Setting up a Mikrotik router for various tasks in SOHO
This article is a tracing paper with an internal instruction written by me personally, according to which we set up new routers in the company. The points will be arranged in a more or less chronological order, but each of them is an independent mini-instruction to one of the services used in our company.
First you need to connect to the device. By default, the configuration on the router is configured on the

Launch
')
Double click the mouse on the MAC address and connect as
When you first log in, the system will warn you that an automatic router configuration script has been launched. Click the
After that, we wait until the
Having connected, we select

Go to
Go to the
For external interfaces, we specify 11.11.11.11 with a distance of 4 and 22.22.22.22 with a distance of 3 as gateways.

After adding three routes (2 for external channels and 1 for the internal network), the router can be connected to the network and connected via IP 192.168.3.101 using the internal IP.
The configuration created above allows you to create 2 external interfaces, of which only one can work per unit of time — that is, the one that has a smaller distance and that has more distance — will work only when the cable is pulled out of the first interface. For obvious reasons, this does not suit us - we need the simultaneous operation of two gateways. To do this, you need to teach the router to return traffic to the interface from which the request came. This is done by creating two additional routes and setting up a firewall. First, create the necessary routes. Previously created routes will also be useful, but you can clone them, because they will change slightly. To do this, click on the route created earlier, click the

Next, go to
Create rules:
These actions must be repeated twice - for 2 external interfaces (brand
Next, you need to create 2 more rules that will direct outgoing traffic marked
So, we have achieved the presence of two simultaneously working gateways, one of which has the highest priority than the second. The problem with this setting is that switching between gateways will be done only when the physical link on the device interface is dropped. But there are other situations as well: there is no more money in the account, problems on the provider side and so on - situations in which even the main gateway is available, but there is no further traffic and in this case the main gateway will not be switched. For auto-
Go to the
Go to
Create a new rule:
Before each of the hosts (8.8.8.8 and 8.8.4.4), we prescribe a unique route with a reduced distance through different gateways (11.11.11.11 and 22.22.22.22).
You can check the operation of
Go to the
Create 2 rules for each of the external interfaces:
You can check NAT by pinging one of the websites on the Internet from a computer connected to the internal interface of the router. If you disable one of the two rules of NAT on the router, you can see how the trace to the selected host on the Internet changes.
In the company's network, it was decided to use the subnet 192.168.168.0/22, with client addressing starting with 192.168.170.2 and the gateway address (of the router itself) 192.168.170.1
Go to the
Go to the
Go to the
Go to the
For batch creation of secrets (accounts) VPN, you can use the script.
You need to go to the

After creating the script, it is enough to create a file in which to adhere to the following syntax:
Please note that the last line is empty. If it is not left empty, the last filled line will not be processed.
Next you need to open the menu item
After these preparations, you can go to

As a result of the script, in
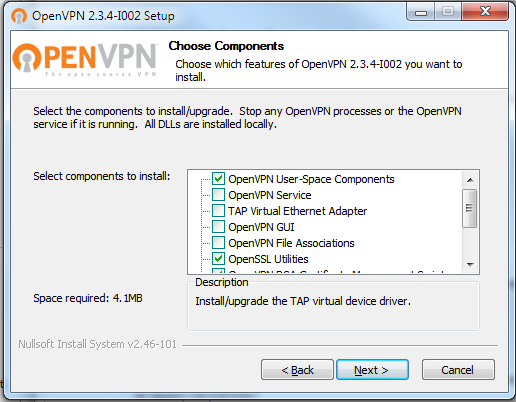
SSTP requires certificates. I used self-signed certificates issued by the OpenVPN snap-in . To obtain certificates you do not need to put all the components
Next, run cmd on behalf of the administrator and go to the
Next, I cleanly edited the
After that, run in the following sequence:
You can just press enter to the questions of the last command in (the data entered in the
In the
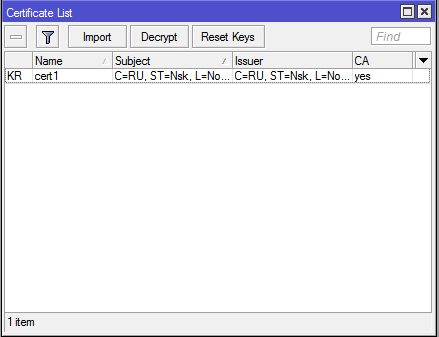
Next in
Go to the
For the profile name, specify
Then, in the
Since when creating secrets (logins / passwords) for
Since this article is about configuring a router, and not a client, I will not discuss how to import this certificate into various operating systems and configure client SSTP connections. I will only mention that the received certificate must be added to trusted root certification authorities.
Go to
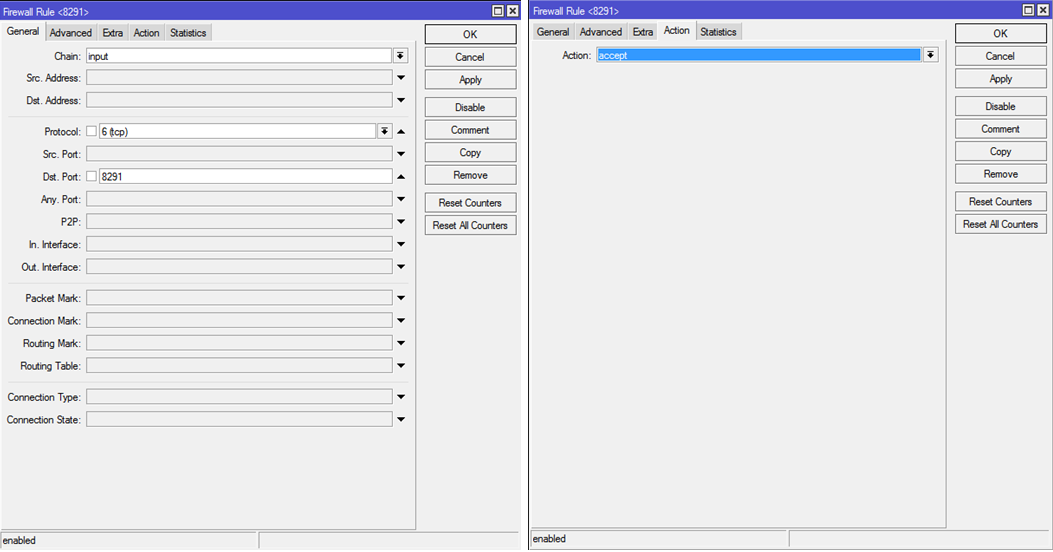
8.1. Access to the router via
Create a rule:
Create 2 rules:
Go to
This rule is necessary to create access without using routing on the client machine, since machine 2.82 will have an additional
Go to
1. Power on, initial setup
First you need to connect to the device. By default, the configuration on the router is configured on the
192.168.88.0/24 subnet. Open the address in the browser, download and save on your computer, Winbox.exe .
Launch
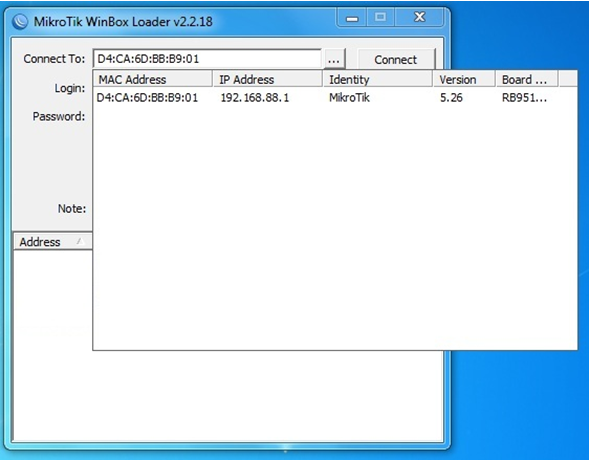
Winbox , on the contrary Connect to press the "…" button, and after a few seconds your router should appear in the list.')
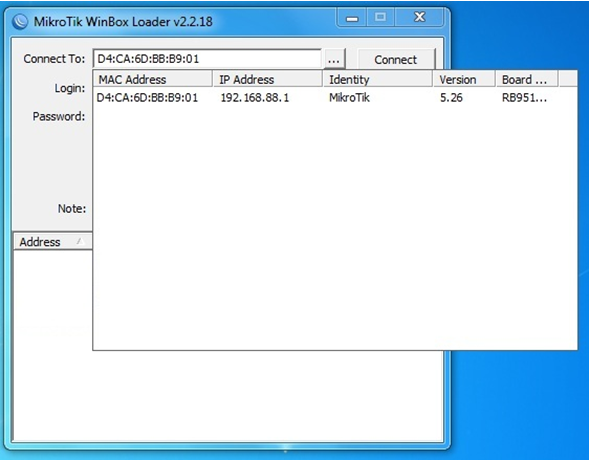
Double click the mouse on the MAC address and connect as
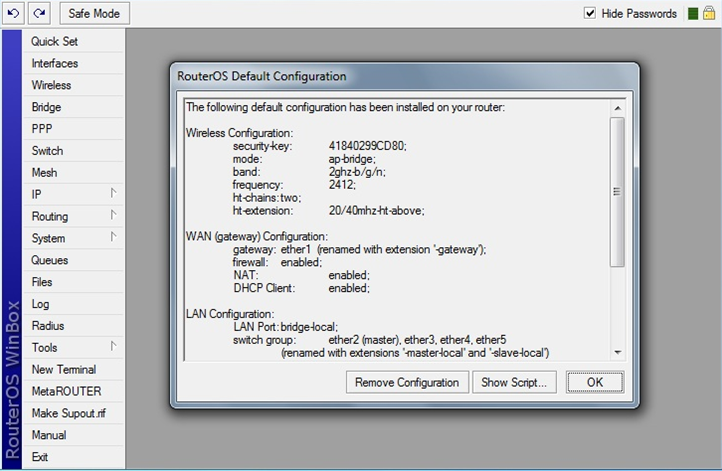
admin without a password.When you first log in, the system will warn you that an automatic router configuration script has been launched. Click the
Remove Configuration button: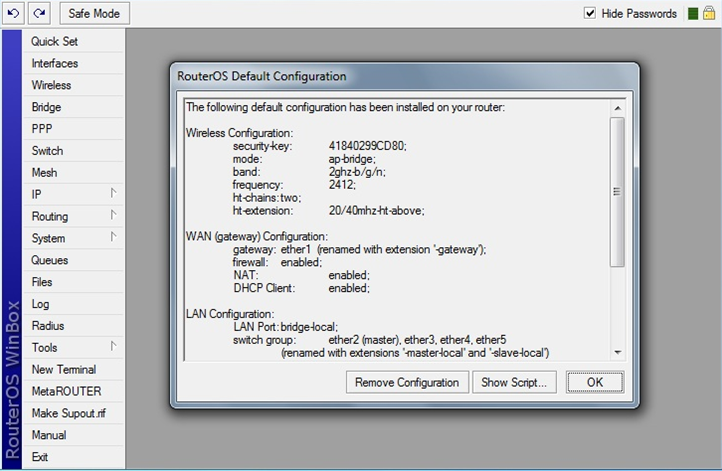
After that, we wait until the
Winbox console closes, and after a few seconds we start Winbox again (from where you saved it) and again connect to the MAC address.Having connected, we select
Interfaces on the left and delete unnecessary interfaces - VLAN, Bridge . We go into the settings of each interface (there are only 5 of them on the company's router) and disable the Master-port and proxy-arp , bringing the settings to the following form:
2. IP issuance
Go to
IP — Addresses . We issue the necessary addresses to the necessary interfaces. In case of using a router in the Escort network, 2 Internet service providers and an internal network are connected to it. The second internal network is formed via VPN. We specify the required IP for each interface. [admin@Mikrotik] /ip address> print Flags: X - disabled, I - invalid, D - dynamic # ADDRESS NETWORK INTERFACE 0 I ;;; , !!! 10.0.33.1/24 10.0.33.0 ether4-hosting-network 1 22.22.22.17/29 22.22.22.16 ether2-gateway2 2 11.11.11.1/28 11.11.11.0 ether1-gateway1 3 192.168.3.101/22 192.168.0.0 ether3-internal-network 4 I 192.168.4.2/22 192.168.4.0 ether4-hosting-network 3. Routing
3.1. Creating master and slave routes
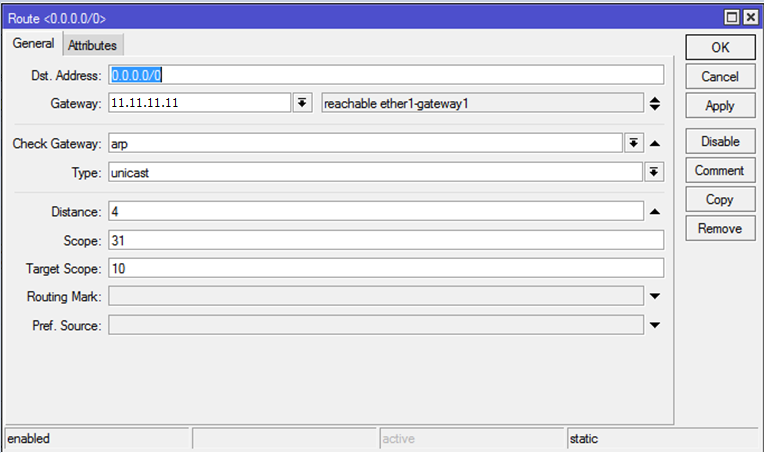
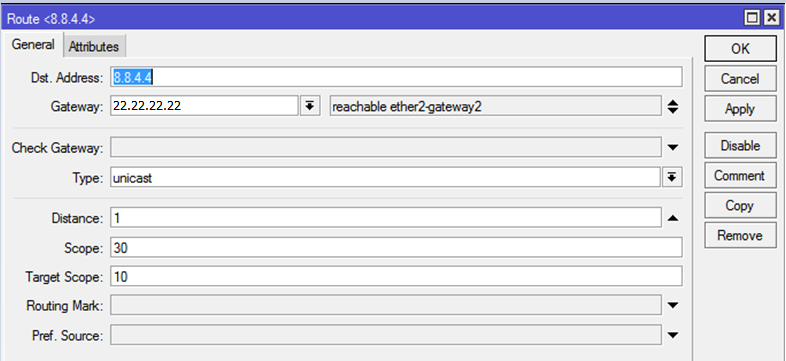
Go to the
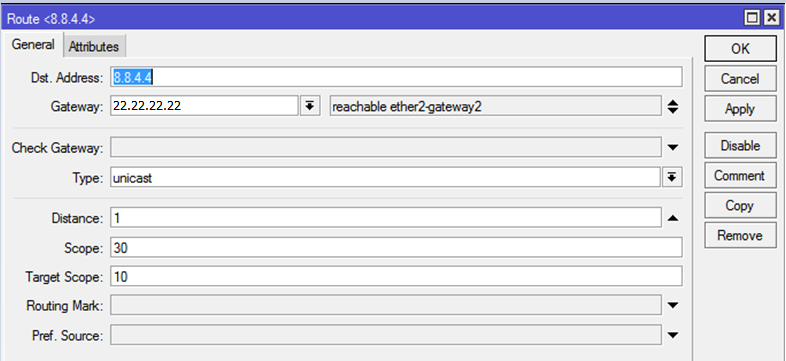
IP — Routes . By default, interfaces are used instead of hosts for routing. It is recommended to remove all static routes, and dynamic ones after changing statics will change themselves. Attention: in order to remove everything painlessly, you need to connect to the router via a local network, without using routes, otherwise the connection will be interrupted when you delete the main one . Next, create new routes: in the Dst.Address field Dst.Address specify 0.0.0.0/0, in the Gateway field, set the IP of the main gateway. Do not forget about the distance - which route is shorter, it will be the main one. In general, route settings should look like this: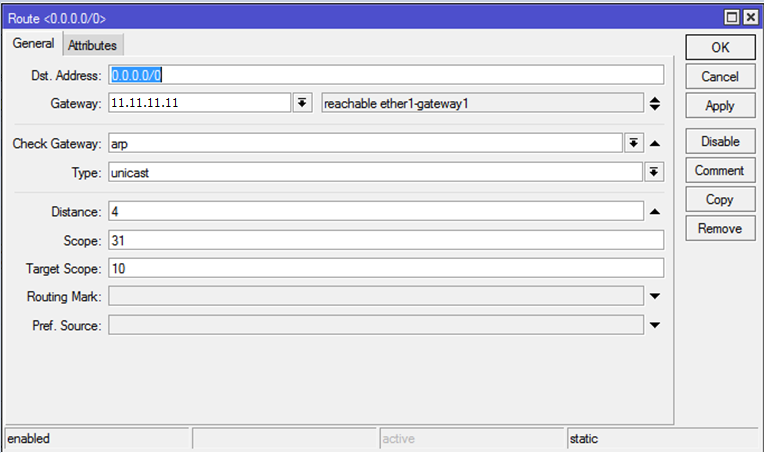
For external interfaces, we specify 11.11.11.11 with a distance of 4 and 22.22.22.22 with a distance of 3 as gateways.

After adding three routes (2 for external channels and 1 for the internal network), the router can be connected to the network and connected via IP 192.168.3.101 using the internal IP.
3.2. Creating table routing
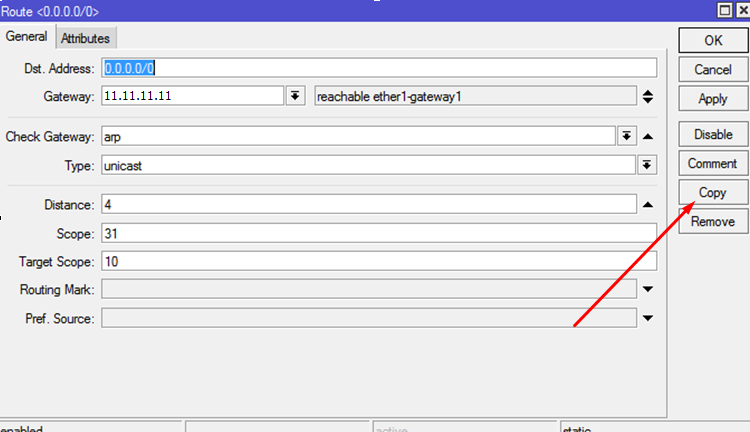
The configuration created above allows you to create 2 external interfaces, of which only one can work per unit of time — that is, the one that has a smaller distance and that has more distance — will work only when the cable is pulled out of the first interface. For obvious reasons, this does not suit us - we need the simultaneous operation of two gateways. To do this, you need to teach the router to return traffic to the interface from which the request came. This is done by creating two additional routes and setting up a firewall. First, create the necessary routes. Previously created routes will also be useful, but you can clone them, because they will change slightly. To do this, click on the route created earlier, click the
Copy button and add the Routing Mark - mark the routes with the interface name, respectively. I called them to_ISP1 and to_ISP2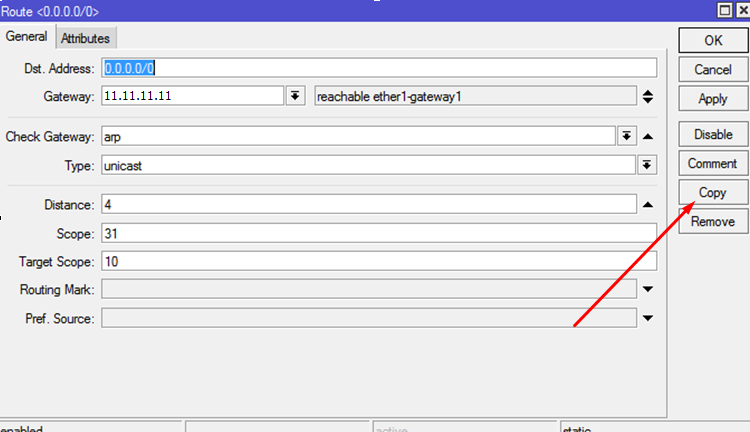

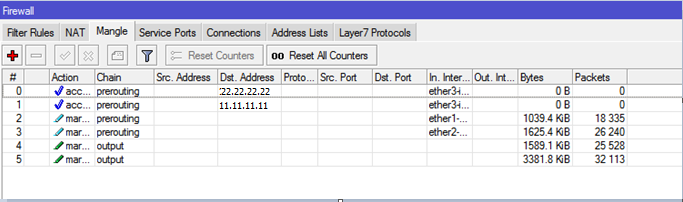
Next, go to
IP - Firewall - Mangle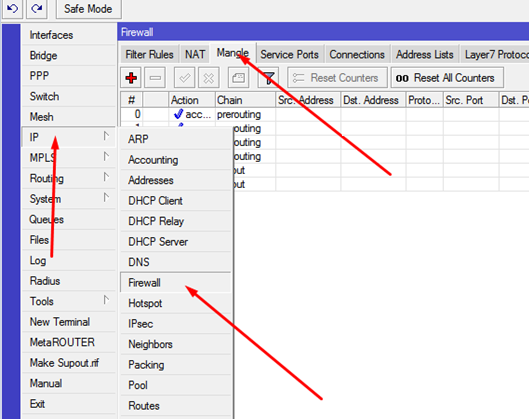
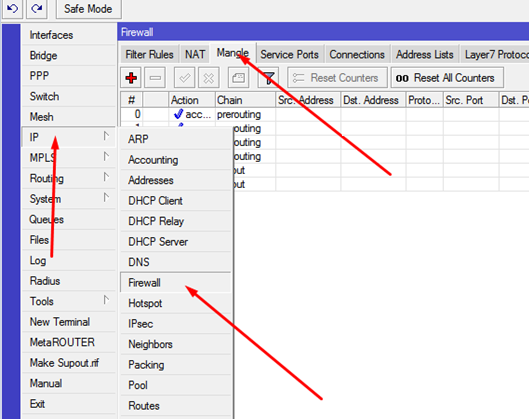
Create rules:
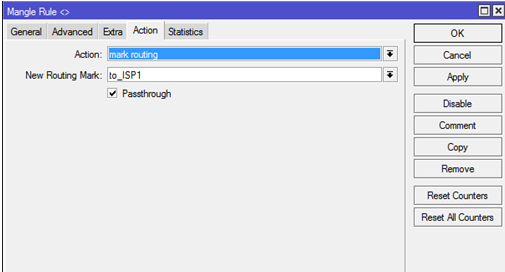
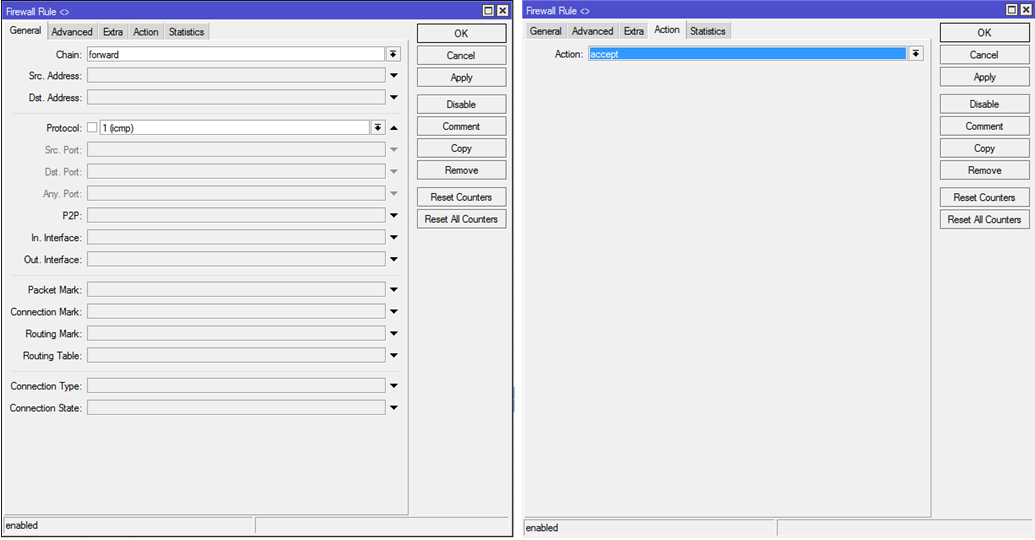
General: Chain: prerouting In-interface: Connection Mark: no-mark , Action: Action: mark connection New Connection Mark: ISP1_conn Passthrough: . Pictures to secure the material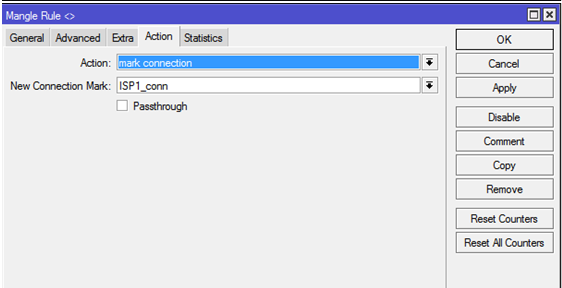
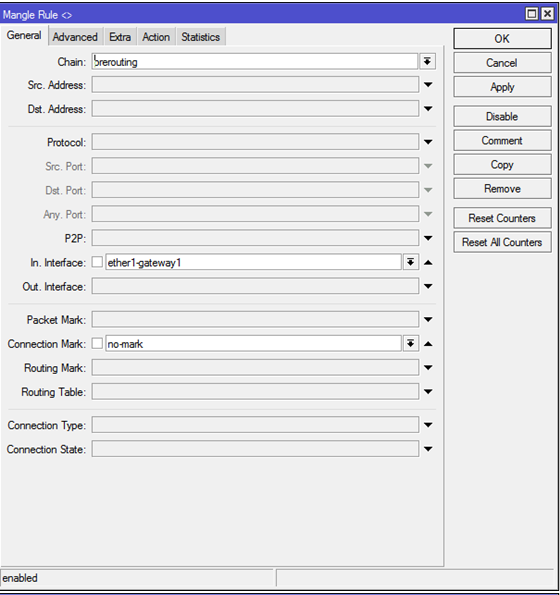
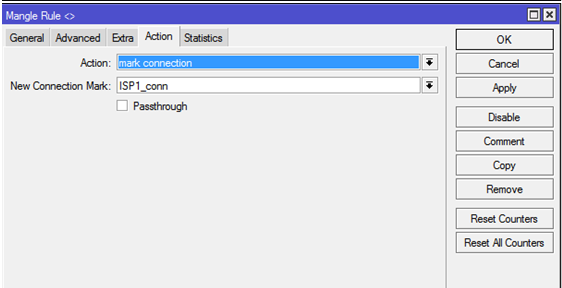
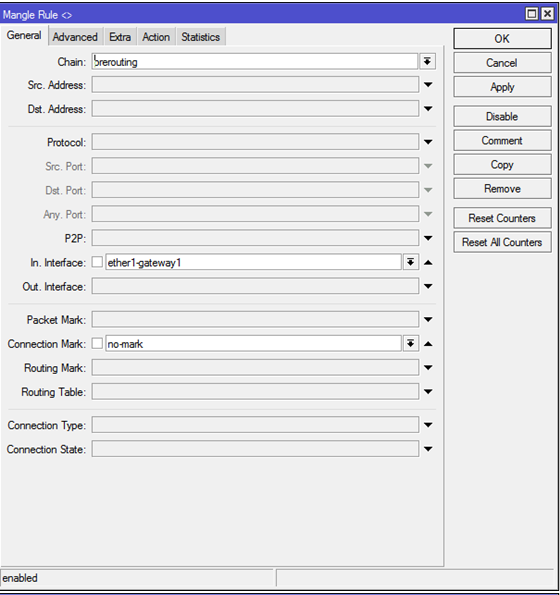
These actions must be repeated twice - for 2 external interfaces (brand
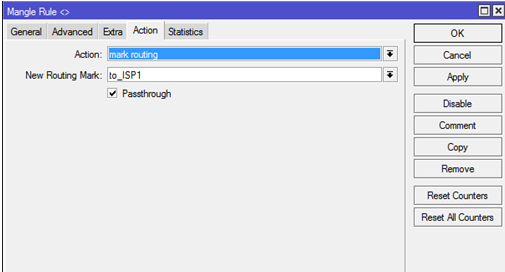
ISP1_conn and ISP2_conn respectively).Next, you need to create 2 more rules that will direct outgoing traffic marked
ISP1_conn and ISP2_conn to the routes marked above. Create a rule: General: Chain: output Connection Mark: ISP1_conn Action: mark routing New Routing Mark: to_ISP1 Passthrough: . Pictures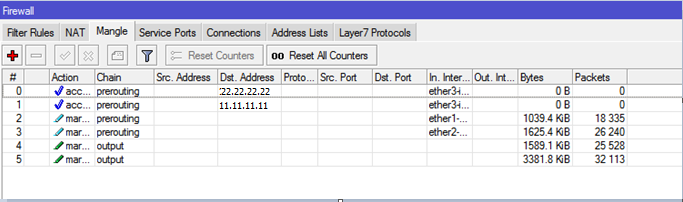


4. Balancing routes in Master-Slave mode
So, we have achieved the presence of two simultaneously working gateways, one of which has the highest priority than the second. The problem with this setting is that switching between gateways will be done only when the physical link on the device interface is dropped. But there are other situations as well: there is no more money in the account, problems on the provider side and so on - situations in which even the main gateway is available, but there is no further traffic and in this case the main gateway will not be switched. For auto-
Netwatch , you need to use the Netwatch feature, which monitors the presence of traffic on the interfaces and switches traffic depending on the rules. Configuring this functionality consists of 3 steps.4.1. Create switch scripts
Go to the
System — Scripts . Create 4 scripts with the names ISP1-DOWN, ISP1-UP, ISP2-DOWN, ISP2-UP . All scripts give maximum rights.Script Contents
ISP1-DOWN:
ISP1-UP:
ISP2-DOWN:
ISP2-UP:
/ip route disable [find dst-address=0.0.0.0/0 and gateway=11.11.11.11 and distance >=4]; ISP1-UP:
/ip route enable [find dst-address=0.0.0.0/0 and gateway=11.11.11.11 and distance >= 4]; ISP2-DOWN:
/ip route disable [find dst-address=0.0.0.0/0 and gateway=22.22.22.22 and distance >=3]; ISP2-UP:
/ip route enable [find dst-address=0.0.0.0/0 and gateway=22.22.22.22 and distance >=3]; 4.2. Creating Netwatch Rules
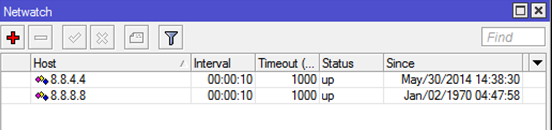
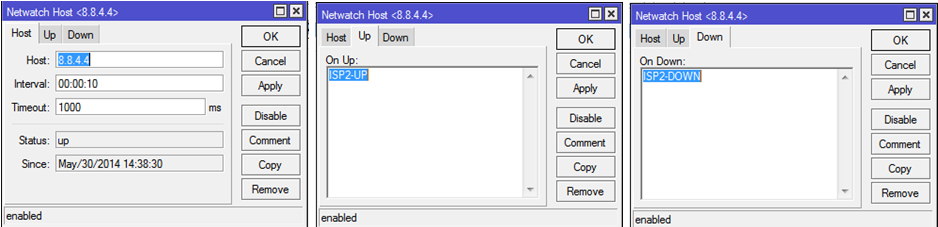
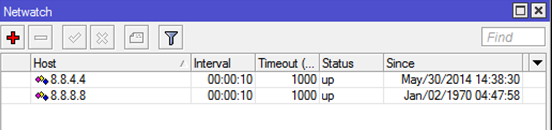
Go to
Tools — NetwatchCreate a new rule:
host: 8.8.4.4 Interval: 00:00:10 timeout: 1000ms Up: ISP2-UP Down: ISP2-DOWN : host: 8.8.8.8 Interval: 00:00:10 timeout: 1000ms Up: ISP1-UP Down: ISP1-DOWN Pictures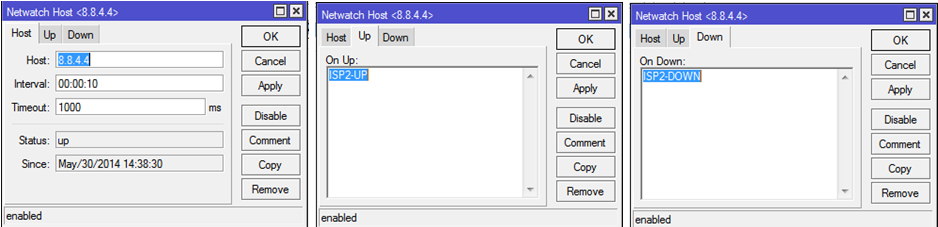
4.3. We create permanent independent routes.
Before each of the hosts (8.8.8.8 and 8.8.4.4), we prescribe a unique route with a reduced distance through different gateways (11.11.11.11 and 22.22.22.22).
You can check the operation of
netwatch breaking a logical (non-physical) link on one of the external interfaces. In my company, a managed switch was used for this, where a port that was not adjacent to the router was extinguished. Thus, the ping to host 8.8.8.8 failed, but the physical link was active. After the termination of the ping, Netwatch extinguished the necessary routes and the internal network accessed the Internet through a backup interface.5. We create NAT
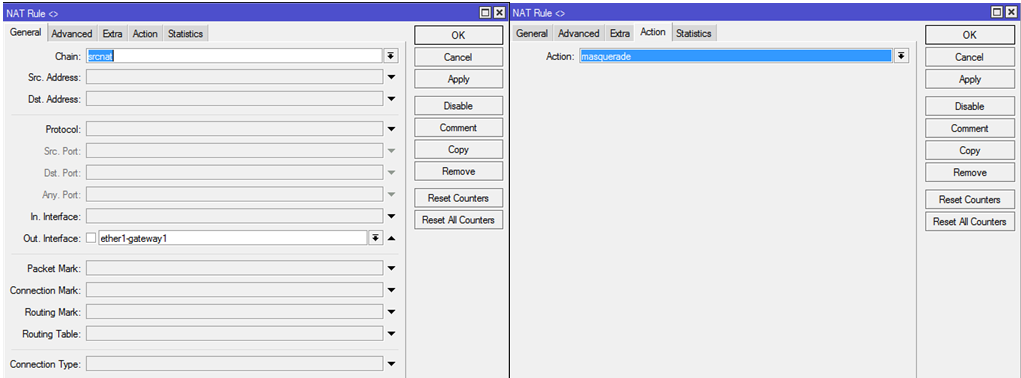
Go to the
IP — Firewall , go to the tab NATCreate 2 rules for each of the external interfaces:
Chain: srcnat Out-Interface: Action: masquerade Picture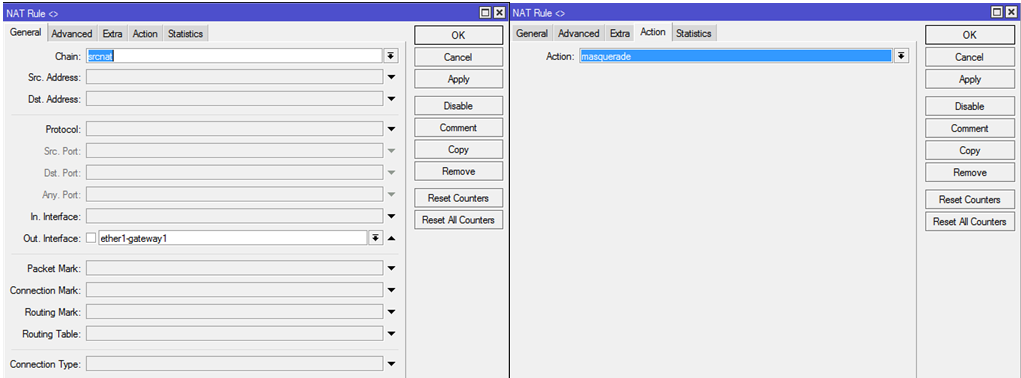
You can check NAT by pinging one of the websites on the Internet from a computer connected to the internal interface of the router. If you disable one of the two rules of NAT on the router, you can see how the trace to the selected host on the Internet changes.
6. Create a VPN server
6.1. We create the pool of IP addresses we need.
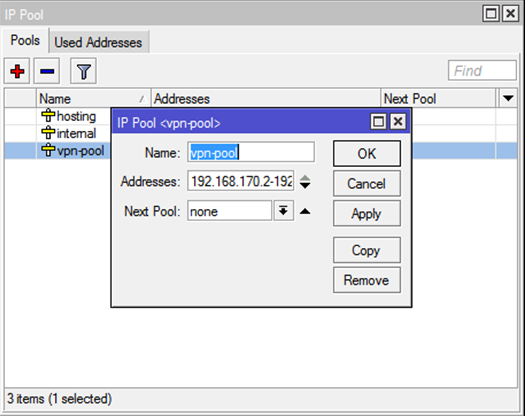
In the company's network, it was decided to use the subnet 192.168.168.0/22, with client addressing starting with 192.168.170.2 and the gateway address (of the router itself) 192.168.170.1
Go to the
IP — Pool and create a new vpn-pool with a range of 192.168.170.2-192.168.171.254: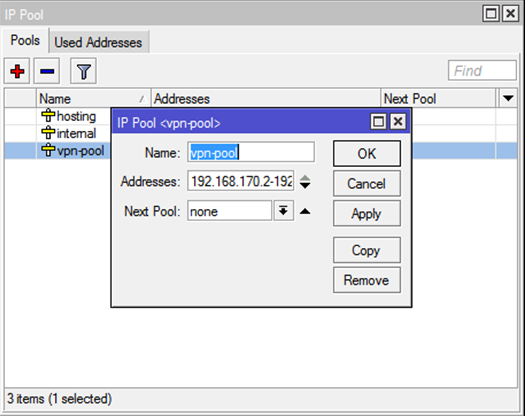
6.2. Enable PPTP server
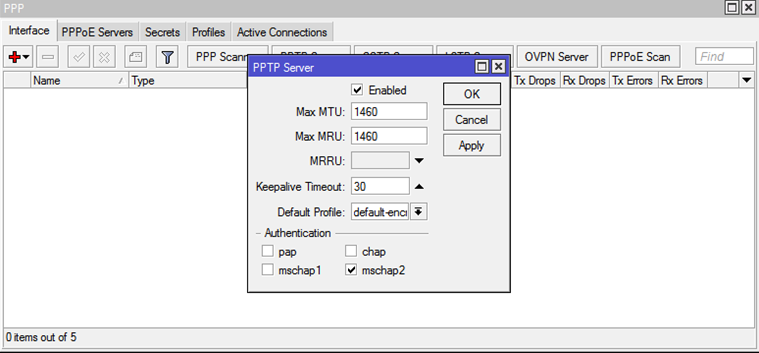
Go to the
PPP menu item, then on the Interfaces tab we find the PPTP Server button. Put the Enabled, mschap2 and select Default Profile: default-encoding .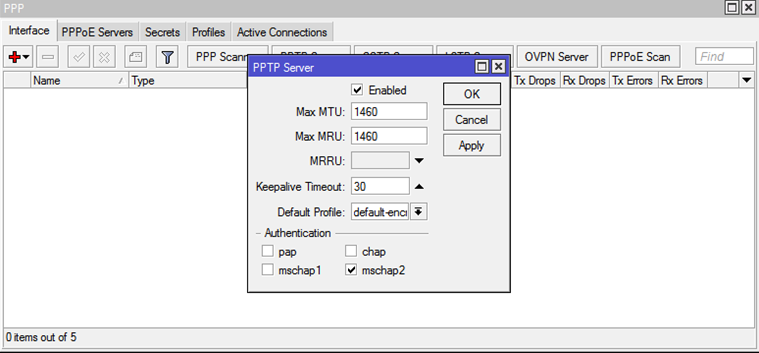
6.3. Configure encryption
Go to the
PPP Profile tab. On the General tab, we specify the Local Address: 192.168.170.1 , Remote Address: vpn-pool . On the Protocols tab on the option Use Encryption set the answer option is Yes .6.4. Create accounts
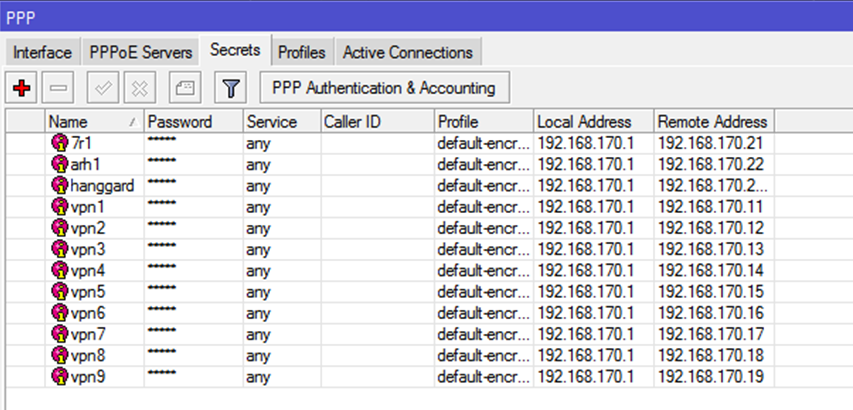
Go to the
Secrets tab. Create user: Name: Password: Service: any Profile: default-encryption Local Address: 192.168.170.1 Remote Address: , , , vpn-pool. , VPN . Picture

6.5. Batch account creation
For batch creation of secrets (accounts) VPN, you can use the script.
You need to go to the
System — Scripts , click "create a new" and insert the text of the script we need.
Script text
:global content [/file get [/file find name=vpnusers.txt] contents] ; :global contentLen [ :len $content ] ; :global lineEnd 0; :global line ""; :global lastEnd 0; :do { :set lineEnd [:find $content "\r\n" $lastEnd ] ; :set line [:pick $content $lastEnd $lineEnd] ; :set lastEnd ( $lineEnd + 2 ) ; :local tmpArray [:toarray $line] ; :if ( [:pick $tmpArray 0] != "" ) do={ :put $tmpArray; /ppp secret add name=[:pick $tmpArray 0] password=[:pick $tmpArray 1] \ local-address=[:pick $tmpArray 2] remote-address=[:pick $tmpArray 3] \ profile=[:pick $tmpArray 4] service=[:pick $tmpArray 5]; } } while ($lineEnd < $contentLen) After creating the script, it is enough to create a file in which to adhere to the following syntax:
,,IP_,IP_,_,The finished file should look something like this.

Please note that the last line is empty. If it is not left empty, the last filled line will not be processed.
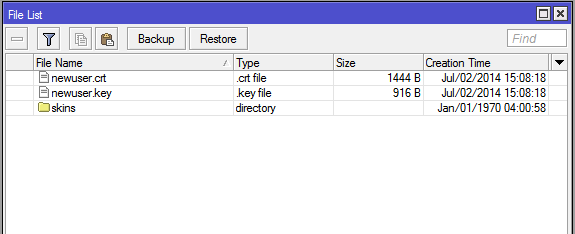
Next you need to open the menu item
Files . The created file must be dragged with the mouse into the resulting window. The file must be called vpnusers.txt , otherwise the script will not work.After these preparations, you can go to
System — Scripts , select the script we need and click Run Script :
As a result of the script, in
PPP — Secrets you can see the added accounts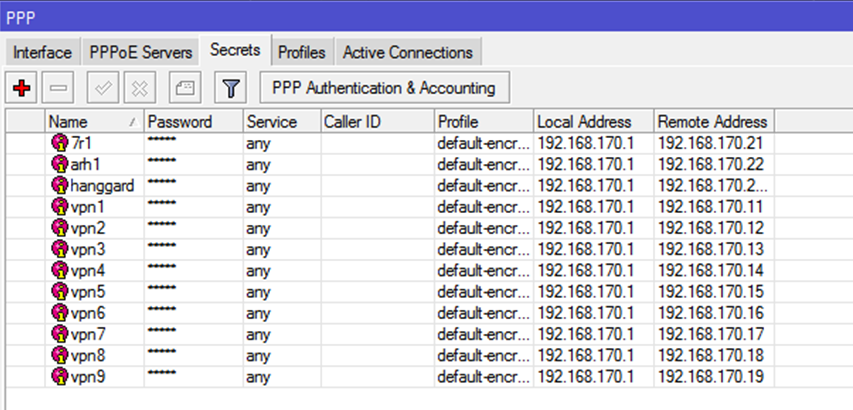
7. Configure SSTP
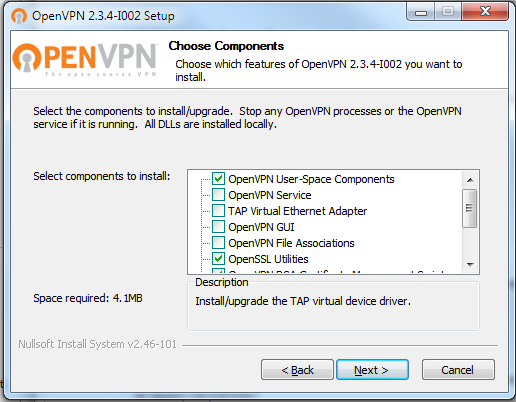
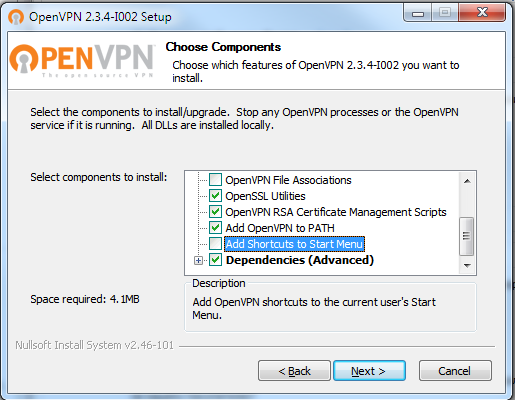
SSTP requires certificates. I used self-signed certificates issued by the OpenVPN snap-in . To obtain certificates you do not need to put all the components
it is enough just indicated in the screenshots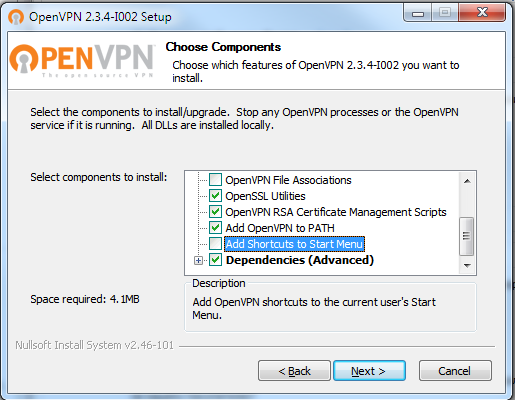
Next, run cmd on behalf of the administrator and go to the
c:\Program Files\OpenVPN\easy-rsa\ directory (or Program Files (x86) , if you installed the 32-bit version of OpenVPN on 64-bit Windows). Open for editing the file vars.bat . If not, then rename vars.bat.sample to vars.bat and vars.bat it to the form:vars.bat
@echo off rem Edit this variable to point to rem the openssl.cnf file included rem with easy-rsa. set HOME=%ProgramFiles%\OpenVPN\easy-rsa set KEY_CONFIG=openssl-1.0.0.cnf rem Edit this variable to point to rem your soon-to-be-created key rem directory. rem rem WARNING: clean-all will do rem a rm -rf on this directory rem so make sure you define rem it correctly! set KEY_DIR=keys rem Increase this to 2048 if you rem are paranoid. This will slow rem down TLS negotiation performance rem as well as the one-time DH parms rem generation process. set KEY_SIZE=1024 rem These are the default values for fields rem which will be placed in the certificate. rem Change these to reflect your site. rem Don't leave any of these parms blank. set KEY_COUNTRY=RU set KEY_PROVINCE=Nsk set KEY_CITY=Novosibirsk set KEY_ORG=Escort set KEY_EMAIL=i_nichupienko@soft-escort.ru set KEY_CN=87.245.176.183 set KEY_NAME=temp_nie set KEY_OU=changeme set PKCS11_MODULE_PATH=changeme set PKCS11_PIN=1234 Next, I cleanly edited the
build-ca.bat :build-ca.bat
@echo off cd %HOME% rem build a cert authority valid for ten years, starting now "c:\Program Files\OpenVPN\bin\openssl.exe" req -days 3650 -nodes -new -x509 -keyout %KEY_DIR%\%1.key -out %KEY_DIR%\%1.crt -config %KEY_CONFIG% After that, run in the following sequence:
c:\Program Files\OpenVPN\easy-rsa>vars.bat c:\Program Files\OpenVPN\easy-rsa>clean-all.bat c:\Program Files\OpenVPN\easy-rsa>build-ca.bat newuser You can just press enter to the questions of the last command in (the data entered in the
vars.bat file will be used), and you can enter new data. In general, as convenient.Command execution

Result

In the
Winbox router, click the Files button and copy the resulting files from the folder using the Drag'n'Drop method.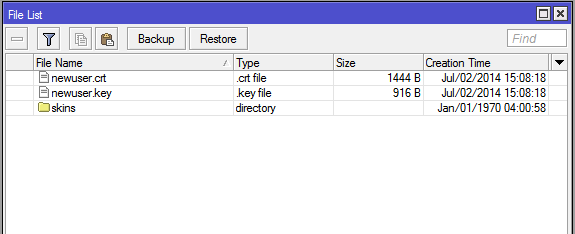
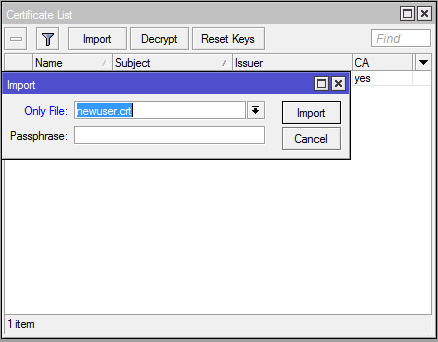
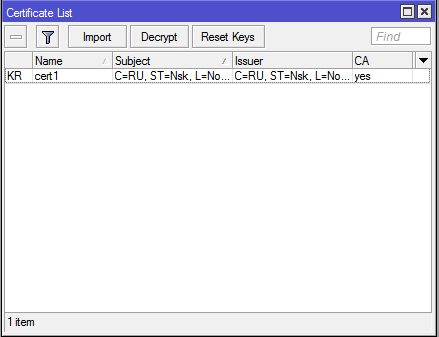
Next in
Winbox go to System — Certificates . Click Import , first select one file, then the second: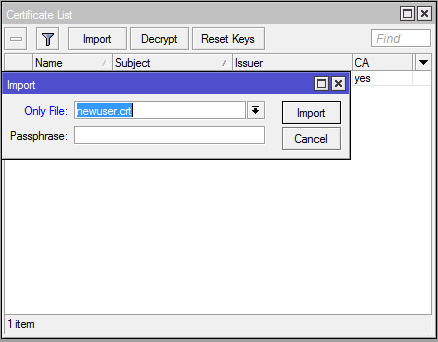
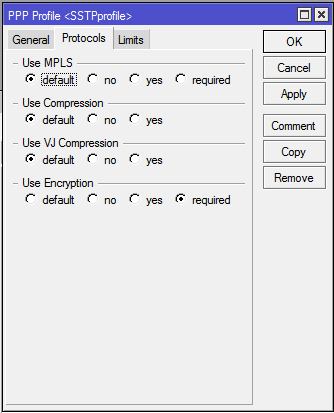
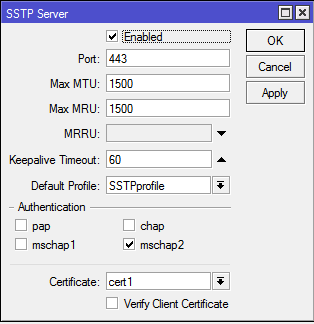
Go to the
PPP — Profile , open the default-encryption created earlier, click Copy and on the Protocol tab change the value of the Use Encryption field from Yes to Required :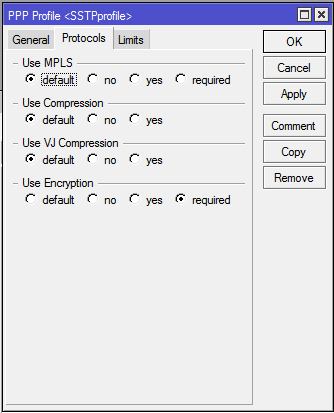
For the profile name, specify
SSTPprofile .Then, in the
System — PPP go to the Interface tab and click the SSTP-Server button there. We set the Enabled SSTPProfile , select SSTPProfile as the Default Profile and specify the certificate we need. We select only mschap2 as the authentication method.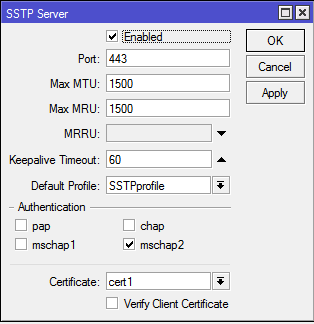
Since when creating secrets (logins / passwords) for
PPP we initially specified the type of service Any , but now we don’t need to create anything extra. Connection is ready.Since this article is about configuring a router, and not a client, I will not discuss how to import this certificate into various operating systems and configure client SSTP connections. I will only mention that the received certificate must be added to trusted root certification authorities.
8. Configure Key Firewall Rules
Go to
IP — Firewall — Filter Rules8.1. Access to the router via Winbox from the internal network
Create a rule:
Chain: Input Protocol: tcp Dst.Port: 8291 In. Interface: ether3-internal Action: accept Picture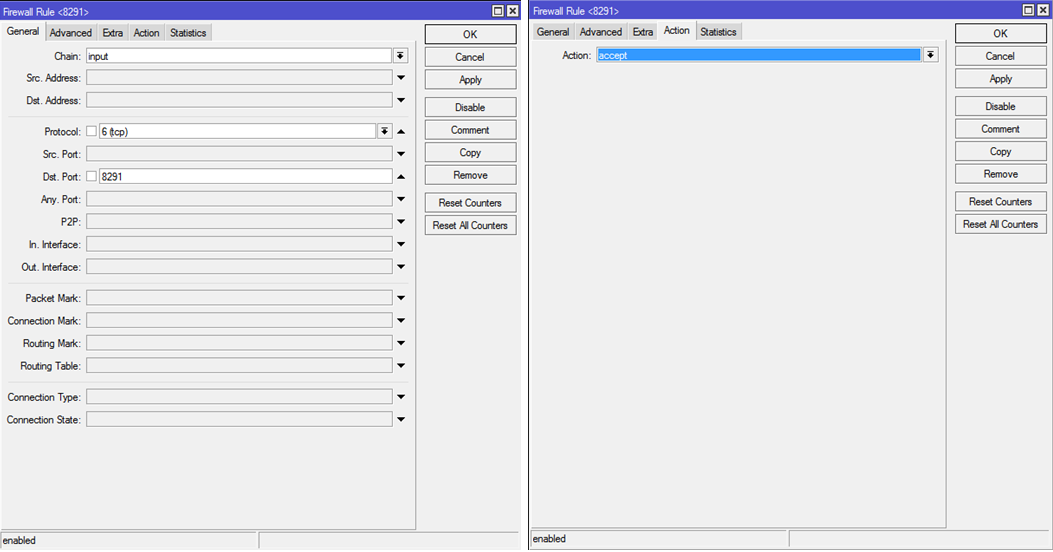
8.2. Ping out from the internal network
Create 2 rules:
Chain: forward Protocol: icmp Out. Interface: ether1-gateway1 ether2-gateway2 ( , .. . , 2) Action: accept Picture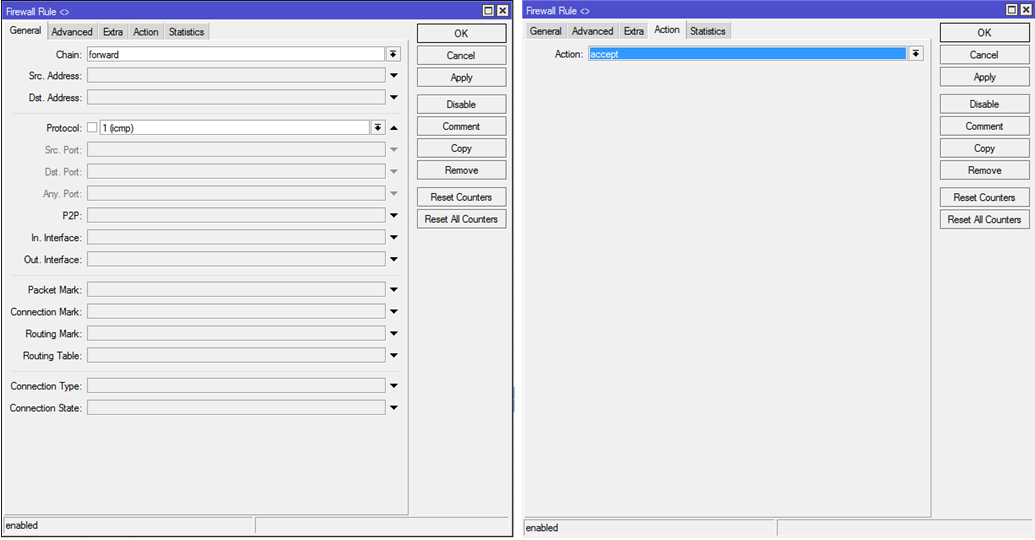
8.3. Ping the internal network from the VPN network
Chain: forward Protocol: icmp Src.Address: 192.168.170.0/24 Dst.Address: 192.168.0.0/22 Action: accept Picture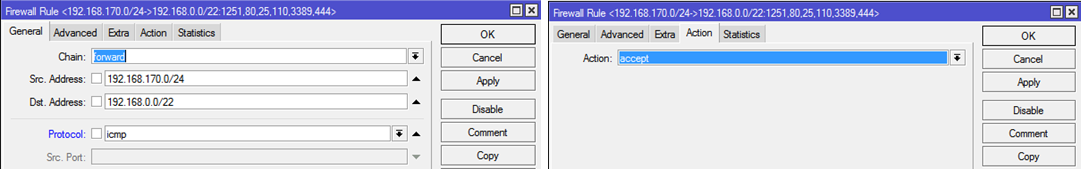
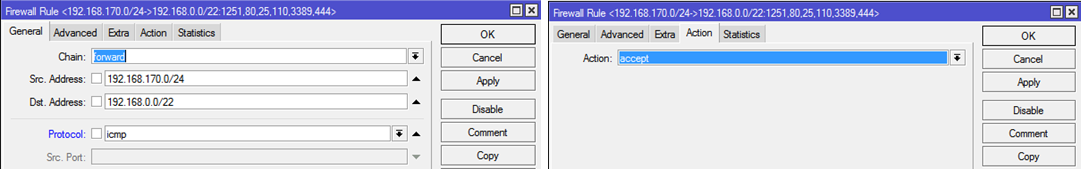
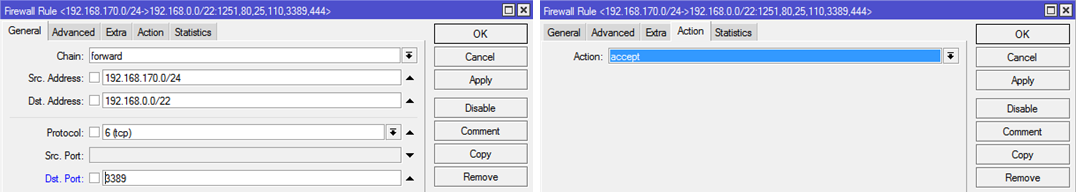
8.4. RDP access from the VPN to the internal network
Chain: forward Protocol: tcp Src.Address: 192.168.170.0/24 Dst.Address: 192.168.0.0/22 Dst.Port: 3389 Action: accept Picture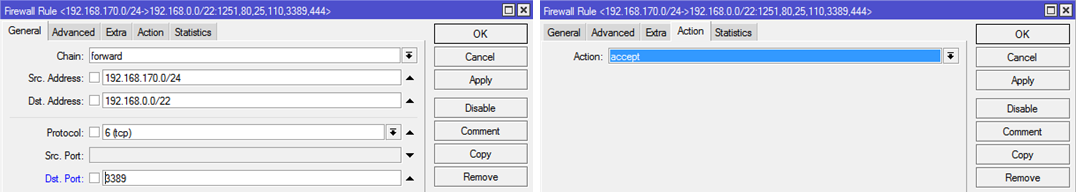
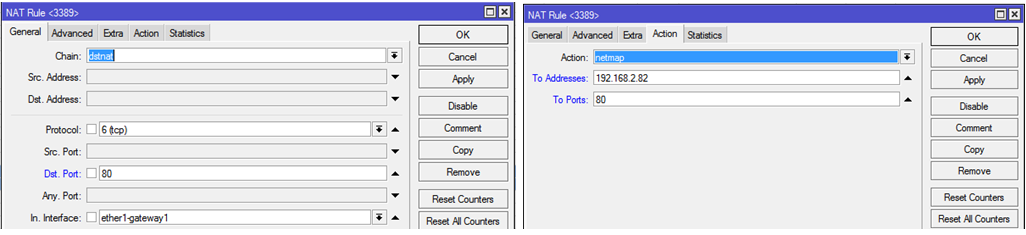
9. Publication of port 80 of the machine 192.168.2.82 outside
Go to
IP — Firewall — NAT Chain: dstnat Protocol: tcp Dst.Port: 80 In.Interface: ether1-gateway1 ( ether2-gateway2 ) Action: netmap To Addresses: 192.168.2.82 To Ports: 80 Picture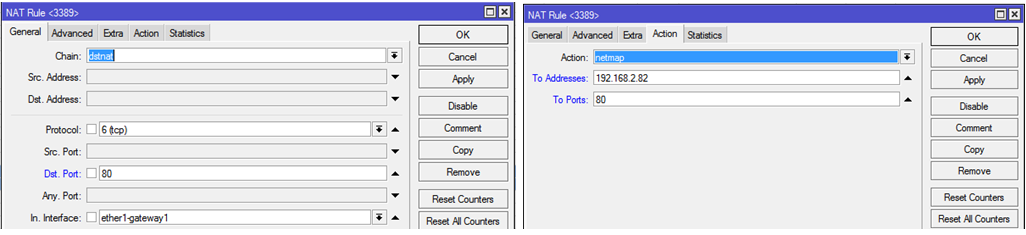
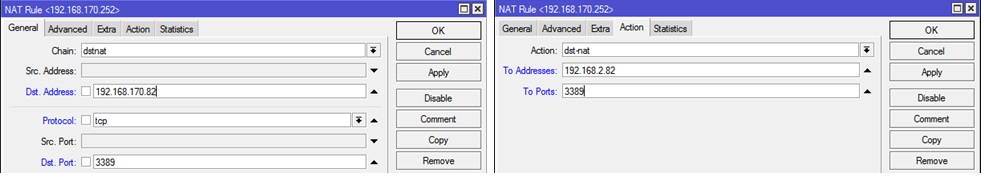
10. Publication of port 3389 of the machine 192.168.2.82 to the VPN
This rule is necessary to create access without using routing on the client machine, since machine 2.82 will have an additional
IP-: from the same subnet segment as the VPN client.Go to
IP — Firewall — NAT Chain: dstnat Dst.Address: 192.168.170.82 Protocol: tcp Dst.Port: 3389 Action: dst-nat To Addresses: 192.168.2.82 To Ports: 3389 Picture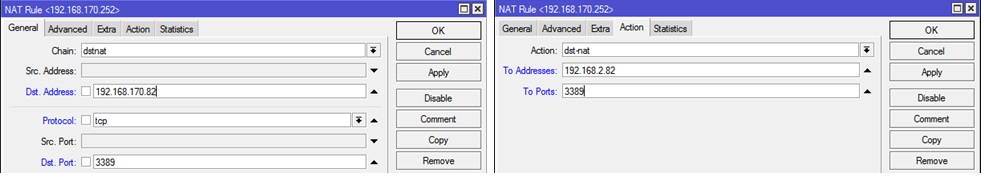
Source: https://habr.com/ru/post/227913/
All Articles