Alloy Discovery: the all-seeing eye of the system administrator
The more computers on the network, the more troublesome the life of a system administrator, who is also made more difficult by advanced users who install their own hardware, software, and even change the hardware configuration with malicious or good intention. When computers become too many or they are located too far, there is a need for conducting a periodic audit of the network. There are many tools that can carry out or facilitate an audit, but few of them solve the problem in a comprehensive manner and cover all the needs of the engineer. The Alloy Software team has created a software solution aimed at a thorough audit. How, and most importantly, why it works, we will tell in the post.

In any company with a more or less large fleet of computers, there is a need to analyze the state of each machine in the network. What is it for?
These tasks require an operational solution, which is guaranteed by specialized software that meets the above requirements.
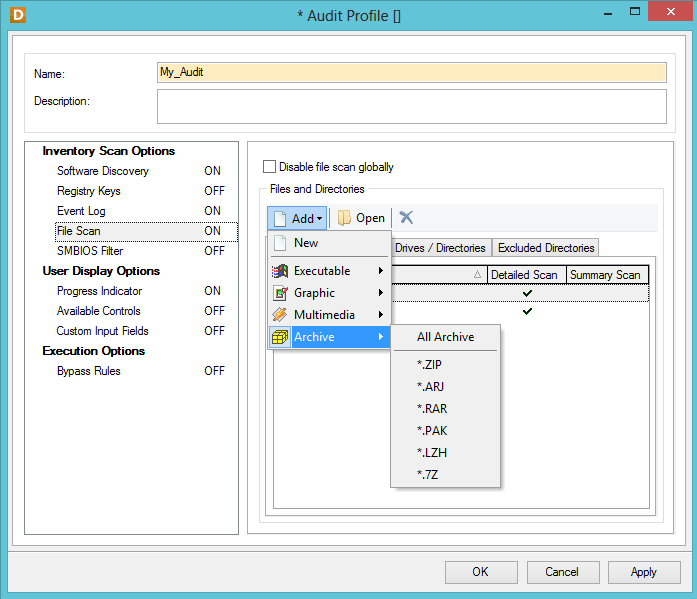
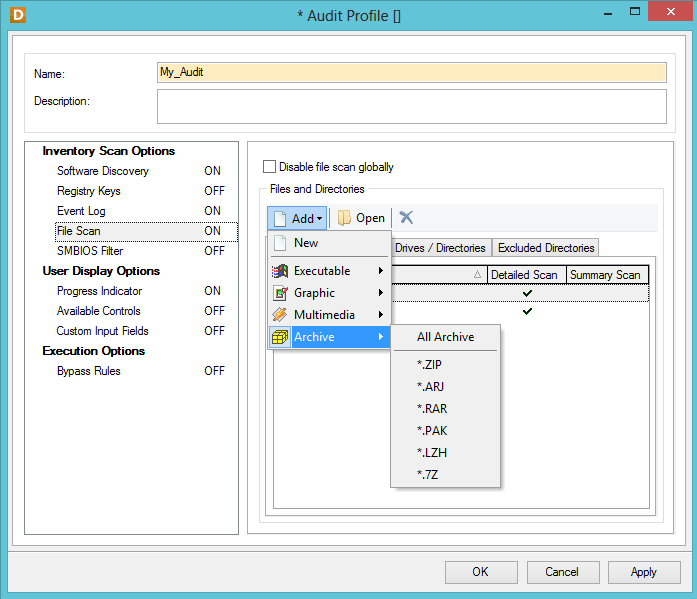
With the help of Alloy Discovery, you can audit an individual computer or device, and you can audit an entire network. The solution provides a flexible configuration of audit agents for various scenarios: single- and multi-domain networks, networks for individual work groups, remote computers on the Internet, isolated DMZ networks, and computers not connected to the network. Audit parameters are finely tuned. If necessary, you can create a custom audit profile with the included scanning of events, installation files, executable files, graphic, audio and video files, archives. However, the ability to scan files is available only for computers running Windows.
Based on the results of each audit, the maximum set of characteristics is determined for each computer in the network:
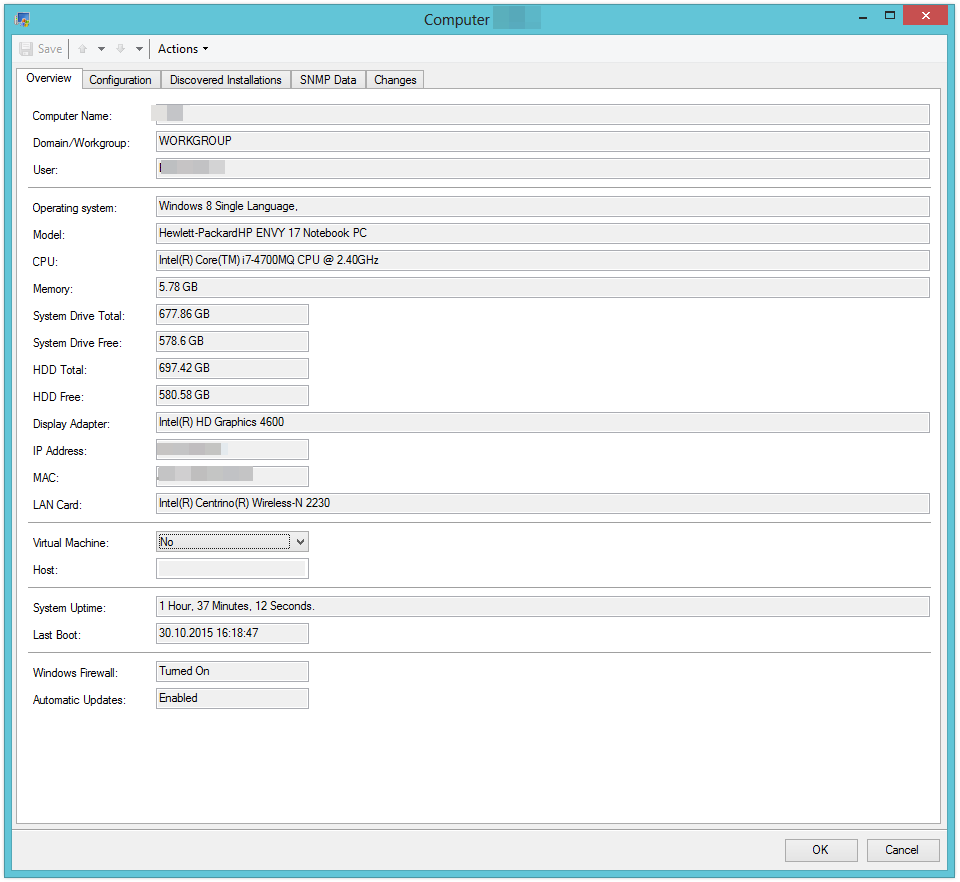
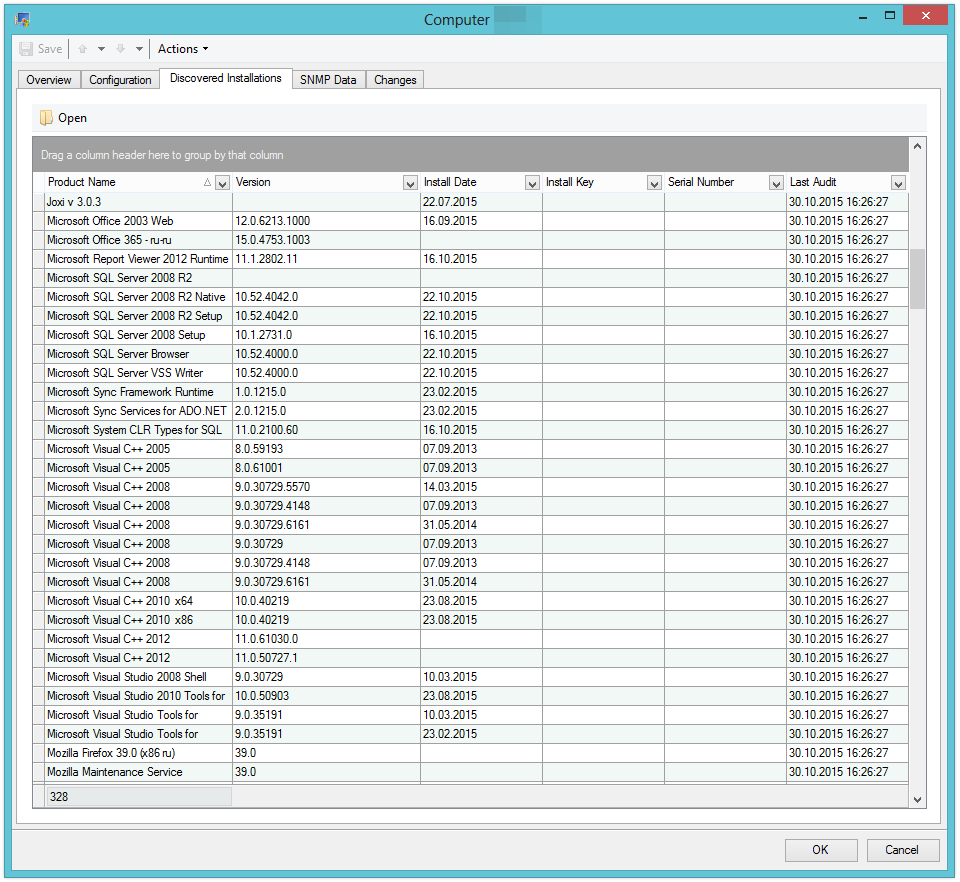
The programs installed on each machine are scanned and determined, including the name, version, installation date, installation key, serial number and date of the last check (audit). The changes section records the facts of installing and uninstalling software that occurred during the period between audits. In the “SNMP Data” section, Alloy Discovery stores data received from the device being audited via the SNMP protocol. This data is most relevant to printers, scanners, switches, routers, and other network devices. The information collected contains the make, model and serial number of the device.
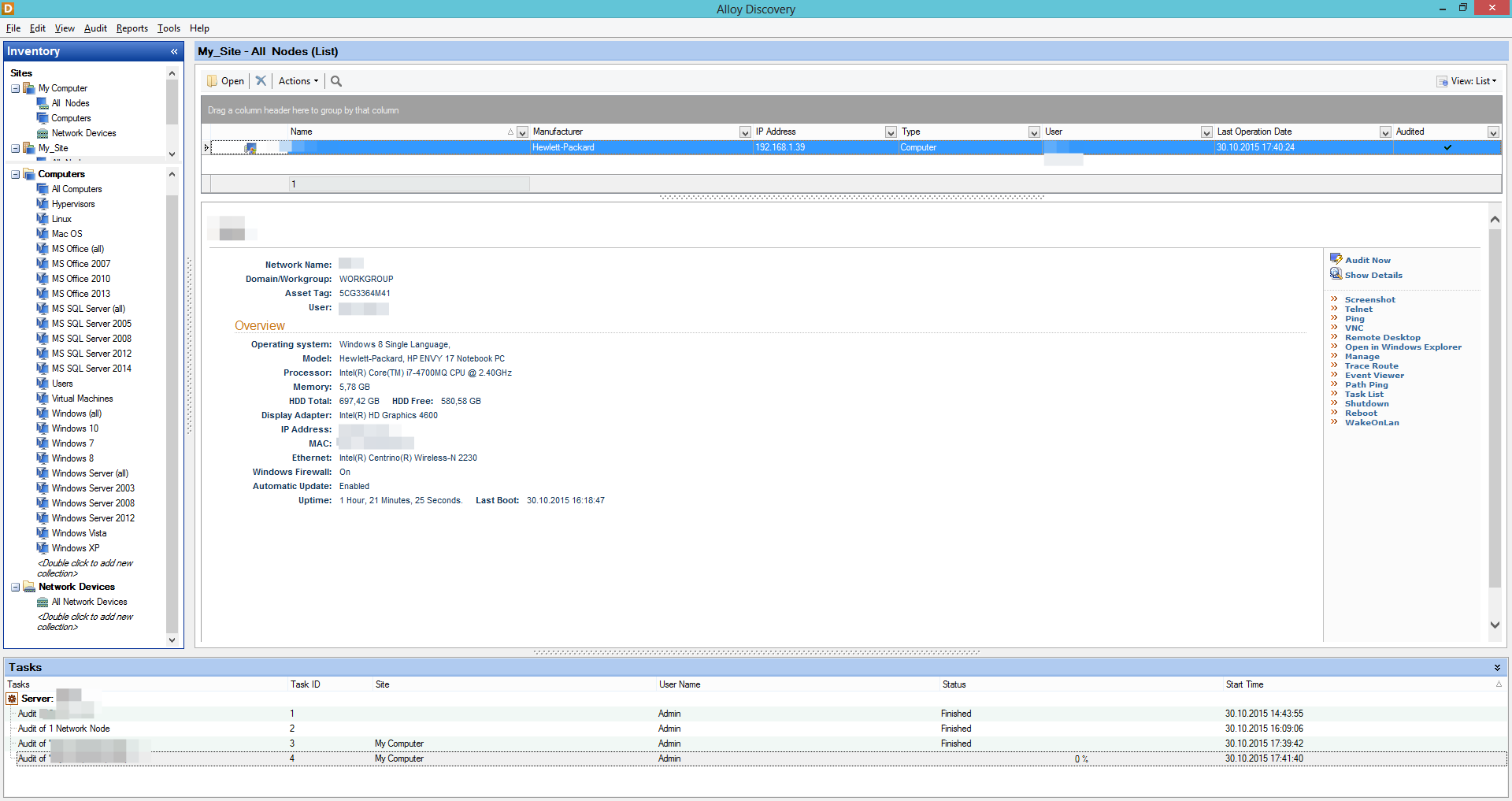
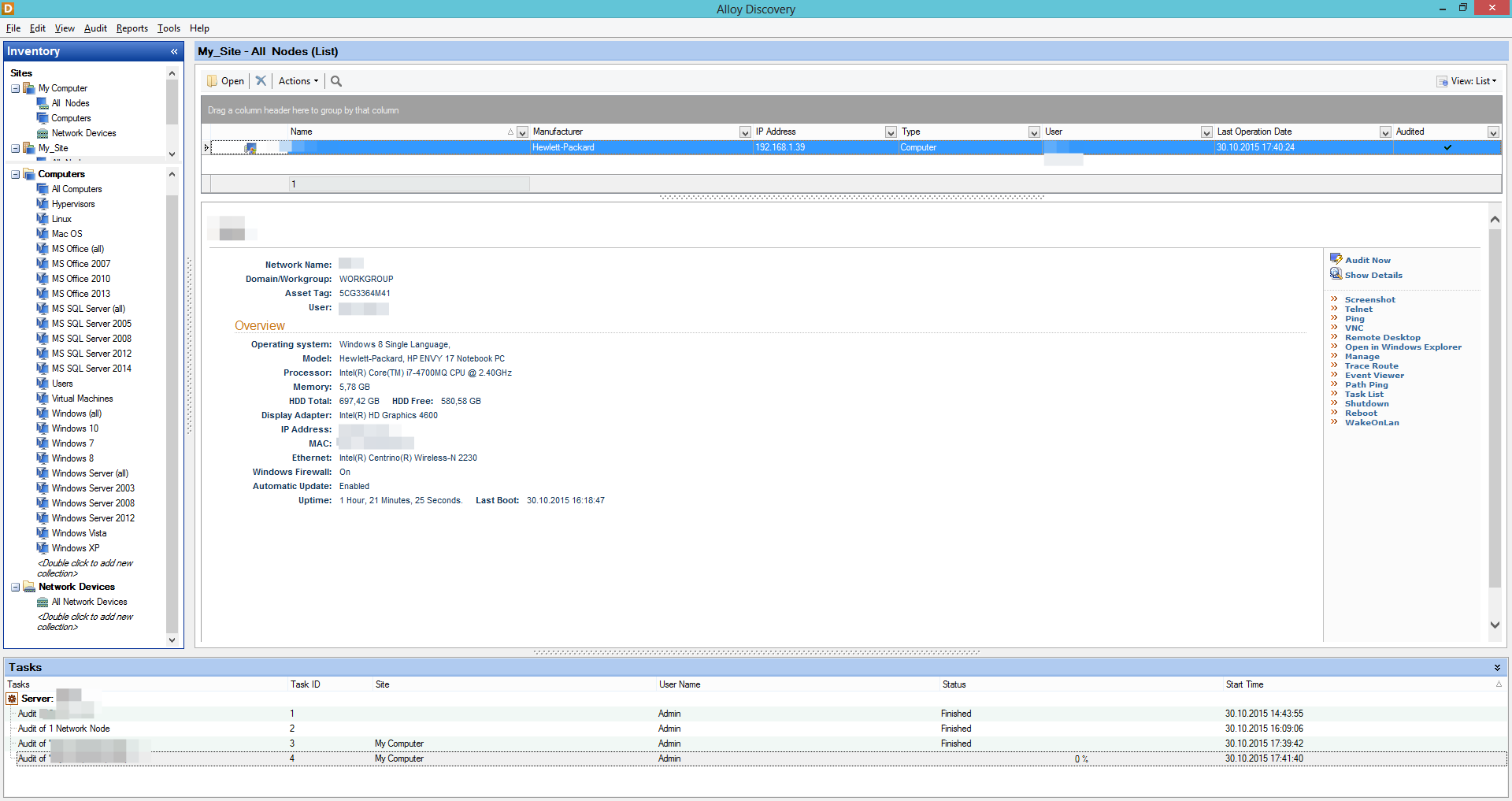
All audit actions are displayed in real time and logged at the same time, so all changes between audits are recorded. Each selected computer is additionally displayed in the form of a card with basic information: operating system, device model, processor, memory, HDD, IP address, MAC address, network connection.
The convenient left menu contains the tools for managing the selected computer: Alloy Remote Screenshot Tool, Telnet, Ping, VNC, Remote Desktop, Trace Route, Event Viewer, Shutdown, Reboot, WakeOnLan, and so on.
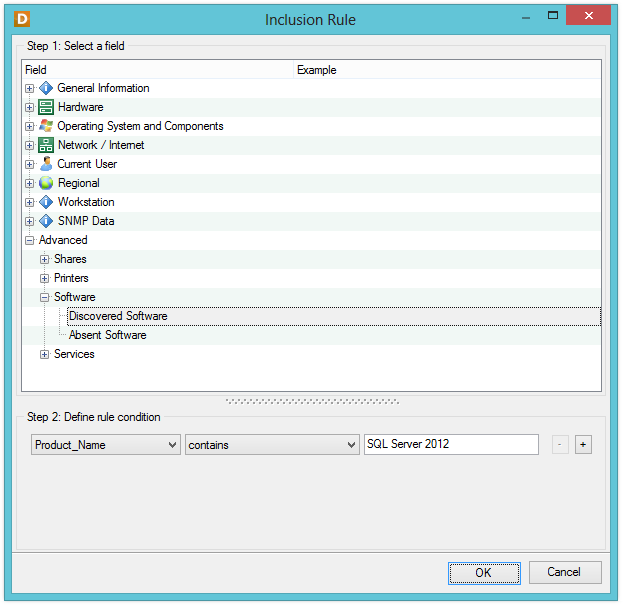
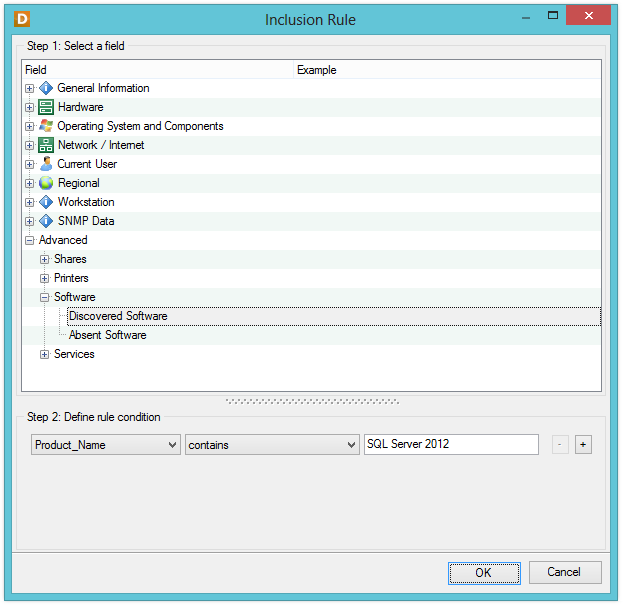
For further convenience of working with data, the administrator can configure the desktop as a dashboard with a customized sidebar. In the sidebar, groups are created according to the specified parameters, into which the audit data is then distributed to the specified filter values. The grouping criterion is specified by setting rules for a large number of parameters. Thus, you can create user groups for the most complex compound expressions: for example, you can separately track computers in the Vologda branch that have MS SQL Server installed, a given CRM and a client-bank USB token connected, or track a computer by user or email . It is very simple to create all the rules: just select the desired parameter, the logical operator from the list and set the desired value.
You can create inventory barcodes for each computer and mark them with machines, which will greatly facilitate the task of inventory in the future.
For companies with a fleet of computers on a network of less than 2,000 machines, we offer Alloy Discovery Express . This is an architecturally simpler solution: a single-user application with a local repository, as opposed to a multi-user environment based on Microsoft SQL Server in the Enterprise version, designed for 10,000 machines on the network.
At the same time, the differences between Express are limited by the lack of functionality that is in demand only in truly large-scale companies with geographically distributed branches:
The rest of the functionality is no different from Enterprise.
Audit parameters are set using a convenient wizard. You can choose the type of group you want to create: an audit group or a group of computers over which the distributed test results will be.
In the case of creating audit groups, you can choose audit options: by domain, IP address, using automated audit scripts, via e-mail for a remote network, using external tools. For domain type groups, you can choose how the computers in the group will be monitored: only Active Directory (including computers turned off and unavailable on the network), Network Browser (for new computers on the network), or both. Then, access and connection settings to devices using the SNMP protocol are set.
Creation of computer groups is intended for analyzing static slices of the state of devices and PCs monitored during the audit (snapshots). In the wizard, you can create a static group in which computers are added and removed manually and a dynamic group with automatic addition of computers according to the established criteria. In the case of a dynamic group, the administrator prescribes the rules according to which computers should be added to one or another cluster. Rules are written using common logic.

After monitoring, similarly to Enterprise, the machines in the network are distributed to user-defined groups, and the administrator can see the most detailed information about each inspected machine.
Both editions of Alloy Discovery easily solve the problem of auditing remote computers and computers outside the network. There are several ways to perform an audit for this:
Alloy Discovery is designed for companies that maintain their own IT-park or have several clients in service. With it, you can solve the most complex audit tasks, maintain comprehensive accounting of PCs and peripherals, track user actions that are important for business processes. Despite the English-language interface, the program is limited to a standard technical dictionary and is understandable to almost everyone who has come across technical English. In addition, the input fields support the Russian language. Using Alloy Discovery ensures that the mouse does not slip into your IT park without the knowledge of the system administrator. Well, that is, it will not connect.

In any company with a more or less large fleet of computers, there is a need to analyze the state of each machine in the network. What is it for?
- First of all, for accounting equipment - it is important to monitor the status of workstations and computers on the network in order to respond quickly to problems, replace outdated equipment and maintain stable operation of the IT infrastructure.
') - To control the installed software and prevent the installation of unlicensed software. Sometimes it is important to keep track of the set of installed programs if company policy provides for such control.
- It is necessary to check the connection of peripheral devices, printers, routers and other office equipment. In some cases, it is critical to check the presence of connected external storage devices.
- Control of network configurations and connections is required.
- It is necessary to monitor the state of computers located at a geographic distance: in branches, branch offices, at service points, etc.
- Finally, an inventory of the PC and related devices is periodically reviewed. In large or geographically distributed companies, this process is labor-intensive.
These tasks require an operational solution, which is guaranteed by specialized software that meets the above requirements.
- Before proceeding with the detailed review, we will briefly list what the Alloy Discovery complex can do.
- Collect detailed information about computers and devices on the network.
- Audit remote servers and computers running Linux and Mac without installing agent applications. On Windows, the agent application is installed at the time of the remote audit, and then immediately removed.
- Remote control of computers and network devices.
- Audit of remote networks and sites with mailing the results.
- Audit of non-networked computers using removable media.
- Analysis of the collected information using the methods of dynamic filtering, grouping and sorting data.
Alloy Discovery Overview
With the help of Alloy Discovery, you can audit an individual computer or device, and you can audit an entire network. The solution provides a flexible configuration of audit agents for various scenarios: single- and multi-domain networks, networks for individual work groups, remote computers on the Internet, isolated DMZ networks, and computers not connected to the network. Audit parameters are finely tuned. If necessary, you can create a custom audit profile with the included scanning of events, installation files, executable files, graphic, audio and video files, archives. However, the ability to scan files is available only for computers running Windows.
Based on the results of each audit, the maximum set of characteristics is determined for each computer in the network:
- all system and hardware specifications
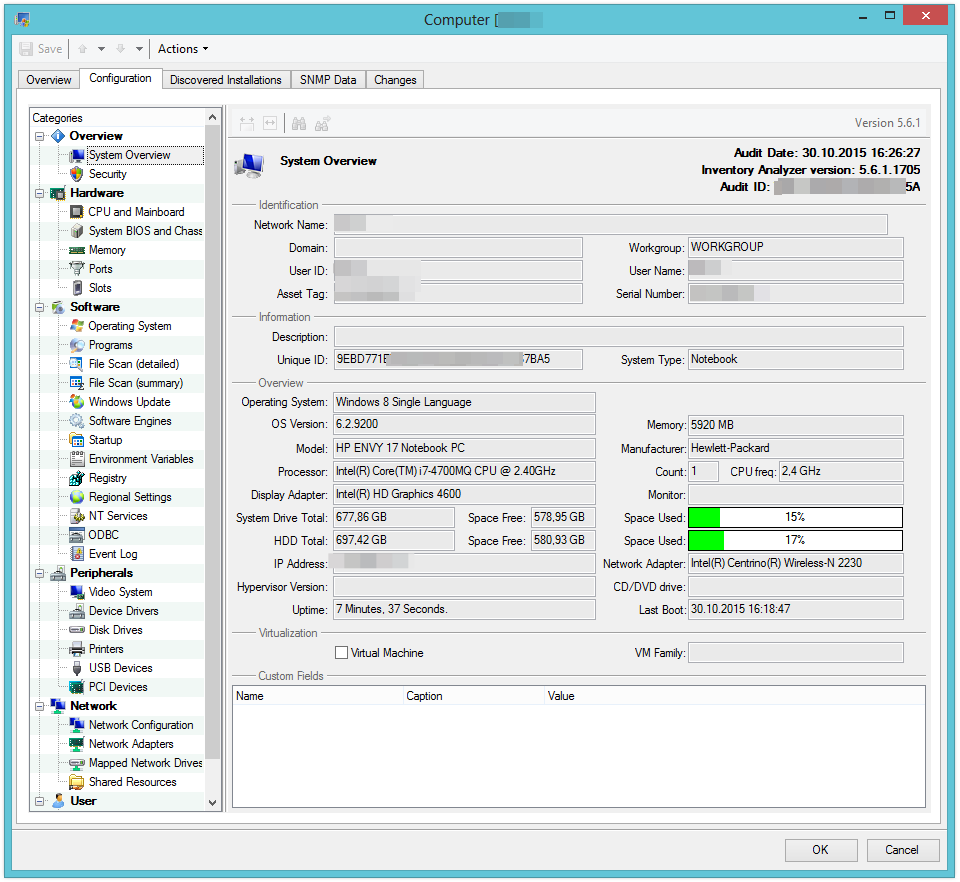
- security settings
- profiles of the operating system used and software installed with version IDs, vendors and installation dates
- data scan files on your computer (multimedia, executable, installation)
- state and parameters of peripheral devices
- network connection settings
- information about users and user accounts.
The programs installed on each machine are scanned and determined, including the name, version, installation date, installation key, serial number and date of the last check (audit). The changes section records the facts of installing and uninstalling software that occurred during the period between audits. In the “SNMP Data” section, Alloy Discovery stores data received from the device being audited via the SNMP protocol. This data is most relevant to printers, scanners, switches, routers, and other network devices. The information collected contains the make, model and serial number of the device.
All audit actions are displayed in real time and logged at the same time, so all changes between audits are recorded. Each selected computer is additionally displayed in the form of a card with basic information: operating system, device model, processor, memory, HDD, IP address, MAC address, network connection.
The convenient left menu contains the tools for managing the selected computer: Alloy Remote Screenshot Tool, Telnet, Ping, VNC, Remote Desktop, Trace Route, Event Viewer, Shutdown, Reboot, WakeOnLan, and so on.
For further convenience of working with data, the administrator can configure the desktop as a dashboard with a customized sidebar. In the sidebar, groups are created according to the specified parameters, into which the audit data is then distributed to the specified filter values. The grouping criterion is specified by setting rules for a large number of parameters. Thus, you can create user groups for the most complex compound expressions: for example, you can separately track computers in the Vologda branch that have MS SQL Server installed, a given CRM and a client-bank USB token connected, or track a computer by user or email . It is very simple to create all the rules: just select the desired parameter, the logical operator from the list and set the desired value.
You can create inventory barcodes for each computer and mark them with machines, which will greatly facilitate the task of inventory in the future.
The younger and very strong brother - Alloy Discovery Express
For companies with a fleet of computers on a network of less than 2,000 machines, we offer Alloy Discovery Express . This is an architecturally simpler solution: a single-user application with a local repository, as opposed to a multi-user environment based on Microsoft SQL Server in the Enterprise version, designed for 10,000 machines on the network.
At the same time, the differences between Express are limited by the lack of functionality that is in demand only in truly large-scale companies with geographically distributed branches:
- planned audit is not provided using various settings and several schedules
- the catalog of installed programs is not collected, the log of installed, remote and updated programs is not kept
- There are no administrative alerts when new programs are detected.
- multiple server inventory cannot be installed
- Integration with MS Report Designer and Crystal Reports is not provided, field names are not configured, standard values are used.
The rest of the functionality is no different from Enterprise.
Audit parameters are set using a convenient wizard. You can choose the type of group you want to create: an audit group or a group of computers over which the distributed test results will be.
In the case of creating audit groups, you can choose audit options: by domain, IP address, using automated audit scripts, via e-mail for a remote network, using external tools. For domain type groups, you can choose how the computers in the group will be monitored: only Active Directory (including computers turned off and unavailable on the network), Network Browser (for new computers on the network), or both. Then, access and connection settings to devices using the SNMP protocol are set.
Creation of computer groups is intended for analyzing static slices of the state of devices and PCs monitored during the audit (snapshots). In the wizard, you can create a static group in which computers are added and removed manually and a dynamic group with automatic addition of computers according to the established criteria. In the case of a dynamic group, the administrator prescribes the rules according to which computers should be added to one or another cluster. Rules are written using common logic.

After monitoring, similarly to Enterprise, the machines in the network are distributed to user-defined groups, and the administrator can see the most detailed information about each inspected machine.
Both editions of Alloy Discovery easily solve the problem of auditing remote computers and computers outside the network. There are several ways to perform an audit for this:
- audit of computers in the network;
- audit of remote networks and sites with sending the results by mail;
- audit of non-networked computers using removable media.
Alloy Discovery is designed for companies that maintain their own IT-park or have several clients in service. With it, you can solve the most complex audit tasks, maintain comprehensive accounting of PCs and peripherals, track user actions that are important for business processes. Despite the English-language interface, the program is limited to a standard technical dictionary and is understandable to almost everyone who has come across technical English. In addition, the input fields support the Russian language. Using Alloy Discovery ensures that the mouse does not slip into your IT park without the knowledge of the system administrator. Well, that is, it will not connect.
Source: https://habr.com/ru/post/271137/
All Articles