About exploits for iOS, bootrom and conflict with Geohot
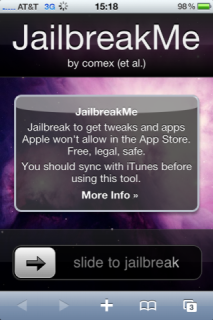 The recent release of the jailbreak from Geohot 'and for devices based on Apple A4 caused a great resonance in the circles of Dev Team . Most developers blamed George Hotz for the selfishness of his intentions, vanity and short-sightedness. Why did this happen?
The recent release of the jailbreak from Geohot 'and for devices based on Apple A4 caused a great resonance in the circles of Dev Team . Most developers blamed George Hotz for the selfishness of his intentions, vanity and short-sightedness. Why did this happen?limera1n - untethered jailbreak from geohot exploits the second known vulnerability in the bootrom of all new iOS devices. Earlier, in September of this year, members of the Dev Team pod2g and posixninja excavated and partially documented the first known vulnerability in the bootrom of the Apple A4 devices. Now Apple is aware of the existence of both vulnerabilities, which are likely to be closed with the next hardware revision of devices.
The thing is that the bootrom (or SecureROM) is a small bootloader that is called by the iPhone / iPad as soon as you turn on the device. The bootrom is usually flashed in read-only NAND (flash memory), which is stitched at the factory when the device is manufactured. All subsequent iOS updates do not affect this area of memory in any way: the bootrom can only be updated with a new hardware revision of devices. That is why all the vulnerabilities found in this section of the code are strategically important.
Upon completion, the bootrom transfers control to the iBoot loader. iBoot is a second stage loader whose task is to partially initialize the device, load the iOS kernel and transfer control to it. iBoot is easily changed when iOS is updated, so all the vulnerabilities found in it are temporary.
')
The entire iOS chaining process looks like this: bootrom -> iBoot -> iOS
An open vulnerability in the bootrom is always a guarantee that the jailbreak will be implemented sooner or later. Vulnerabilities in iBoot or iOS are unreliable and are closed by Apple when iOS is updated. In addition, the jailbreak that is performed through a vulnerability in iBoot is typically tethered, i.e. After rebooting the device, the jailbreak must be performed again.

After the rush release of limera1n, the Dev Team postponed the exit of greenpois0n in order to hide the implementation of the bootrom exploit - Apple's SHAtter to the next generation of devices in which the vulnerability that geohot uses is 100% closed.
If you are interested in this topic, the next time we can consider the principle of operation of exploits for the implementation of the jailbreak.
Source: https://habr.com/ru/post/105872/
All Articles