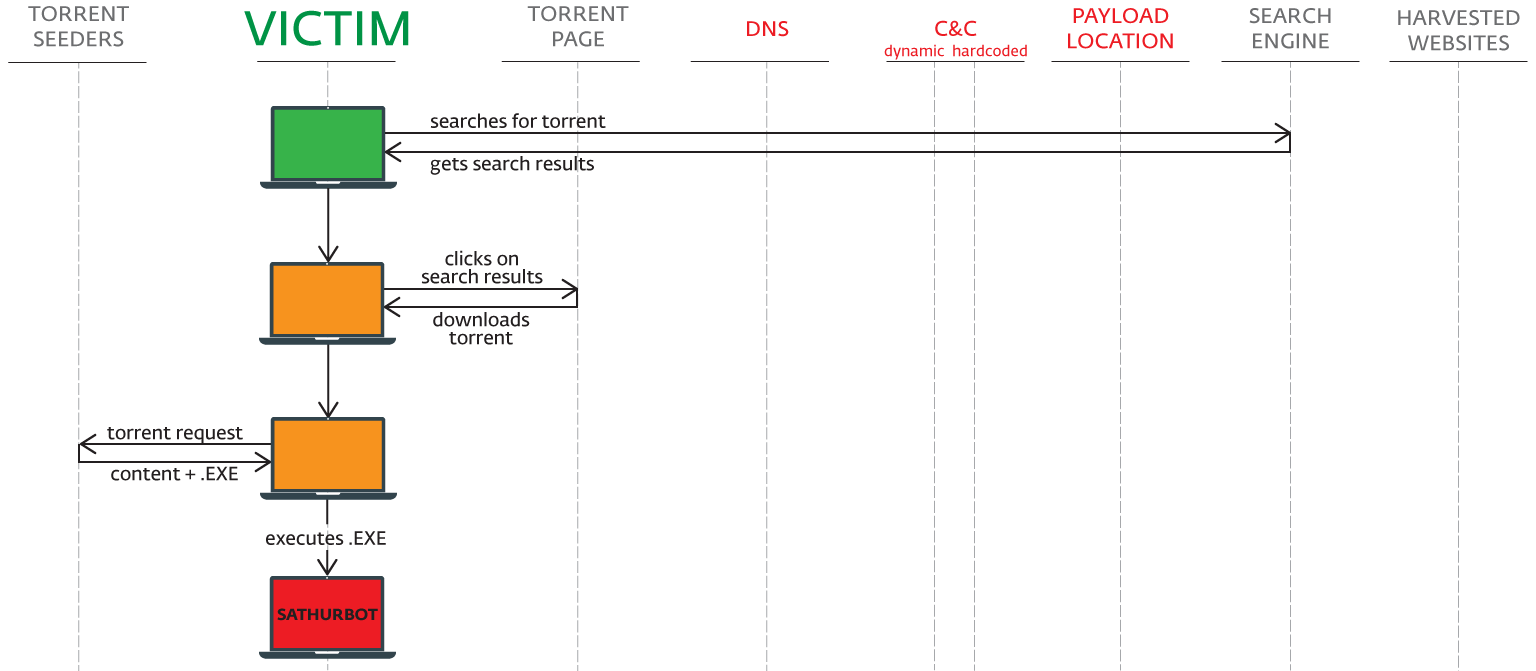
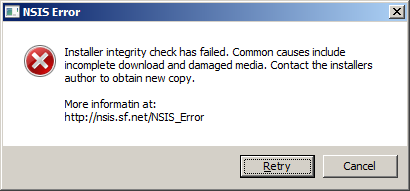
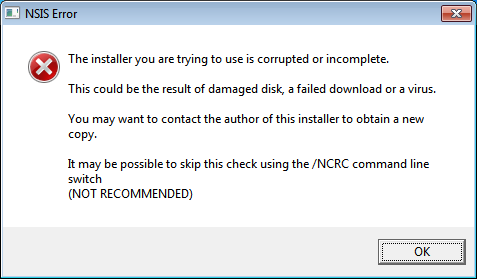
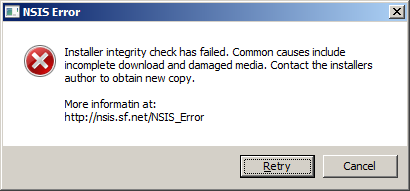
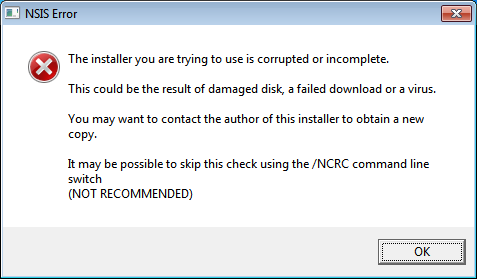
After launching the executable file, the Trojan displays a fake error message (see below). In fact, the download successfully runs in the background, and the computer is part of the Sathurbot botnet.
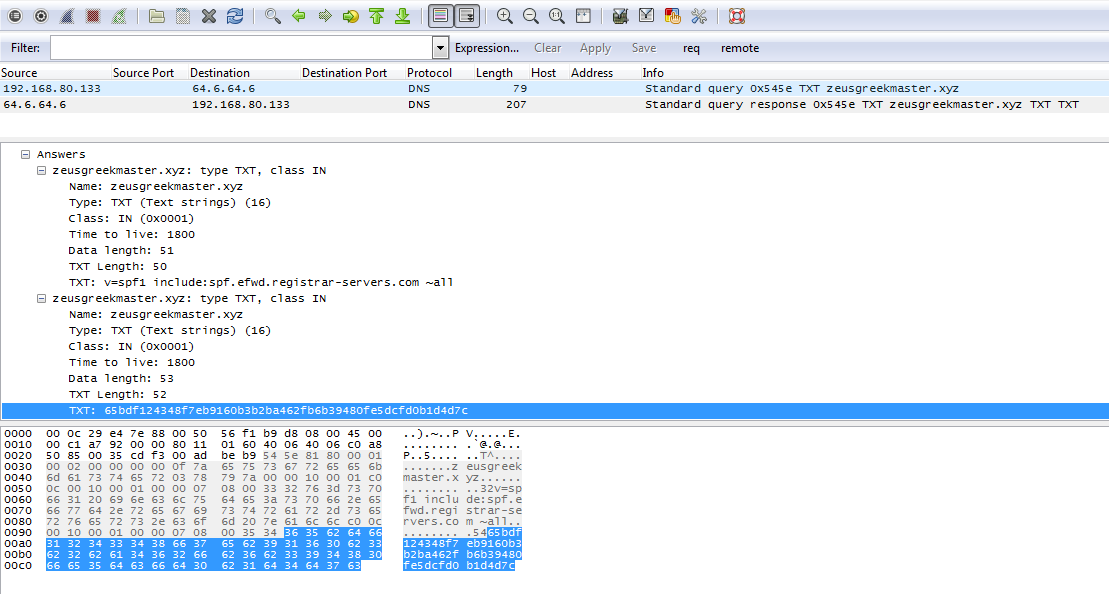
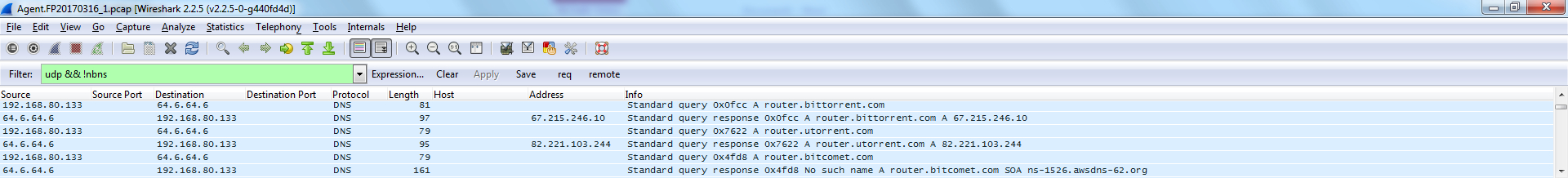
After installation, Sathurbot performs a DNS query to the C & C manager. Trojan can update, load and run other executable files. During the study, we observed the installation of Boaxxe, Kovter and Fleercivet, but not the fact that the operators will be limited to these programs.
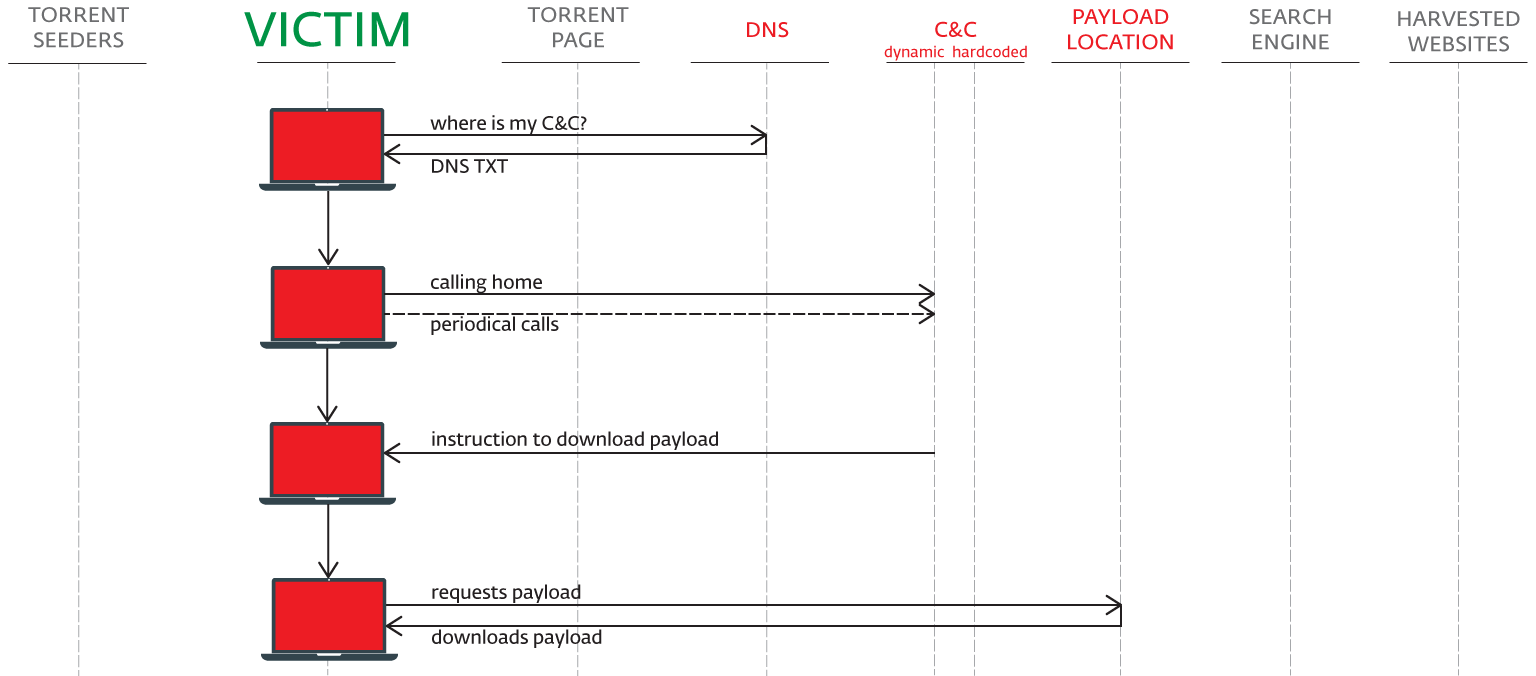
Next, Sathurbot reports a successful installation on C & C.
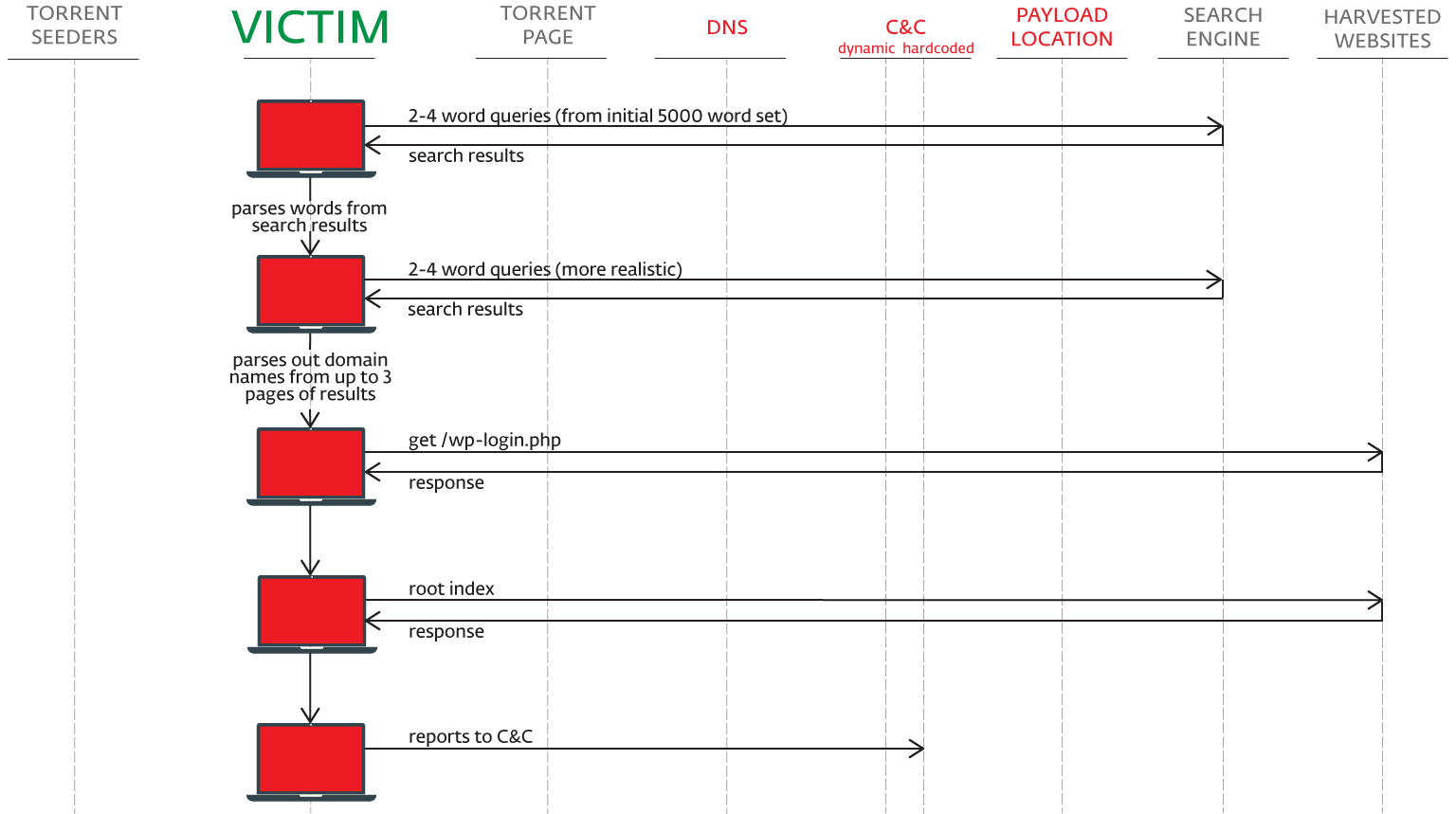
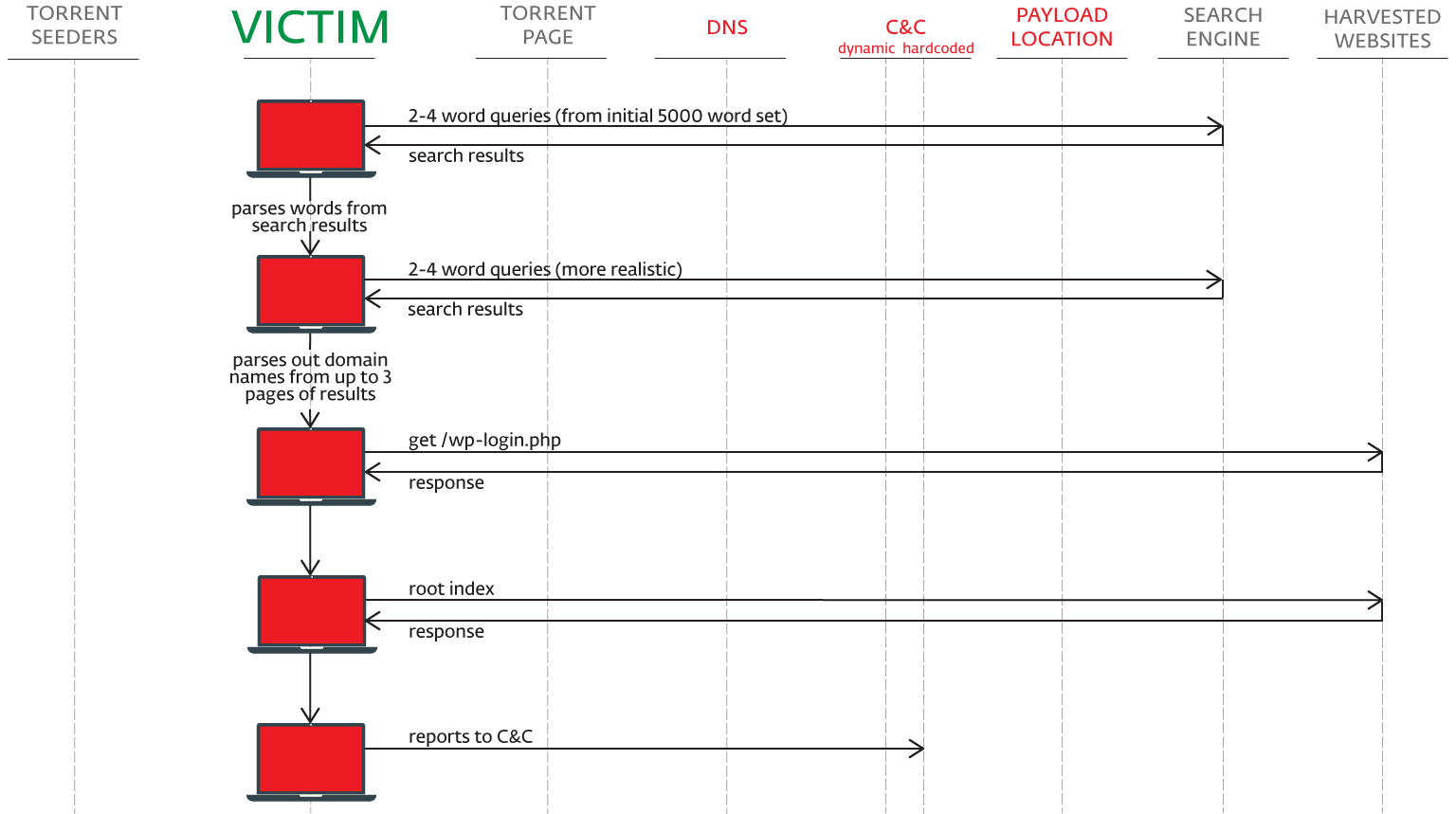
Sathurbot receives a list of 5,000 commonly used words from the management server and uses them as search queries in Google, Bing and Yandex, combining them into phrases randomly. Next, the Trojan selects 2-4 new words, which are most often found on sites that are on the first pages of the search results. New, more meaningful phrases are used in the second round of searches.
Next, Sathurbot examines the sites obtained in the second stage of the first three pages of search results. Trojan selects sites running WordPress, referring to the domain name / wp-login.php . The attackers are also interested in Drupal, Joomla, PHP-NUKE, phpFox, DedeCMS.
The collected domains are transferred to the second C & C server.
The second C & C transmits the credentials for authorization on the domains of interest to the infected computers in the botnet. Each bot out of 20,000 makes only one login attempt - this avoids getting into the "black list" of IP addresses and blocking.
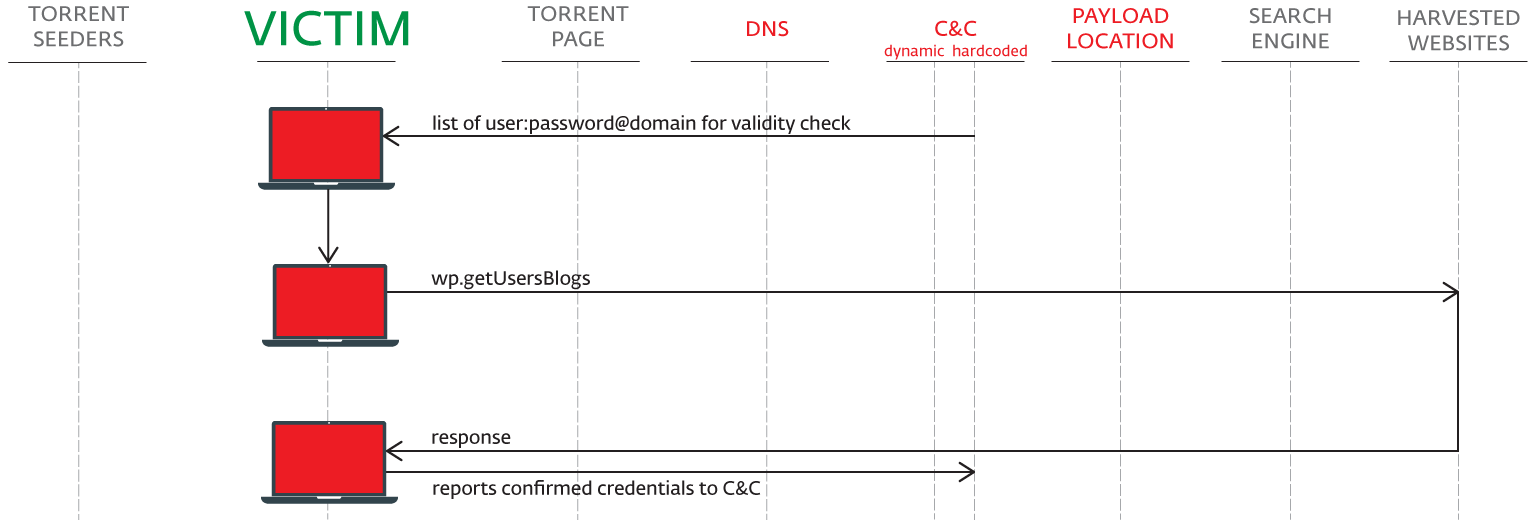
In the course of the study, a list of 10,000 domains was sent to the C & C managing server for verification.

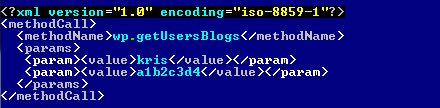
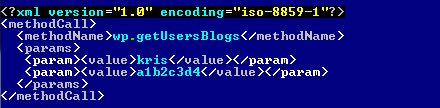
The attacks use the XML-RPC API:
Sathurbot is equipped with the libtorrent library. After infection, computers in the botnet can also distribute malicious torrents.
Bots have different tasks - some computers collect data, others attack the XML-RPC API, some perform both actions.
According to our data, the Sathurbot botnet includes more than 20,000 infected computers and is valid from June 2016.
Numerous attacks via /wp-login.php (even on sites that do not use WordPress) are a direct result of Sathurbot activity. Operators also use wp.getUsersBlogs XMLRPC. We have seen and spread links to malicious torrent in email.
Users of ESET NOD32 anti-virus products are protected from this threat.
Network administrators: check unknown sub-pages and / or directories on the server. If they contain links to download torrents, check the logs for attacks.
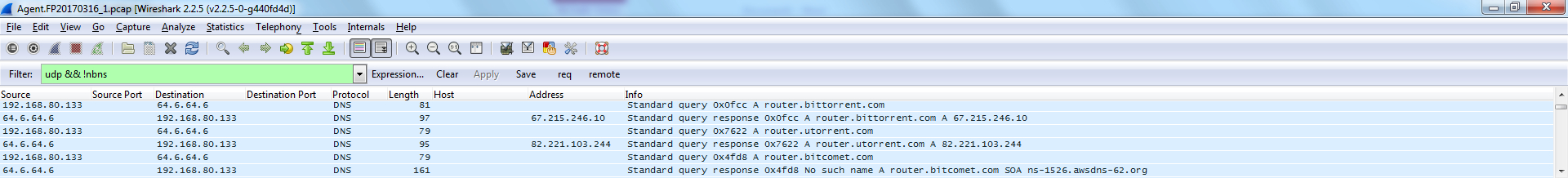
Users: run Wireshark with the http.request filter to see requests of the type GET / wp-login.php and / or POST /xmlrpc.php.
Check the files or registry entries listed in the Infection Indicators section.
Network administrators: change passwords, delete sub-pages that are not related to the site, (optionally) restore the site from a backup.
Users: find a suspicious DLL using a third-party file manager, open the Process Explorer or Task Manager, terminate explorer.exe and / or rundll32.exe, delete (quarantine) the affected DLL, restart the computer.
Note. This will remove Sathurbot, but not other malware that it may have downloaded. Alternatively, use a comprehensive anti-malware product or at least an online scanner.
Network administrators: if the site does not require XML-RPC, disable it and use complex passwords.
Users: Avoid running executable files besides those released by famous developers; Do not download torrents from sites that are not intended for file sharing.
We are currently seeing Sathurbot's installation:
\ ProgramData \ Microsoft \ Performance \ Monitor \ PerformanceMonitor.dll
\ ProgramData \ Microsoft \ Performance \ TheftProtection \ TheftProtection.dll
\ ProgramData \ Microsoft \ Performance \ Monitor \ SecurityHelper.dll
\ Users \ ***** \ AppData \ Local \ Microsoft \ Protect \ protecthost.dll
Runs in the context of rundll32.exe or explorer.exe processes and blocks editing of files and registry keys. There are 32 and 64-bit versions.
Attached folders with torrent files downloaded:
\ SecurityCache \ cache \ resume \
\ SecurityCache \ cache \ rules \
\ SecurityCache \ data \
\ SecurityCache \ zepplauncher.mif - contains DHT nodes
\ temp \
% appdata% \ SYSHashTable \ - contains folders with hashes of visited domains% appdata% \ SYSHashTable \ SyshashInfo.db - a set of target domains, including information about the structure
Installers:
2D9AFB96EAFBCFCDD8E1CAFF492BFCF0488E6B8C
3D08D416284E9C9C4FF36F474C9D46F3601652D5
512789C90D76785C061A88A0B92F5F5778E80BAA
735C8A382400C985B85D27C67369EF4E7ED30135
798755794D124D00EAB65653442957614400D71D
4F52A4A5BA897F055393174B3DFCA1D022416B88
8EDFE9667ECFE469BF88A5A5EBBB9A75334A48B9
5B45731C6BBA7359770D99124183E8D80548B64F
C0F8C75110123BEE7DB5CA3503C3F5A50A1A055E
C8A514B0309BCDE73F7E28EB72EB6CB3ABE24FDD
AF1AE760F055120CA658D20A21E4B14244BC047D
A1C515B965FB0DED176A0F38C811E6423D9FFD86
B9067085701B206D2AC180E82D5BC68EDD584A8B
77625ADEA198F6756E5D7C613811A5864E9874EA
Sathurbot dll:
F3A265D4209F3E7E6013CA4524E02D19AAC951D9
0EA717E23D70040011BD8BD0BF1FFAAF071DA22C
2381686708174BC5DE2F04704491B331EE9D630B
2B942C57CEE7E2E984EE10F4173F472DB6C15256
2F4FAA5CB5703004CA68865D8D5DACBA35402DE4
4EBC55FDFB4A1DD22E7D329E6EF8C7F27E650B34
0EF3ECD8597CE799715233C8BA52D677E98ABDFD
0307BBAC69C54488C124235449675A0F4B0CCEFA
149518FB8DE56A34B1CA2D66731126CF197958C3
3809C52343A8F3A3597898C9106BA72DB7F6A3CB
4A69B1B1191C9E4BC465F72D76FE45C77A5CB4B0
5CCDB41A34ADA906635CE2EE1AB4615A1AFCB2F2
6C03F7A9F826BB3A75C3946E3EF75BFC19E14683
8DA0DC48AFB8D2D1E9F485029D1800173774C837
AC7D8140A8527B8F7EE6788C128AFF4CA92E82C2
E1286F8AE85EB8BD1B6BE4684E3C9E4B88D300DB
Additional payload:
C439FC24CAFA3C8008FC01B6F4C39F6010CE32B6
ABA9578AB2588758AD34C3955C06CD2765BFDF68
DFB48B12823E23C52DAE03EE4F7B9B5C9E9FDF92
FAFF56D95F06FE4DA8ED433985FA2E91B94EE9AD
B728EB975CF7FDD484FCBCFFE1D75E4F668F842F
59189ABE0C6C73B66944795A2EF5A2884715772E
C6BDB2DC6A48136E208279587EFA6A9DD70A3FAA
BEAA3159DBE46172FC79E8732C00F286B120E720
5ED0DF92174B62002E6203801A58FE665EF17B76
70DFABA5F98B5EBC471896B792BBEF4DB4B07C53
10F92B962D76E938C154DC7CBD7DEFE97498AB1E
426F9542D0DDA1C0FF8D2F4CB0D74A1594967636
AA2176834BA49B6A9901013645C84C64478AA931
1C274E18A8CAD814E0094C63405D461E815D736A
61384C0F690036E808F5988B5F06FD2D07A87454
F32D42EF1E5ED221D478CFAA1A76BB2E9E93A0C1
594E098E9787EB8B7C13243D0EDF6812F34D0FBA
1AAFEBAA11424B65ED48C68CDEED88F34136B8DC
BA4F20D1C821B81BC324416324BA7605953D0605
E08C36B122C5E8E561A4DE733EBB8F6AE3172BF0
7748115AF04F9FD477041CB40B4C5048464CE43E
3065C1098B5C3FC15C783CDDE38A14DFA2E005E4
FA25E212F77A06C0B7A62C6B7C86643660B24DDA
FADADFFA8F5351794BC5DCABE301157A4A2EBBCF
B0692A03D79CD2EA7622D3A784A1711ADAABEE8D
9411991DCF1B4ED9002D9381083DE714866AEA00
DNS:
zeusgreekmaster.xyz
apollogreekmaster.xyz
C & C:
jhkabmasdjm2asdu7gjaysgddasd.xyz
boomboomboomway.xyz
mrslavelemmiwinkstwo.xyz
uromatalieslave.space
newforceddomainisherenow.club
justanotherforcedomain.xyz
artemisoslave.xyz
asxdq2saxadsdawdq2sasaddfsdfsf4ssfuckk.xyz
kjaskdhkaudhsnkq3uhaksjndkud3asds.xyz
badaboommail.xyz
Torrent trackers:
badaboomsharetracker.xyz
webdatasourcetraffic.xyz
sharetorrentsonlinetracker.xyz
webtrafficsuccess.xyz
You may need a third-party tool, because Windows Regedit does not display this:
HKLM \ SYSTEM \ CurrentControlSet \ services \ SharedAccess \ Parameters \ FirewallPolicy \ FirewallRules \ {variable GUID} = “v2.10 | Action = Allow | Active = TRUE | Dir = In | Profile = Private | Profile = Public | App = C: \\ Windows \\ explorer.exe | Name = Windows Explorer | ”
HKLM \ SYSTEM \ CurrentControlSet \ services \ SharedAccess \ Parameters \ FirewallPolicy \ FirewallRules \ {variable GUID} = “v2.10 | Action = Allow | Active = TRUE | Dir = In | Profile = Private | Profile = Public | App = C: \\ Windows \\ system32 \\ rundll32.exe | Name = Windows host process (Rundll32) | ”
HKLM \ SOFTWARE \ Microsoft \ Windows \ CurrentVersion \ Explorer \ ShellIconOverlayIdentifiers \ 0TheftProtectionDll = {GUID1}
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} = “Windows Theft Protection”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} \ InprocServer32 = “C: \\ ProgramData \\ Microsoft \\ Performance \\ TheftProtection \\ TheftProtection.dll”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} \ InprocServer32 \ ThreadingModel = “Apartment”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID2}
{GUID2} records vary in all samples, contain six long subkeys, the content is binary type and is encrypted. Used to store variables, temporary values and IP, C & C, UID settings.
For example, {GUID2} looks like this:
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000003
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000002
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000001
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000009
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000011
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00010001
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00010002
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000008
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000007
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000004
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000010
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00020001
The report tells about the ecosystem of Sathurbot Trojan - spreading through torrents and brute-force attacks on WordPress sites.
')
Torrent
Sathurbot spreads through hidden torrent pages on compromised sites. The user gets on these pages from the search results when trying to find a movie or software. Some pages use https:


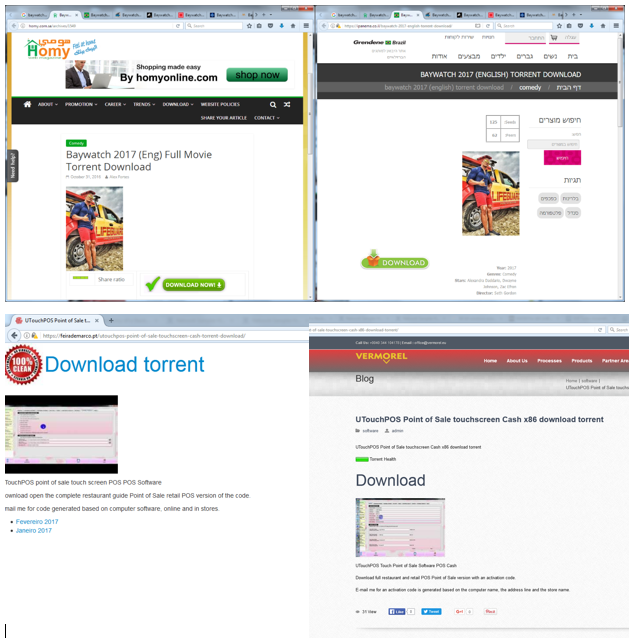
Starting the download, you will find many distributors, downloaded torrents do not cause any special suspicions.
A torrent with a movie contains a video file, a text document with instructions and an installer for a codec, a torrent with a software — an installer and an instruction. The problem in the installer - running this executable file loads the Sathurbot DLL library into the system.
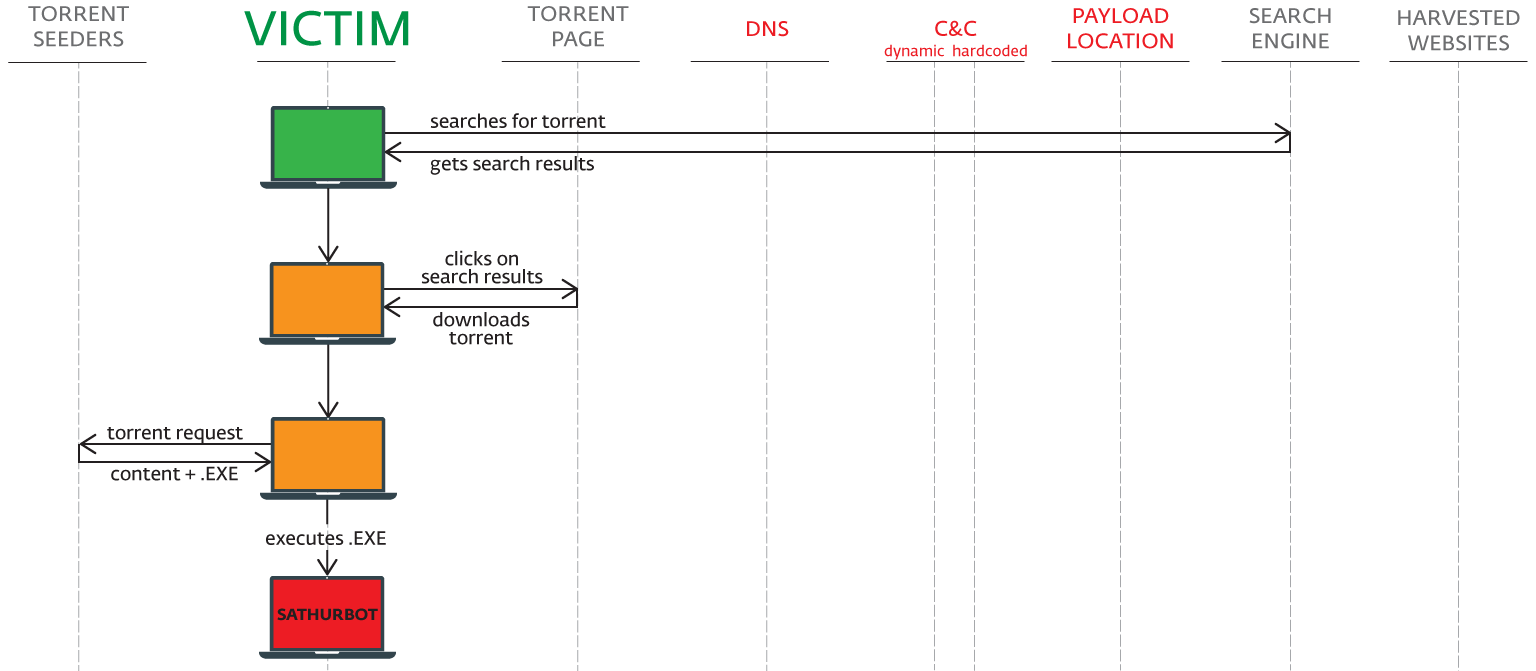
After launching the executable file, the Trojan displays a fake error message (see below). In fact, the download successfully runs in the background, and the computer is part of the Sathurbot botnet.
Backdoor and bootloader
After installation, Sathurbot performs a DNS query to the C & C manager. Trojan can update, load and run other executable files. During the study, we observed the installation of Boaxxe, Kovter and Fleercivet, but not the fact that the operators will be limited to these programs.
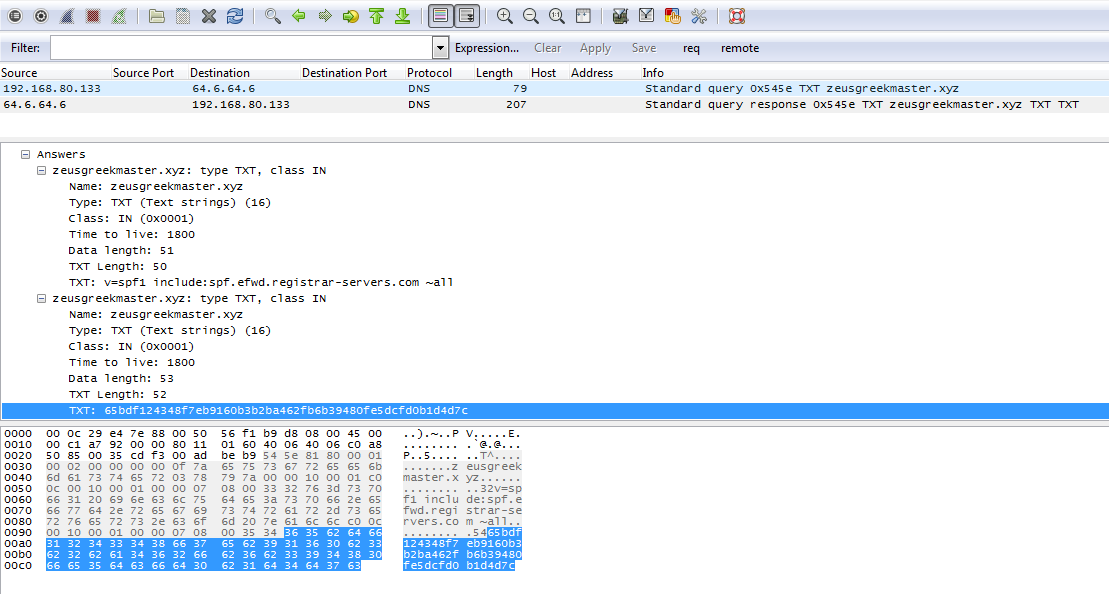
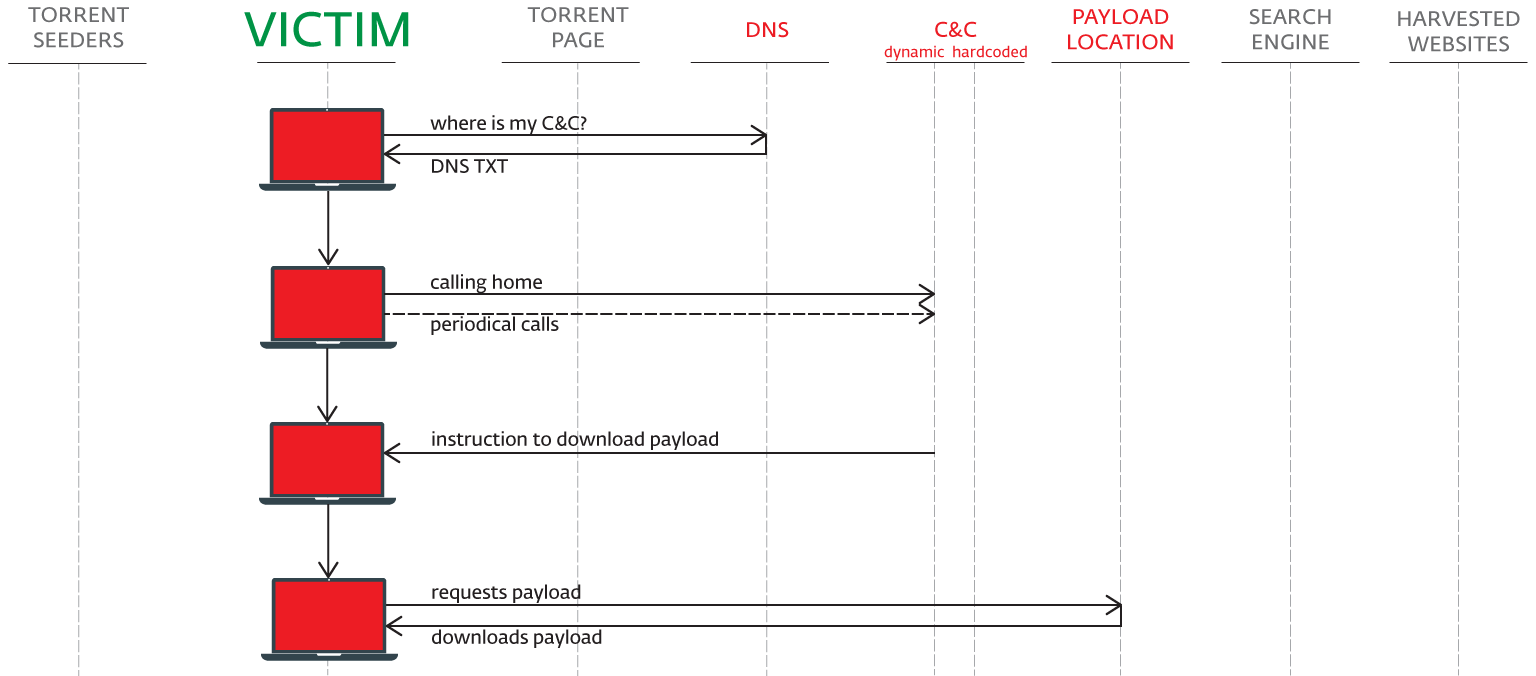
Next, Sathurbot reports a successful installation on C & C.
Data collection
Sathurbot receives a list of 5,000 commonly used words from the management server and uses them as search queries in Google, Bing and Yandex, combining them into phrases randomly. Next, the Trojan selects 2-4 new words, which are most often found on sites that are on the first pages of the search results. New, more meaningful phrases are used in the second round of searches.
Next, Sathurbot examines the sites obtained in the second stage of the first three pages of search results. Trojan selects sites running WordPress, referring to the domain name / wp-login.php . The attackers are also interested in Drupal, Joomla, PHP-NUKE, phpFox, DedeCMS.
The collected domains are transferred to the second C & C server.
WordPress Distributed Attack
The second C & C transmits the credentials for authorization on the domains of interest to the infected computers in the botnet. Each bot out of 20,000 makes only one login attempt - this avoids getting into the "black list" of IP addresses and blocking.
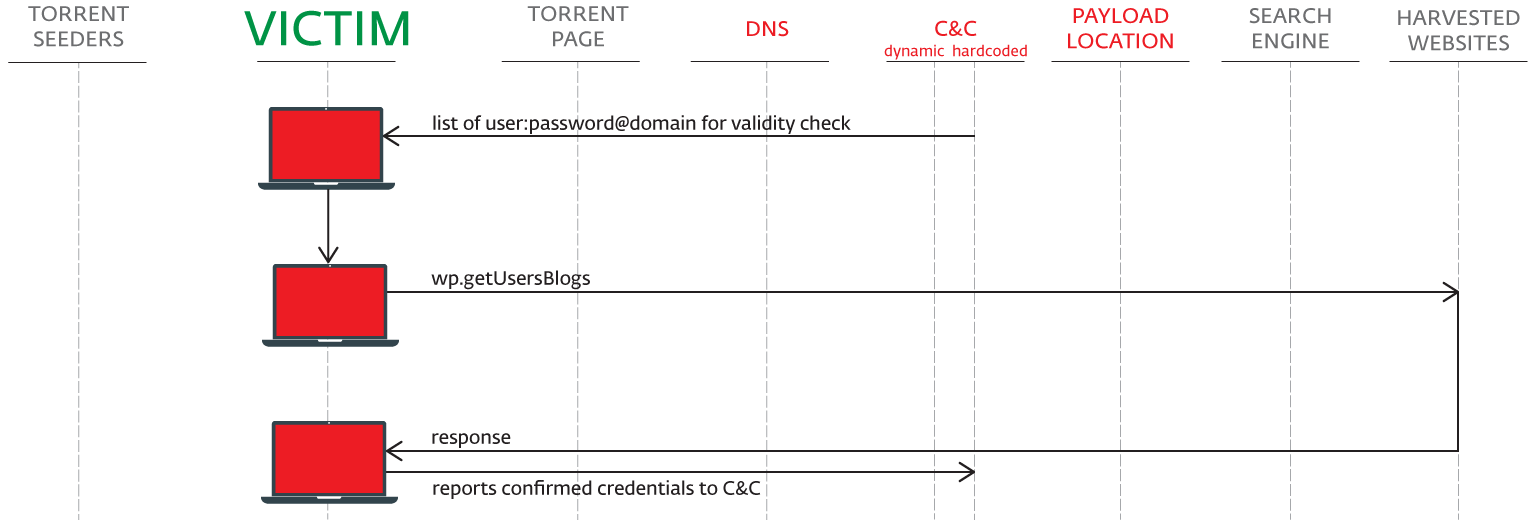
In the course of the study, a list of 10,000 domains was sent to the C & C managing server for verification.

The attacks use the XML-RPC API:
Distribution
Sathurbot is equipped with the libtorrent library. After infection, computers in the botnet can also distribute malicious torrents.
Bots have different tasks - some computers collect data, others attack the XML-RPC API, some perform both actions.
Results
According to our data, the Sathurbot botnet includes more than 20,000 infected computers and is valid from June 2016.
Numerous attacks via /wp-login.php (even on sites that do not use WordPress) are a direct result of Sathurbot activity. Operators also use wp.getUsersBlogs XMLRPC. We have seen and spread links to malicious torrent in email.
Users of ESET NOD32 anti-virus products are protected from this threat.
Detection
Network administrators: check unknown sub-pages and / or directories on the server. If they contain links to download torrents, check the logs for attacks.
Users: run Wireshark with the http.request filter to see requests of the type GET / wp-login.php and / or POST /xmlrpc.php.
Check the files or registry entries listed in the Infection Indicators section.
Deletion
Network administrators: change passwords, delete sub-pages that are not related to the site, (optionally) restore the site from a backup.
Users: find a suspicious DLL using a third-party file manager, open the Process Explorer or Task Manager, terminate explorer.exe and / or rundll32.exe, delete (quarantine) the affected DLL, restart the computer.
Note. This will remove Sathurbot, but not other malware that it may have downloaded. Alternatively, use a comprehensive anti-malware product or at least an online scanner.
Prevention
Network administrators: if the site does not require XML-RPC, disable it and use complex passwords.
Users: Avoid running executable files besides those released by famous developers; Do not download torrents from sites that are not intended for file sharing.
Infection indicators
We are currently seeing Sathurbot's installation:
\ ProgramData \ Microsoft \ Performance \ Monitor \ PerformanceMonitor.dll
\ ProgramData \ Microsoft \ Performance \ TheftProtection \ TheftProtection.dll
\ ProgramData \ Microsoft \ Performance \ Monitor \ SecurityHelper.dll
\ Users \ ***** \ AppData \ Local \ Microsoft \ Protect \ protecthost.dll
Runs in the context of rundll32.exe or explorer.exe processes and blocks editing of files and registry keys. There are 32 and 64-bit versions.
Attached folders with torrent files downloaded:
\ SecurityCache \ cache \ resume \
\ SecurityCache \ cache \ rules \
\ SecurityCache \ data \
\ SecurityCache \ zepplauncher.mif - contains DHT nodes
\ temp \
% appdata% \ SYSHashTable \ - contains folders with hashes of visited domains% appdata% \ SYSHashTable \ SyshashInfo.db - a set of target domains, including information about the structure
Samples (SHA-1)
Installers:
2D9AFB96EAFBCFCDD8E1CAFF492BFCF0488E6B8C
3D08D416284E9C9C4FF36F474C9D46F3601652D5
512789C90D76785C061A88A0B92F5F5778E80BAA
735C8A382400C985B85D27C67369EF4E7ED30135
798755794D124D00EAB65653442957614400D71D
4F52A4A5BA897F055393174B3DFCA1D022416B88
8EDFE9667ECFE469BF88A5A5EBBB9A75334A48B9
5B45731C6BBA7359770D99124183E8D80548B64F
C0F8C75110123BEE7DB5CA3503C3F5A50A1A055E
C8A514B0309BCDE73F7E28EB72EB6CB3ABE24FDD
AF1AE760F055120CA658D20A21E4B14244BC047D
A1C515B965FB0DED176A0F38C811E6423D9FFD86
B9067085701B206D2AC180E82D5BC68EDD584A8B
77625ADEA198F6756E5D7C613811A5864E9874EA
Sathurbot dll:
F3A265D4209F3E7E6013CA4524E02D19AAC951D9
0EA717E23D70040011BD8BD0BF1FFAAF071DA22C
2381686708174BC5DE2F04704491B331EE9D630B
2B942C57CEE7E2E984EE10F4173F472DB6C15256
2F4FAA5CB5703004CA68865D8D5DACBA35402DE4
4EBC55FDFB4A1DD22E7D329E6EF8C7F27E650B34
0EF3ECD8597CE799715233C8BA52D677E98ABDFD
0307BBAC69C54488C124235449675A0F4B0CCEFA
149518FB8DE56A34B1CA2D66731126CF197958C3
3809C52343A8F3A3597898C9106BA72DB7F6A3CB
4A69B1B1191C9E4BC465F72D76FE45C77A5CB4B0
5CCDB41A34ADA906635CE2EE1AB4615A1AFCB2F2
6C03F7A9F826BB3A75C3946E3EF75BFC19E14683
8DA0DC48AFB8D2D1E9F485029D1800173774C837
AC7D8140A8527B8F7EE6788C128AFF4CA92E82C2
E1286F8AE85EB8BD1B6BE4684E3C9E4B88D300DB
Additional payload:
C439FC24CAFA3C8008FC01B6F4C39F6010CE32B6
ABA9578AB2588758AD34C3955C06CD2765BFDF68
DFB48B12823E23C52DAE03EE4F7B9B5C9E9FDF92
FAFF56D95F06FE4DA8ED433985FA2E91B94EE9AD
B728EB975CF7FDD484FCBCFFE1D75E4F668F842F
59189ABE0C6C73B66944795A2EF5A2884715772E
C6BDB2DC6A48136E208279587EFA6A9DD70A3FAA
BEAA3159DBE46172FC79E8732C00F286B120E720
5ED0DF92174B62002E6203801A58FE665EF17B76
70DFABA5F98B5EBC471896B792BBEF4DB4B07C53
10F92B962D76E938C154DC7CBD7DEFE97498AB1E
426F9542D0DDA1C0FF8D2F4CB0D74A1594967636
AA2176834BA49B6A9901013645C84C64478AA931
1C274E18A8CAD814E0094C63405D461E815D736A
61384C0F690036E808F5988B5F06FD2D07A87454
F32D42EF1E5ED221D478CFAA1A76BB2E9E93A0C1
594E098E9787EB8B7C13243D0EDF6812F34D0FBA
1AAFEBAA11424B65ED48C68CDEED88F34136B8DC
BA4F20D1C821B81BC324416324BA7605953D0605
E08C36B122C5E8E561A4DE733EBB8F6AE3172BF0
7748115AF04F9FD477041CB40B4C5048464CE43E
3065C1098B5C3FC15C783CDDE38A14DFA2E005E4
FA25E212F77A06C0B7A62C6B7C86643660B24DDA
FADADFFA8F5351794BC5DCABE301157A4A2EBBCF
B0692A03D79CD2EA7622D3A784A1711ADAABEE8D
9411991DCF1B4ED9002D9381083DE714866AEA00
Domains:
DNS:
zeusgreekmaster.xyz
apollogreekmaster.xyz
C & C:
jhkabmasdjm2asdu7gjaysgddasd.xyz
boomboomboomway.xyz
mrslavelemmiwinkstwo.xyz
uromatalieslave.space
newforceddomainisherenow.club
justanotherforcedomain.xyz
artemisoslave.xyz
asxdq2saxadsdawdq2sasaddfsdfsf4ssfuckk.xyz
kjaskdhkaudhsnkq3uhaksjndkud3asds.xyz
badaboommail.xyz
Torrent trackers:
badaboomsharetracker.xyz
webdatasourcetraffic.xyz
sharetorrentsonlinetracker.xyz
webtrafficsuccess.xyz
Registry settings
You may need a third-party tool, because Windows Regedit does not display this:
HKLM \ SYSTEM \ CurrentControlSet \ services \ SharedAccess \ Parameters \ FirewallPolicy \ FirewallRules \ {variable GUID} = “v2.10 | Action = Allow | Active = TRUE | Dir = In | Profile = Private | Profile = Public | App = C: \\ Windows \\ explorer.exe | Name = Windows Explorer | ”
HKLM \ SYSTEM \ CurrentControlSet \ services \ SharedAccess \ Parameters \ FirewallPolicy \ FirewallRules \ {variable GUID} = “v2.10 | Action = Allow | Active = TRUE | Dir = In | Profile = Private | Profile = Public | App = C: \\ Windows \\ system32 \\ rundll32.exe | Name = Windows host process (Rundll32) | ”
HKLM \ SOFTWARE \ Microsoft \ Windows \ CurrentVersion \ Explorer \ ShellIconOverlayIdentifiers \ 0TheftProtectionDll = {GUID1}
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} = “Windows Theft Protection”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} \ InprocServer32 = “C: \\ ProgramData \\ Microsoft \\ Performance \\ TheftProtection \\ TheftProtection.dll”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID1} \ InprocServer32 \ ThreadingModel = “Apartment”
HKLM \ SOFTWARE \ Classes \ CLSID \ {GUID2}
{GUID2} records vary in all samples, contain six long subkeys, the content is binary type and is encrypted. Used to store variables, temporary values and IP, C & C, UID settings.
For example, {GUID2} looks like this:
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000003
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000002
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000001
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000009
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000011
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00010001
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00010002
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000008
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000007
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000004
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00000010
HKLM \ SOFTWARE \ Classes \ CLSID \ {8E577F7E-03C2-47D1-B4C0-BCE085F78F66} \ 00020001
Source: https://habr.com/ru/post/326198/
All Articles