November 2 - the most IT day of the year
For a couple of years I have been following the birthdays of key (and at the same time not very key) people in the field of information technology and computer science. November 2 - the most concentrated day of "my IT calendar" - as many as 6 birthday people: Irish, Hindu, Ukrainian, two Russians and "American." 83, (3)% of them are human.

Let the Happy Birthday post begin.
"Pure mathematics was discovered by Boolee in the work he called 'The Laws of Thinking'."
- Bertrand Russell
')
Founding father of mathematical logic and computer science. In his honor, named the type of the variable Boolean in programming. Last year celebrated the 200th anniversary.
Two systematic treatises were created on mathematical topics by Boolem during life: "Treatise on differential equations" and "Treatise on finite differences". These works have made important contributions to the relevant sections of mathematics and at the same time have shown Buhl’s deep understanding of the philosophy of his subject.
"An Investigation of the Laws of Thought"


The founder of computer technology in the USSR. Under his leadership, the first Small Electronic Calculating Machine (MESM) was developed in the USSR and continental Europe.

Under his leadership, 15 types of computers were created, starting with the tube (BESM-1, BESM-2, M-20) and ending with modern supercomputers on integrated circuits.

Deserved the Kolmogorov Medal and the Knut Award .
Regardless of Steven Cook, he proved in 1971 the Cook – Levine theorem, thanks to which the problem of the equality of the classes P and NP was formulated, which became one of the millennium problems.
The Cook – Levine theorem states that the problem of the satisfiability of a Boolean formula in a CNF ( SAT ) is NP-complete .

Legendary and controversial character. Severe hacker character was tempered in the dashing 80-90s. He started with Fido and "showdown" with the "real" Kaspersky. Since 2008 he has been living and working (at McAfee) in the USA.
In 2008, he published 16 books on information protection and program optimization, computer viruses and disassembling. Also among the books - "Encyclopedia will take the weather."

He loved to quote Dune.
Speaking of worms.

It was the first virus to receive considerable attention in the media.
He also led to a first conviction in the United States on the 1986 Computer Fraud and Abuse Act.

Indian Mitnick, a young Hindu hacker prolific to books, protects the government, the police and the Indian bureau of inquiry.
Hacking TALK with Trishneet Arora, The Hacking Era, Hacking With Smart Phones
Happy birthday, guys!
Publication support is the Edison company, which develops CAD systems for electrical power systems , as well as assists the research institute with the implementation of a software module containing a mathematical neural network algorithm for image recognition .

Let the Happy Birthday post begin.
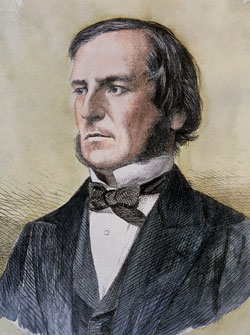
George Boole , 1815
"Pure mathematics was discovered by Boolee in the work he called 'The Laws of Thinking'."
- Bertrand Russell
')
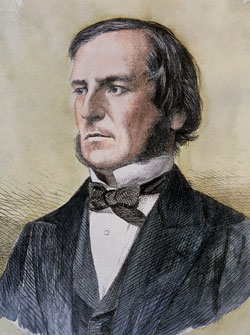
Founding father of mathematical logic and computer science. In his honor, named the type of the variable Boolean in programming. Last year celebrated the 200th anniversary.
Two systematic treatises were created on mathematical topics by Boolem during life: "Treatise on differential equations" and "Treatise on finite differences". These works have made important contributions to the relevant sections of mathematics and at the same time have shown Buhl’s deep understanding of the philosophy of his subject.
"An Investigation of the Laws of Thought"

Sergey Lebedev , 1902

The founder of computer technology in the USSR. Under his leadership, the first Small Electronic Calculating Machine (MESM) was developed in the USSR and continental Europe.

Under his leadership, 15 types of computers were created, starting with the tube (BESM-1, BESM-2, M-20) and ending with modern supercomputers on integrated circuits.
Leonid Levin , 1948

Deserved the Kolmogorov Medal and the Knut Award .
Regardless of Steven Cook, he proved in 1971 the Cook – Levine theorem, thanks to which the problem of the equality of the classes P and NP was formulated, which became one of the millennium problems.
The Cook – Levine theorem states that the problem of the satisfiability of a Boolean formula in a CNF ( SAT ) is NP-complete .
Read more
- 2012 Knut Prize awarded to Leonid Levin
- Interview with Leonid Levin (about Kolmogorov, Kolmogorov complexity, etc.)
- Computer Science Award for natives of the USSR
- L. A. Levin: Universal brute force problems
Chris Kaspersky (Nikolai Likhachev), 1976

Legendary and controversial character. Severe hacker character was tempered in the dashing 80-90s. He started with Fido and "showdown" with the "real" Kaspersky. Since 2008 he has been living and working (at McAfee) in the USA.
In 2008, he published 16 books on information protection and program optimization, computer viruses and disassembling. Also among the books - "Encyclopedia will take the weather."

Book list
- Technique and philosophy of hacker attacks.
- The mindset is a disassembler.
- Technique of network attacks.
- Fundamentals of hacking. The art of disassembling.
- Notes virus researcher computer.
- Encyclopedia will take the weather. Local weather prediction.
- Hacker Disassembling Uncovered.
- Shellcoder's Programming Uncovered.
- Data Recovery Tips & Solutions: Windows, Linux, and BSD.
- CD Cracking Uncovered Protection Against Unsanctioned.
- CD Cracking Uncovered: Protection Against Unsanctioned CD Copying.
- Hacker Debugging Uncovered.
- Code Optimization: Effective Memory Usage.
He loved to quote Dune.
Speaking of worms.
Morris worm , 1988

It was the first virus to receive considerable attention in the media.
He also led to a first conviction in the United States on the 1986 Computer Fraud and Abuse Act.
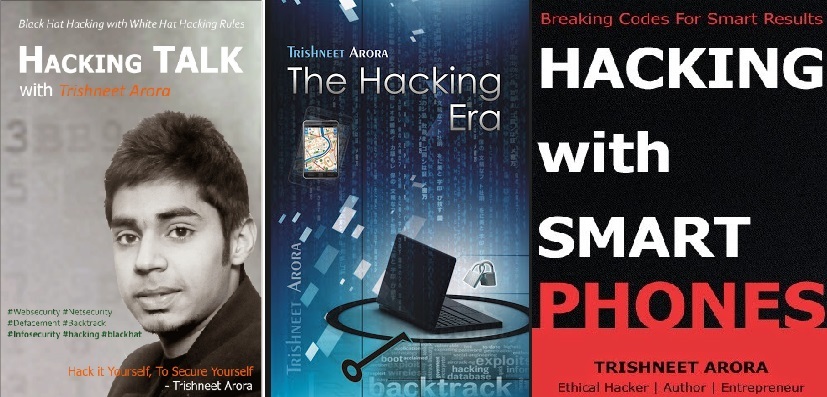
Trishneet Arora , 1993

Indian Mitnick, a young Hindu hacker prolific to books, protects the government, the police and the Indian bureau of inquiry.
Hacking TALK with Trishneet Arora, The Hacking Era, Hacking With Smart Phones
Video hacker
Happy birthday, guys!
Publication support is the Edison company, which develops CAD systems for electrical power systems , as well as assists the research institute with the implementation of a software module containing a mathematical neural network algorithm for image recognition .
Source: https://habr.com/ru/post/314206/
All Articles