Detected a network of cyber espionage, operating in 40 countries
 Kaspersky Lab announces the discovery of a global cyber espionage network operating in 40 countries and affecting more than 350 important sites. The main tool for carrying out these attacks was the malware NetTraveler, so named after the line found in the source codes “NetTraveler Is Running!”. This trojan is designed to steal confidential data, is able to register keystrokes, work with the file system, conduct a search among office documents (DOC, XLS, RTF, PPT, PDF). In addition, he is interested in projects Corel Draw, AutoCAD and various configuration files.
Kaspersky Lab announces the discovery of a global cyber espionage network operating in 40 countries and affecting more than 350 important sites. The main tool for carrying out these attacks was the malware NetTraveler, so named after the line found in the source codes “NetTraveler Is Running!”. This trojan is designed to steal confidential data, is able to register keystrokes, work with the file system, conduct a search among office documents (DOC, XLS, RTF, PPT, PDF). In addition, he is interested in projects Corel Draw, AutoCAD and various configuration files.The largest number of infections was found in Mongolia, followed by Russia and India. In general, the attacks were recorded in 40 countries of the world, including Kazakhstan, Kyrgyzstan, China, Tajikistan, South Korea, Spain, Germany, the USA, Canada, the UK, Greece and others.
It is noteworthy that this spy network specializes in infecting government agencies, embassies, enterprises of the oil and gas industry, research institutes and military contractors. At which specific sites in Russia traces of NetTraveler infection were detected are not reported ...
Computer infection is carried out using targeted mailing phishing emails exploiting vulnerabilities in MSWord and Windows (exploit.MSWord.CVE-2010-3333.cg, exploit.MSWord.CVE-2010-3333.ci, exploit.MSWord.CVE-2010-3333 .cl, exploit.Win32.CVE-2012-0158.y, exploit.MSWord.CVE-2012-0158.an, exploit.MSWord.CVE-2012-0158.ax, exploit.Win32.CVE-2012-0158.aa ). The first activity of the network was discovered in 2004, and the largest number of infections accounted for 2010-2013.
NetTraveler distribution area:

')
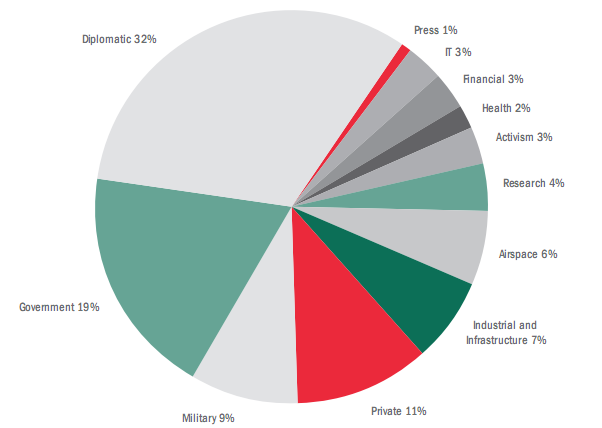
The distribution of infections by industry:
We read the report from LC “TheNetTravelerAttacks, Part 1” for more details.
A good reason for the security guards of important objects in the country is to check their networks.
Signs of infection:
IP network traffic
> 209.11.241.144 - mothership, VPn server, c2
> 121.12.124.69 - c2 (allen.w223.west263.cn)
> 61.178.77.111 - c2 (wolf0.3322.org)
> 182.50.130.68 - c2 (viprambler.com)
> 103.20.192.59 - c2 (sunshine.59.ydli.net)
> 213.156.6.122 - c2 (cultureacess.com)
> 209.130.115.38 - c2 (tsgoogoo.net)
> 98.143.145.80 - c2 (spit113.minidns.net)
> 96.46.4.237 - c2 (sghrhd.190.20081.info)
> 109.169.86.178 - c2 (imapupdate.com)
> 125.67.89.156 - c2 (faceboak.net)
> 142.4.96.6 - c2 (buynewes.com)
> 124.115.21.209 - c2 iP
> 67.198.140.148 - c2 (southstock.net)
> 96.44.179.26 - c2 (vip222idc.s169.288idc.com)
> 235.22.123.90 - c2 (gami1.com)
> 178.77.45.32 - c2 (ra1nru.com)
> 121.12.124.69 - c2 (allen.w223.west263.cn)
> 61.178.77.111 - c2 (wolf0.3322.org)
> 182.50.130.68 - c2 (viprambler.com)
> 103.20.192.59 - c2 (sunshine.59.ydli.net)
> 213.156.6.122 - c2 (cultureacess.com)
> 209.130.115.38 - c2 (tsgoogoo.net)
> 98.143.145.80 - c2 (spit113.minidns.net)
> 96.46.4.237 - c2 (sghrhd.190.20081.info)
> 109.169.86.178 - c2 (imapupdate.com)
> 125.67.89.156 - c2 (faceboak.net)
> 142.4.96.6 - c2 (buynewes.com)
> 124.115.21.209 - c2 iP
> 67.198.140.148 - c2 (southstock.net)
> 96.44.179.26 - c2 (vip222idc.s169.288idc.com)
> 235.22.123.90 - c2 (gami1.com)
> 178.77.45.32 - c2 (ra1nru.com)
Domain names
> allen.w223.west263.cn
> andriodphone.net
> bauer.8866.org
> buynewes.com
> cultureacess.com
> discoverypeace.org
> drag2008.com
> eaglesey.com
> enterairment.net
> faceboak.net
> gami1.com
> globalmailru.com
> hint09.9966.org
> imapupdate.com
> inwpvpn.com
> keyboardhk.com
> localgroupnet.com
> mailyandexru.com
> msnnewes.com
> newesyahoo.com
> newfax.net
> pkspring.net - sinkholed by Kaspersky lab
> ra1nru.com
> ramb1er.com
> sghrhd.190.20081.info
> southstock.net
> spit113.minidns.net
> tsgoogoo.net
> vip222idc.s169.288idc.com
> viplenta.com
> vipmailru.com
> viprainru.com
> viprambler.com
> vipyandex.com
> vpnwork.3322.org
> wolf0.3322.org
> wolf001.us109.eoidc.net
> yahooair.com
> yangdex.org - sinkholed by Kaspersky lab
> zeroicelee.com
> andriodphone.net
> bauer.8866.org
> buynewes.com
> cultureacess.com
> discoverypeace.org
> drag2008.com
> eaglesey.com
> enterairment.net
> faceboak.net
> gami1.com
> globalmailru.com
> hint09.9966.org
> imapupdate.com
> inwpvpn.com
> keyboardhk.com
> localgroupnet.com
> mailyandexru.com
> msnnewes.com
> newesyahoo.com
> newfax.net
> pkspring.net - sinkholed by Kaspersky lab
> ra1nru.com
> ramb1er.com
> sghrhd.190.20081.info
> southstock.net
> spit113.minidns.net
> tsgoogoo.net
> vip222idc.s169.288idc.com
> viplenta.com
> vipmailru.com
> viprainru.com
> viprambler.com
> vipyandex.com
> vpnwork.3322.org
> wolf0.3322.org
> wolf001.us109.eoidc.net
> yahooair.com
> yangdex.org - sinkholed by Kaspersky lab
> zeroicelee.com
Mutexes
> boat-12 is running!
> dochunter2012 is running!
> hunter-2012 is running!
> nt-2012 is running!
> nettravler is running!
> nettravler2012 is running!
> sh-2011 is running!
> shenghai is running!
> dochunter2012 is running!
> hunter-2012 is running!
> nt-2012 is running!
> nettravler is running!
> nettravler2012 is running!
> sh-2011 is running!
> shenghai is running!
Names of malicious files on disks
> main active group (s) in 2013, unique configuration filenames: perf2012.ini, config_t.dat, config_shenghai.dat, pert2012.ini, in:
• c: \ documents and settings \ [user] \ local set tings \ temp \
• c: \ users \ [user] \ local settings \ temp \
• c: \ WindoWs \ temp \
• c: \ WindoWs \ system \
> other (older) variants, configs: FmiFen.ini in:
•% system%
> malware body: net.exe, netmgr.exe, net mgr.dll in
• c: \
• c: \ WindoWs \ system \
•% system%
•% temp%
• c: \ WindoWs \ temp \
•% appdata% \ Adobe \
> other (older) variants, malware bodies:
•% system% \ bootuid.dll
•% system% \ wuaucit.exe
•% system% \ 6to4ex.dll
•% temp% \ Process.dll
•% temp% \ Process.dll_d
•% temp% \ cmss.exe
•% temp% \ sysinfo2012.dll
•% temp% \ winlogin.exe
•% windir% \ system32 \ iasex.dll
•% windir% \ system32 \ system_t.dll
•% temp% \ smcs.exe
•% appdata% \ Adobe \ sysinfo2012.dll
> Artifacts during installation and running:
•% temp% \ Win32en.bat
•% system% \ dnlist.ini
•% temp% \ dnlist.ini
•% appdata% \ Adobe \ ie.log
•% temp% \ ie.log
•% system% \ enumfs.ini
•% temp% \ enumfs.ini
•% system% \ install.tmp
•% system% \ kyrecord.txt
• c: \ documents and settings \ user \ start menu \ Programs \ startup \ seru-vice.lnk
• c: \ documents and settings \ user \ start menu \ Programs \ startup \ net-mgr.lnk
• c: \ docume ~ 1 \ user ~ 1 \ lo cAls ~ 1 \ temp \ recycler_w \ Allindex.ini
• c: \ docume ~ 1 \ user ~ 1 \ lo cAls ~ 1 \ temp \ recycler_w \ Allindex.ini_d
• c: \ documents and settings \ [user] \ local set tings \ temp \
• c: \ users \ [user] \ local settings \ temp \
• c: \ WindoWs \ temp \
• c: \ WindoWs \ system \
> other (older) variants, configs: FmiFen.ini in:
•% system%
> malware body: net.exe, netmgr.exe, net mgr.dll in
• c: \
• c: \ WindoWs \ system \
•% system%
•% temp%
• c: \ WindoWs \ temp \
•% appdata% \ Adobe \
> other (older) variants, malware bodies:
•% system% \ bootuid.dll
•% system% \ wuaucit.exe
•% system% \ 6to4ex.dll
•% temp% \ Process.dll
•% temp% \ Process.dll_d
•% temp% \ cmss.exe
•% temp% \ sysinfo2012.dll
•% temp% \ winlogin.exe
•% windir% \ system32 \ iasex.dll
•% windir% \ system32 \ system_t.dll
•% temp% \ smcs.exe
•% appdata% \ Adobe \ sysinfo2012.dll
> Artifacts during installation and running:
•% temp% \ Win32en.bat
•% system% \ dnlist.ini
•% temp% \ dnlist.ini
•% appdata% \ Adobe \ ie.log
•% temp% \ ie.log
•% system% \ enumfs.ini
•% temp% \ enumfs.ini
•% system% \ install.tmp
•% system% \ kyrecord.txt
• c: \ documents and settings \ user \ start menu \ Programs \ startup \ seru-vice.lnk
• c: \ documents and settings \ user \ start menu \ Programs \ startup \ net-mgr.lnk
• c: \ docume ~ 1 \ user ~ 1 \ lo cAls ~ 1 \ temp \ recycler_w \ Allindex.ini
• c: \ docume ~ 1 \ user ~ 1 \ lo cAls ~ 1 \ temp \ recycler_w \ Allindex.ini_d
Name of malware modules according to LC version
> backdoor.Win32.bifrose.bcx
> trojan-dropper.Win32.dorifel.acrn
> trojan-dropper.Win32.dorifel.acsj
> trojan-dropper.Win32.dorifel.acsm
> trojan-dropper.Win32.dorifel.acuf
> trojan-dropper.Win32.dorifel.cql
> trojan-dropper.Win32.dorifel.fhg
> trojan-dropper.Win32.dorifel.fny
> trojan-dropper.Win32.dorifel.iat
> trojan-dropper.Win32.dorifel.jam
> trojan-dropper.Win32.dorifel.kcy
> trojan-dropper.Win32.dorifel.ylt
> trojan-spy.Win32.travnet. *
> trojan.multi.yahg.a
> trojan.Win32.Agent2.eakj
> trojan.Win32.Agent2.exms
> trojan.Win32.Agent2.ezgb
> trojan.Win32.Agent2.fdhs
> trojan.Win32.delf.dgmw
> trojan.Win32.delf.dgmx
> trojan.Win32.Genome.agyil
> trojan.Win32.Genome.aiunu
> trojan.Win32.Genome.ajeqr
> trojan.Win32.Genome.akqco
> trojan.Win32.Genome.aksho
> trojan.Win32.Jorik.travnet. *
> not-a-virus: downloader.Win32.nettraveler. *
> trojan-dropper.Win32.dorifel.acrn
> trojan-dropper.Win32.dorifel.acsj
> trojan-dropper.Win32.dorifel.acsm
> trojan-dropper.Win32.dorifel.acuf
> trojan-dropper.Win32.dorifel.cql
> trojan-dropper.Win32.dorifel.fhg
> trojan-dropper.Win32.dorifel.fny
> trojan-dropper.Win32.dorifel.iat
> trojan-dropper.Win32.dorifel.jam
> trojan-dropper.Win32.dorifel.kcy
> trojan-dropper.Win32.dorifel.ylt
> trojan-spy.Win32.travnet. *
> trojan.multi.yahg.a
> trojan.Win32.Agent2.eakj
> trojan.Win32.Agent2.exms
> trojan.Win32.Agent2.ezgb
> trojan.Win32.Agent2.fdhs
> trojan.Win32.delf.dgmw
> trojan.Win32.delf.dgmx
> trojan.Win32.Genome.agyil
> trojan.Win32.Genome.aiunu
> trojan.Win32.Genome.ajeqr
> trojan.Win32.Genome.akqco
> trojan.Win32.Genome.aksho
> trojan.Win32.Jorik.travnet. *
> not-a-virus: downloader.Win32.nettraveler. *
MD5 malware modules
01d06f85fce63444c3563fe3bd20c004
03e8d330abc77a6a9d635d2e7c0e213a
08e5352a2416bd32a1c07f2d6c2f11fa
13b3cb819b460591c27e133e93fb8661
19a0693480c82f2b7fc8659d8f91717a
1a70e1e36e6afa454f6457140ac3d2ec
1dcad7c8f56207b2c423353f0c328755
1f26e5f9b44c28b37b6cd13283838366
209c3b51cad30c85ca79a9f067ce04cd
22be9cca6e4ec3af327595b890a92fec
28e9faec9de3bbdeb65435bfc377d1f8
294da087e6329ae78c1a5fb42b999500
29a394a4ec8a30b5f36c7b874fc9fe10
2a43c23a17cd2bc9074a486c47444e7c
2ac8f77548e87b401767c7076adfa00d
2d0e4748d857c12184ed2c94c13ec1ae
2dc139d82a2a5bf027bcb6a40f75b3f4
33334d8dc36c4ee7739fe2f8b448da72
36f9a0e71f0b580333c61bfeaa88df39
37d588b289c65f10c256e43eba939a0a
382c1d692dd3cec9b046e5c0eeaf92e6
39c2b2ee24373bf1ef20faff958718bc
3b4cf5f1ff8c4187e41c6ab80f000491
3cb96fe79aa01c82ac68c54e88918e57
482f112cb7cb0293d99f8a7606acbe85
4968882f189236952fd38a11586b395a
4c8950da250ea135ee77a2644af414ba
524aed944b7f307eea5677eda7e2079a
54583ccc97c33e358510b563b1536e69
57f2374d9f2a787339b0c6a5b1008a72
5e35b31472a2e603a995198d8e8411ed
5e7c5e8d9f5864488ddf04b662d1ad8e
63f0f91e3ccf5dd00a455d3038a299f4
66684b8b82fb5318a41ab7e6abb8dd42
677f7c42f79a0a58760056529739fdd6
6afeec03c8f4bc78fa2b3ad27392b0e7
6d00e4f95fba02126b32bb74dc4fec55
6d49cdbade7541d46be3fb47a0f563bb
6de813a22b2b73e330085ec7c85e041b
71f311a648348e7598eb55ab7618842c
723129912a2d0fb4aede7100071787ef
778c1764dd5c36c1eb96c49a8f8441e6
7b92e9d21bc4db838bc102b289f4fd5f
812d8e4d7a484bb363b139cfa08617e5
81591ae1c975b8a0b5ad5546a103992c
81d92e20f3078bd8e43b226308393e43
83429db9cc63196bf42c691cc09b7b84
852f562812305ad099372109f8e8b189
85865e048183849b255c92e609a5fa25
86cce64193a347b50329a32cdf08d198
89bfd463ca76b62c61a548778316567d
8ccea94fd83d9cb1b15a2a4befec24a2
8d3036a65ac2404d4562cdb927fd3d2c
8d78a9e3df1e19f9520f2bbb5f04cb54
8dc61b737990385473dca9bfc826727b
95113e04af14c23df607964fa9d83476
9b198f1e260700bdcb4740266cd35b3f
9c1c2825532b25e266d62db50952ab44
9c544da8c23826379d60581cce17a483
a0e350787e4134ea91ccb26d17cdf167
a1169fb2eb93616ced7536a53fb05648
a431d5786d9d95bc9d04df07cbefc0a2
a6d89df2a80675980fb3e4a9bcc162e2
a77456a160890a26a8f7c019c2e77021
aa6f8eff83aea3ff7b8f016e67f74dac
af6649323daf6dbd3aef1b950588487c
b3840ec1299517dacd6c18c71ff5bafc
b8c99bc028a0a32288d858df7bf6bec1
b990752f8266d7648070bea7e24d326f
ba026e6190aee2c64ef62a4e79419bcf
bea6e3481c0a06ce36600d8b3cc6155b
c87e8a3ceefd93c7e431b753801c6bb6
cb9cc50b18a7c91cf4a34c624b90db5d
cebaaad59f1616698dec4f14d76b4c9a
d04a7f30c83290b86cac8d762dcc2df5
d218706eb07f2722ae4e0106cce27d52
d286c4cdf40e2dae5362eff562bccd3a
d2fe88fff648a0bcbfdf0f0bd042a0a4
d354b71116961cad955ed11cb938ca32
d687cfde1c4ea77de1b92ea2f9e90ad5
d80c29813bfbc3cbcbd469249d49ebf3
d9c0ca95e49b113c5751fffdb20beb3f
d9cf41b5d11e42dabf9470964d09c000
db6e36f962fdb58c8e9f8f9a781fda66
dc01df3c40cb4fb0bef448693475ea1b
def612ad0554006378f185d3b56efb57
e51a4cc0272a98e9eddfec16667603f4
e5b1ffd2ecd7e610d07d093d65639da9
eb5761c410b5139f23235e9b67964495
eefc66a1e978dc9d825f28702106d4d5
efa23860086c5d12d3e6b918073c717f
f3c5c20f5c45fc401484caf72753d778
fad8f37c9bd5420f49cfd5960a60fa24
fb3495715764cdaa547f2b040c0a9b1f
fc3853c2383e2fbb2af381fd1277504d
fe16c30782e2b16b07d5a3a1cf9dfb8f
ff04126a5d61a10c81bfd0a6d0a643d0
03e8d330abc77a6a9d635d2e7c0e213a
08e5352a2416bd32a1c07f2d6c2f11fa
13b3cb819b460591c27e133e93fb8661
19a0693480c82f2b7fc8659d8f91717a
1a70e1e36e6afa454f6457140ac3d2ec
1dcad7c8f56207b2c423353f0c328755
1f26e5f9b44c28b37b6cd13283838366
209c3b51cad30c85ca79a9f067ce04cd
22be9cca6e4ec3af327595b890a92fec
28e9faec9de3bbdeb65435bfc377d1f8
294da087e6329ae78c1a5fb42b999500
29a394a4ec8a30b5f36c7b874fc9fe10
2a43c23a17cd2bc9074a486c47444e7c
2ac8f77548e87b401767c7076adfa00d
2d0e4748d857c12184ed2c94c13ec1ae
2dc139d82a2a5bf027bcb6a40f75b3f4
33334d8dc36c4ee7739fe2f8b448da72
36f9a0e71f0b580333c61bfeaa88df39
37d588b289c65f10c256e43eba939a0a
382c1d692dd3cec9b046e5c0eeaf92e6
39c2b2ee24373bf1ef20faff958718bc
3b4cf5f1ff8c4187e41c6ab80f000491
3cb96fe79aa01c82ac68c54e88918e57
482f112cb7cb0293d99f8a7606acbe85
4968882f189236952fd38a11586b395a
4c8950da250ea135ee77a2644af414ba
524aed944b7f307eea5677eda7e2079a
54583ccc97c33e358510b563b1536e69
57f2374d9f2a787339b0c6a5b1008a72
5e35b31472a2e603a995198d8e8411ed
5e7c5e8d9f5864488ddf04b662d1ad8e
63f0f91e3ccf5dd00a455d3038a299f4
66684b8b82fb5318a41ab7e6abb8dd42
677f7c42f79a0a58760056529739fdd6
6afeec03c8f4bc78fa2b3ad27392b0e7
6d00e4f95fba02126b32bb74dc4fec55
6d49cdbade7541d46be3fb47a0f563bb
6de813a22b2b73e330085ec7c85e041b
71f311a648348e7598eb55ab7618842c
723129912a2d0fb4aede7100071787ef
778c1764dd5c36c1eb96c49a8f8441e6
7b92e9d21bc4db838bc102b289f4fd5f
812d8e4d7a484bb363b139cfa08617e5
81591ae1c975b8a0b5ad5546a103992c
81d92e20f3078bd8e43b226308393e43
83429db9cc63196bf42c691cc09b7b84
852f562812305ad099372109f8e8b189
85865e048183849b255c92e609a5fa25
86cce64193a347b50329a32cdf08d198
89bfd463ca76b62c61a548778316567d
8ccea94fd83d9cb1b15a2a4befec24a2
8d3036a65ac2404d4562cdb927fd3d2c
8d78a9e3df1e19f9520f2bbb5f04cb54
8dc61b737990385473dca9bfc826727b
95113e04af14c23df607964fa9d83476
9b198f1e260700bdcb4740266cd35b3f
9c1c2825532b25e266d62db50952ab44
9c544da8c23826379d60581cce17a483
a0e350787e4134ea91ccb26d17cdf167
a1169fb2eb93616ced7536a53fb05648
a431d5786d9d95bc9d04df07cbefc0a2
a6d89df2a80675980fb3e4a9bcc162e2
a77456a160890a26a8f7c019c2e77021
aa6f8eff83aea3ff7b8f016e67f74dac
af6649323daf6dbd3aef1b950588487c
b3840ec1299517dacd6c18c71ff5bafc
b8c99bc028a0a32288d858df7bf6bec1
b990752f8266d7648070bea7e24d326f
ba026e6190aee2c64ef62a4e79419bcf
bea6e3481c0a06ce36600d8b3cc6155b
c87e8a3ceefd93c7e431b753801c6bb6
cb9cc50b18a7c91cf4a34c624b90db5d
cebaaad59f1616698dec4f14d76b4c9a
d04a7f30c83290b86cac8d762dcc2df5
d218706eb07f2722ae4e0106cce27d52
d286c4cdf40e2dae5362eff562bccd3a
d2fe88fff648a0bcbfdf0f0bd042a0a4
d354b71116961cad955ed11cb938ca32
d687cfde1c4ea77de1b92ea2f9e90ad5
d80c29813bfbc3cbcbd469249d49ebf3
d9c0ca95e49b113c5751fffdb20beb3f
d9cf41b5d11e42dabf9470964d09c000
db6e36f962fdb58c8e9f8f9a781fda66
dc01df3c40cb4fb0bef448693475ea1b
def612ad0554006378f185d3b56efb57
e51a4cc0272a98e9eddfec16667603f4
e5b1ffd2ecd7e610d07d093d65639da9
eb5761c410b5139f23235e9b67964495
eefc66a1e978dc9d825f28702106d4d5
efa23860086c5d12d3e6b918073c717f
f3c5c20f5c45fc401484caf72753d778
fad8f37c9bd5420f49cfd5960a60fa24
fb3495715764cdaa547f2b040c0a9b1f
fc3853c2383e2fbb2af381fd1277504d
fe16c30782e2b16b07d5a3a1cf9dfb8f
ff04126a5d61a10c81bfd0a6d0a643d0
Source: https://habr.com/ru/post/182178/
All Articles