Kismet
Kismet is a multifunctional free utility for working with wireless networks Wi-Fi. Users are familiar with it mainly through hacking articles, where the program is used to detect hidden networks or capture packets. Hacking other people's networks is bad, and yet Kismet is much more than a master key in the hands of an attacker. In the arsenal of an information security engineer, this program becomes an excellent tool for monitoring and analyzing the 802.11 air.
The Kismet project takes its beginning in the distant 2001. Originally released under the GNU GPL license and regularly updated for almost 10 years, the program has managed to acquire its own community and enter the top ten network analyzers. Despite the fact that Kismet is a cross-platform development, some functions are available only in Linux, and the developer declares the most complete support in this case, therefore, all of the above is true when running on Linux itself.
Before installing Kismet, you need to make sure that the Wi-Fi card supports RFMON monitoring mode. This mode switches the 802.11 adapter to surveillance mode, in which it captures all packets that are on the air. It all depends on the specific case, some devices support this mode without problems, some only a third-party driver can help, and some instances do not have this feature at all.
As always, the packages in the repositories are lagging behind the current developments, so it makes more sense to download the latest version of the source codes and build the program. The procedure is no different from the standard one, there are no specific requirements for the system, except that since the user interface is based on Curses, the corresponding libraries may be required. Looking ahead, it is worth noting that for Kismet there is a separate QT graphical interface.
')
The developer provides different security configurations. Since some actions (for example, changing the mode of operation of a network adapter) require root access, you should take a responsible approach to setting up security during installation. The program is built on a client-server architecture, so allocating rights is not a tricky business, and the documentation details the nuances of this procedure.
If everything was done correctly, the program will start with the command kismet.
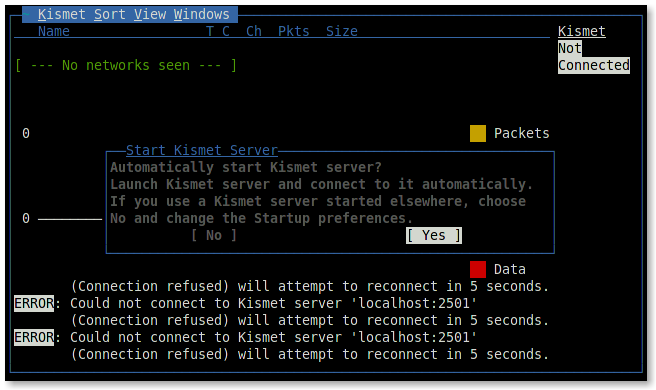
As mentioned earlier, Kismet was built using client-server technology, so when you start the client, you will be prompted to start the server or specify its address. This article assumes that the program is used on one machine, so you should run the local one.
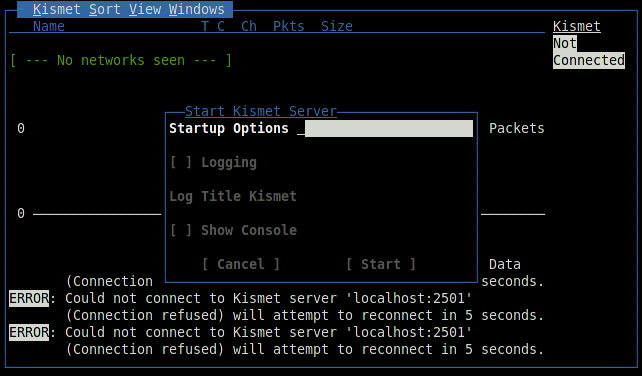
Depending on the task, you can transfer startup parameters to the server, enable or disable logging, and also observe the server console directly in the client interface.
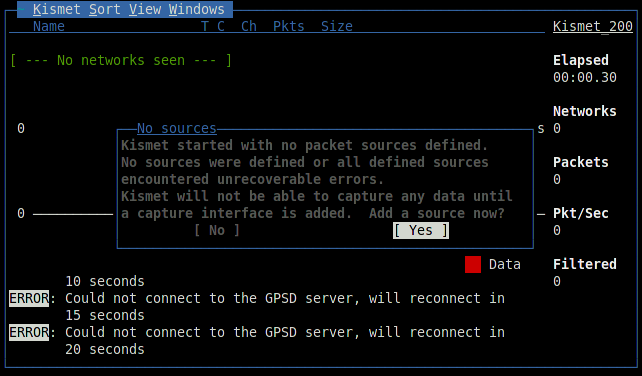
After connecting to the server and starting the scan will begin. Kismet will display information about the found networks. By default, networks with unsecured WEP encryption are highlighted with red, green - with no encryption, and yellow with WPA encryption.
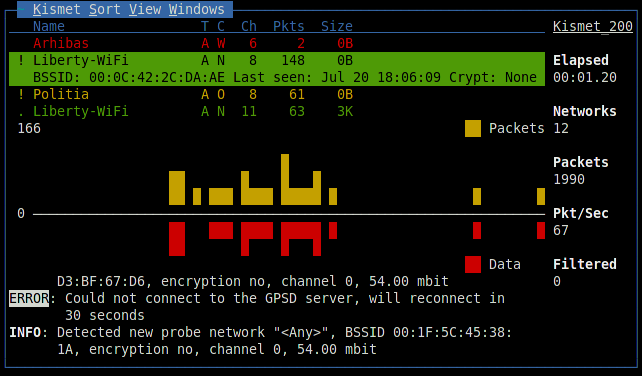
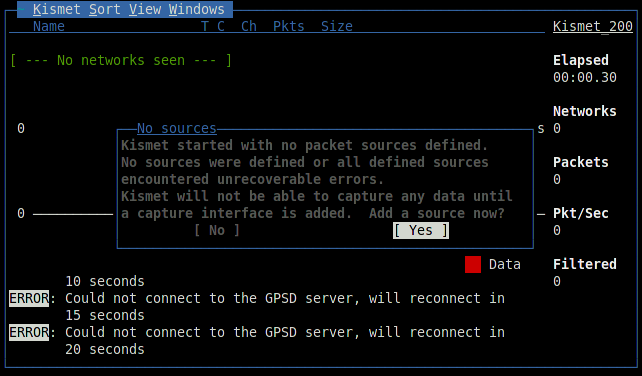
The figures below the list are a visual representation of the packets and data passing on the air, similar graphs will be found in other windows of the program. When you select any network, additional information will appear in the row: an identifier (BSSID), a detection time, an encryption method, the number of packets, and the amount of data transmitted after detection. The exclamation mark, dot or space before the name of the network denotes three activity levels, column T - network type (A = Access point), C - encryption type (W = WEP, N = none, etc.). Data fields can be removed, exactly like adding new ones through the settings menu. The general statistics of observation is displayed on the right, and the Filtered value shows the number of packets that fell under the filters created. A log is kept at the bottom, a careful reader might notice a connection error with the GPSD server there. Kismet can work with a GPS device and supply captured data with geographic coordinates.
When you select a network, a window opens that displays more detailed information:
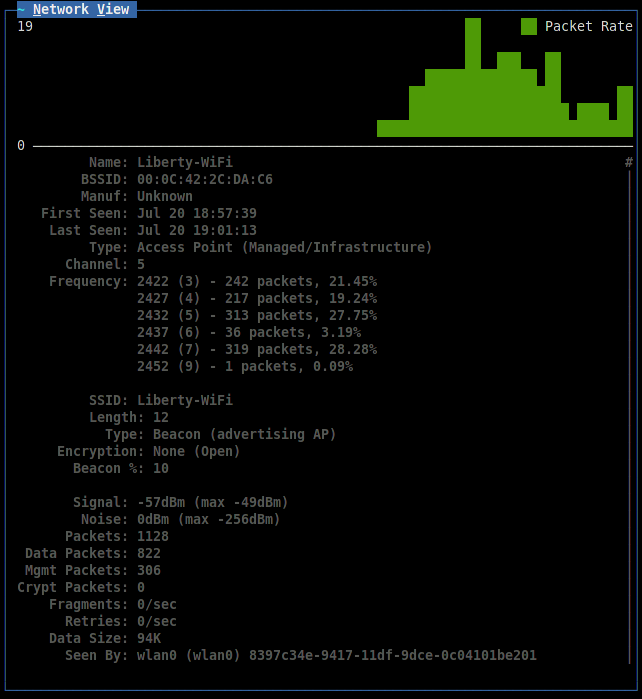
You can add two more graphic indicators: the signal level and the number of repetitions through the View menu. The View → Clients command displays a list of clients connected to the selected access point:
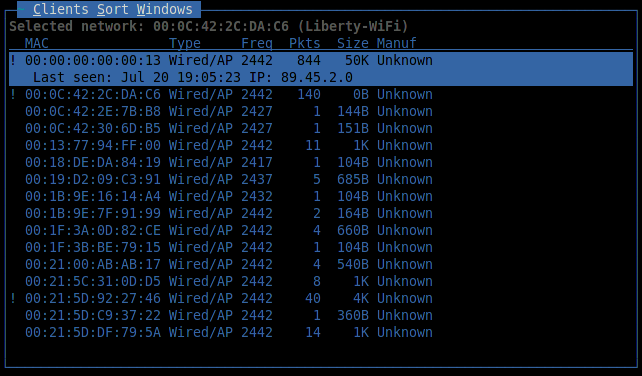
Here, in addition to the basic information, an important parameter is added: the client's IP address.
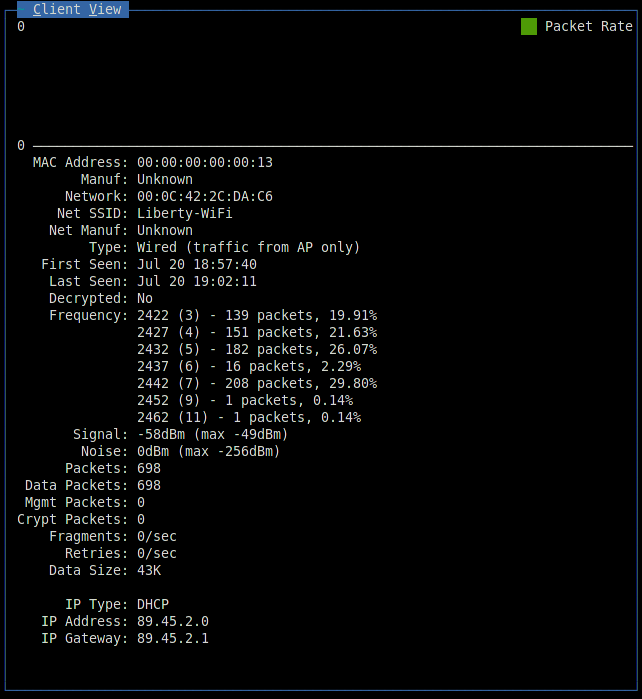
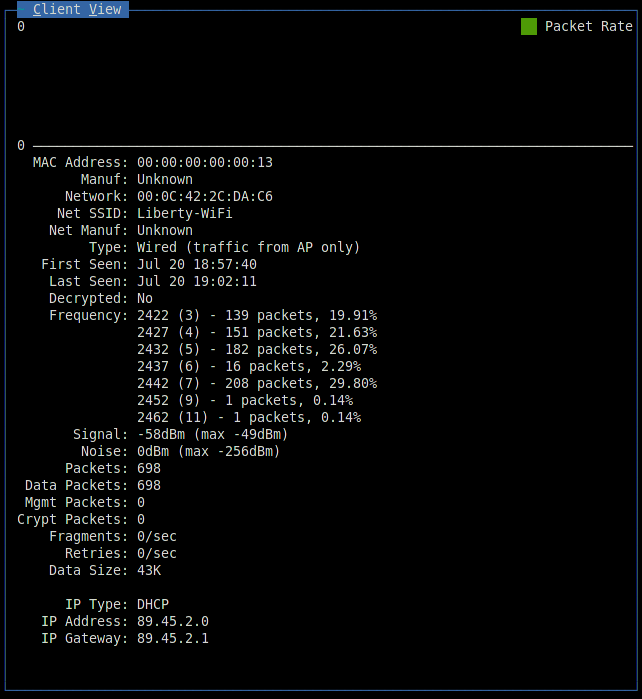
The last Kismet window displays customer information:
Conventionally, the tasks solved with the help of Kismet can be divided into two areas: analytics and protection. In the first case, the accumulated information must be processed by third-party applications, and in the second, Kismet works as a detector of various kinds of network attacks. Consider both profiles better with specific examples.
Most recently, the scandal has died down due to the collection by Google of information about Wi-Fi access points and the capture of part of the traffic. Indeed, according to Raphael Leiteritz, Google’s brand manager, Street View cars collected the coordinates of Wi-Fi points and GSM base stations for the sake of developing navigation service and a whole list of good deeds. Their system worked like this: the Google Street View car used the Maxrad BMMG24005 antenna for receiving the 802.11 broadcast and moved along the route, taking around itself all the data in the Wi-Fi range. The obtained data was processed by Kismet, which, in connection with the GPS receiver, allows you to build a high-quality interception station.
Create your own car Street View, which will deal with so-called. Vardrivingom not as difficult as it seems at first glance. Of the additional equipment, only a GPS receiver is required to bind data to a geographic location.
To begin collecting information, a GPS device must be connected and configured to work through the GPSD daemon. It should be noted that Kismet works with the JSON format and therefore it will not be possible to use GPS emulators for tests, unless the gpsfake utility is included in the GPSD package, which can play the existing logs of navigators. However, GPS tuning is beyond the scope of Kismet discussion.
This time the server must be started in the logging mode to start collecting information. By default, there will be 5 types of logs available: alarm protocol, geographic XML log, text list of detected networks, network XML log and package dump in Pcap format. It was because of the latter that Google was harassed by the public, since in theory this file could contain personal data flying over the air.
If everything is done correctly, then now the main window will display data on the current geographic location. Contrary to popular belief, Kismet does not know the coordinates of a Wi-Fi point, and geographic data is nothing more than the coordinates of a GPS receiver. And although in the presence of a large amount of information it is quite realistic to dispatch the point, the program does not set itself such a task - this is a matter of third-party products.
In the process of movement the logs will grow rapidly, so you should think about the free amount of memory.
The data received by the program is stored in a simple clear format. So, for example, the geographical XML-log we are interested in consists of many such elements:
All attributes are intuitive and to understand the data will not be difficult for any programmer. How to use this data - the decision of the developer. You can build a Wi-Fi map of access points in your area, you can develop a direction finding system. Google said it was collecting data for pseudo-GPS navigation, when base stations are used as a guideline, not satellites. Combining data from various logs, you can collect statistics, analyze, make maps and graphs - everything is limited only by imagination. Anyone can build a part of Google Street View in their car and do some useful research.
Kismet has more serious, though less demanded functionality. It is no secret that many businesses use Wi-Fi for internal communication. Information in such networks is often not intended for the general public. Wireless air protection is no less important than any other measure aimed at maintaining the level of internal security. Kismet can detect a large list of network attacks at the channel and network level. To do this, the program has an alarm mechanism, or simply put it - alerts.
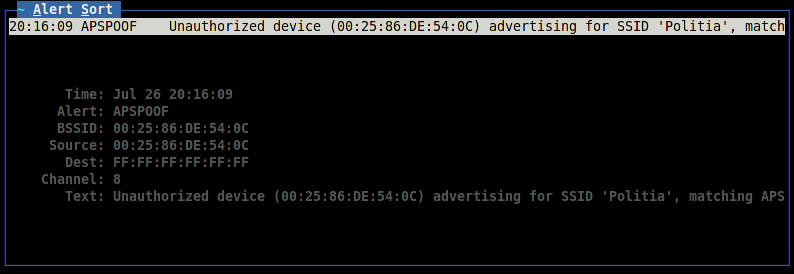
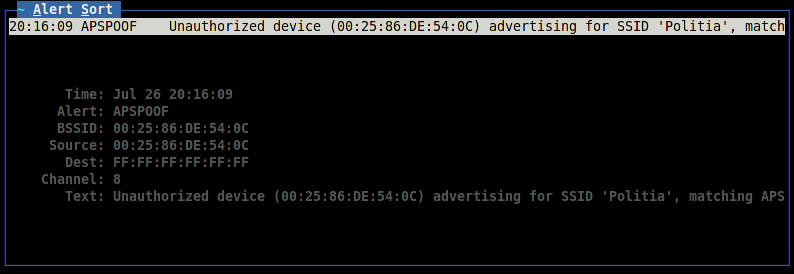
Alarm rules for a particular case are specified in the configuration file. Consider the operation of an intrusion detection system using the example of the APSPOOF rule. This is probably one of the easiest methods - it allows you to recognize the attack , during which the attacker acts as a fake access point.
The configuration of this rule looks like this:
Validmacs are valid MAC address values for an access point named “Politia” that must be protected. Kismet, provoked by Karma Tools, instantly detects and reports in the Alerts window and log.
Other alarm rules are configured in exactly the same way. Using Kismet to protect wireless networks is no more difficult than capturing packets, and when combined with other measures, the overall level of security becomes much higher.
From the stories of the former employee of the Information and Security Service of the Republic of Moldova. In 2005, a certain firm turned to the office asking for help. For almost a year, the company regularly had remittances in the wrong direction. The internal security service waved its hands: they checked the accountants from and to, there were no bank errors, but from somewhere there appeared payment orders in which the account numbers were changed. Everything turned out to be more than trivial: some enterprising guys rented a cabinet on the floor below, found out the password for the Wi-Fi network and sometimes changed the data in bills that the accountant meticulously saved in a shared folder, and then printed to a printer in an important office at a time. For the time being, the fraudsters managed to steal a rather large amount of money.
True or not, it is not known, but such a story could well have happened, and it is called upon once again to remind information security engineers of an important and vulnerable component of a modern corporate network, Wi-Fi wireless data transfer technology.
In fact, this small program can be discussed further. The article does not address the topic of plug-ins, greatly expanding its capabilities. Not so long ago, Kismet moved to a new core, so the number of plug-ins is not large, but among them there is a decent copy - DECT Sniffer, which allows using Kismet to work with telephone networks, there is a plug-in for Bluetooth. But this is a topic for a separate publication. And this article, I hope, has coped with its task - to acquaint Russian-speaking users with another good network development. Maybe Kismet will help someone in the work as it once helped me.
In preparing the article, Kismet documentation was used, which tells in great detail about working with the program; interesting Google letters ; materials from wve.org , where all types of network attacks on wireless networks are collected; The site of the GPSD project (very good documentation on GPS in Linux), personal experience, stories of friends and veterans, defenders of the network front.
The latest version of the program is always available at https://www.kismetwireless.net/download.shtml
UPD: Moved to the blog "Information Security".
The Kismet project takes its beginning in the distant 2001. Originally released under the GNU GPL license and regularly updated for almost 10 years, the program has managed to acquire its own community and enter the top ten network analyzers. Despite the fact that Kismet is a cross-platform development, some functions are available only in Linux, and the developer declares the most complete support in this case, therefore, all of the above is true when running on Linux itself.
Installation
Before installing Kismet, you need to make sure that the Wi-Fi card supports RFMON monitoring mode. This mode switches the 802.11 adapter to surveillance mode, in which it captures all packets that are on the air. It all depends on the specific case, some devices support this mode without problems, some only a third-party driver can help, and some instances do not have this feature at all.
As always, the packages in the repositories are lagging behind the current developments, so it makes more sense to download the latest version of the source codes and build the program. The procedure is no different from the standard one, there are no specific requirements for the system, except that since the user interface is based on Curses, the corresponding libraries may be required. Looking ahead, it is worth noting that for Kismet there is a separate QT graphical interface.
')
The developer provides different security configurations. Since some actions (for example, changing the mode of operation of a network adapter) require root access, you should take a responsible approach to setting up security during installation. The program is built on a client-server architecture, so allocating rights is not a tricky business, and the documentation details the nuances of this procedure.
Preparation for work
If everything was done correctly, the program will start with the command kismet.
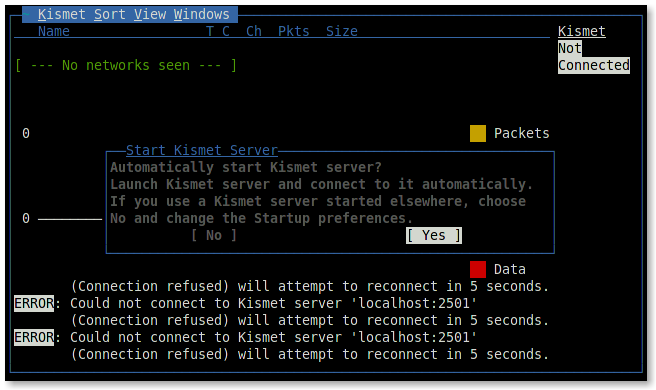
As mentioned earlier, Kismet was built using client-server technology, so when you start the client, you will be prompted to start the server or specify its address. This article assumes that the program is used on one machine, so you should run the local one.
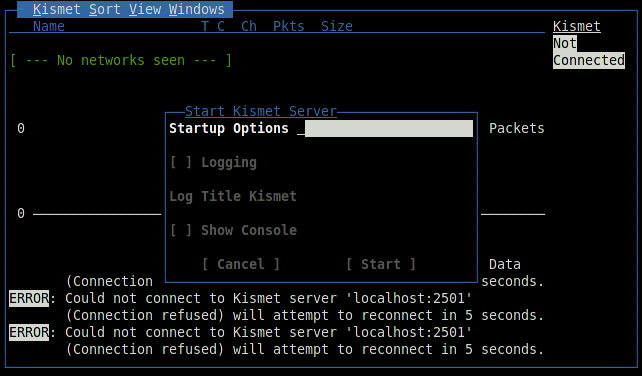
Depending on the task, you can transfer startup parameters to the server, enable or disable logging, and also observe the server console directly in the client interface.
Meet Kismet
After connecting to the server and starting the scan will begin. Kismet will display information about the found networks. By default, networks with unsecured WEP encryption are highlighted with red, green - with no encryption, and yellow with WPA encryption.
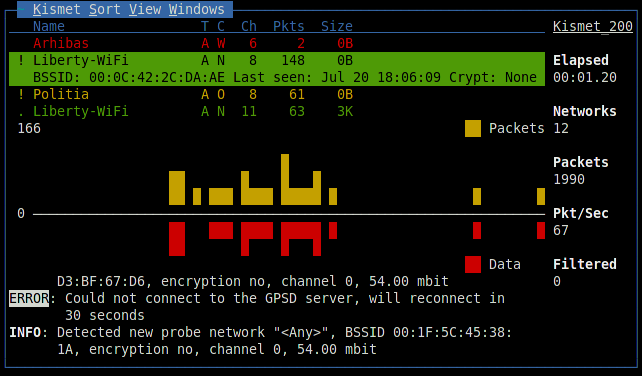
The figures below the list are a visual representation of the packets and data passing on the air, similar graphs will be found in other windows of the program. When you select any network, additional information will appear in the row: an identifier (BSSID), a detection time, an encryption method, the number of packets, and the amount of data transmitted after detection. The exclamation mark, dot or space before the name of the network denotes three activity levels, column T - network type (A = Access point), C - encryption type (W = WEP, N = none, etc.). Data fields can be removed, exactly like adding new ones through the settings menu. The general statistics of observation is displayed on the right, and the Filtered value shows the number of packets that fell under the filters created. A log is kept at the bottom, a careful reader might notice a connection error with the GPSD server there. Kismet can work with a GPS device and supply captured data with geographic coordinates.
When you select a network, a window opens that displays more detailed information:
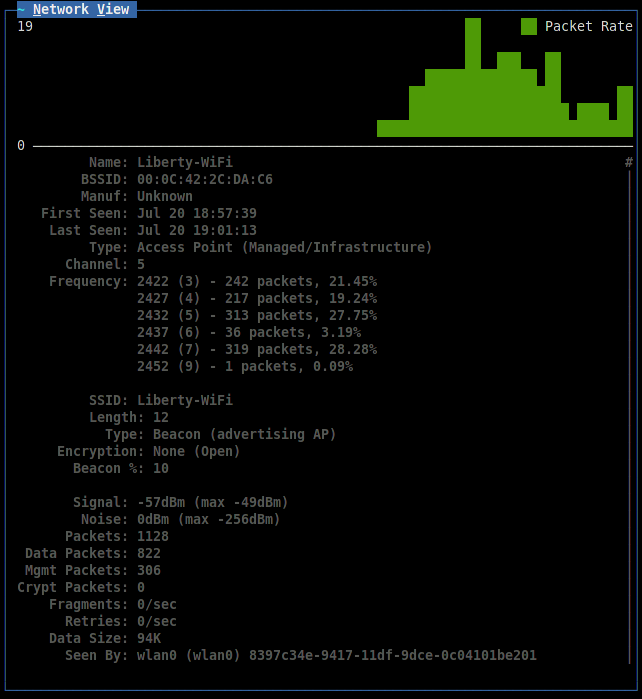
You can add two more graphic indicators: the signal level and the number of repetitions through the View menu. The View → Clients command displays a list of clients connected to the selected access point:
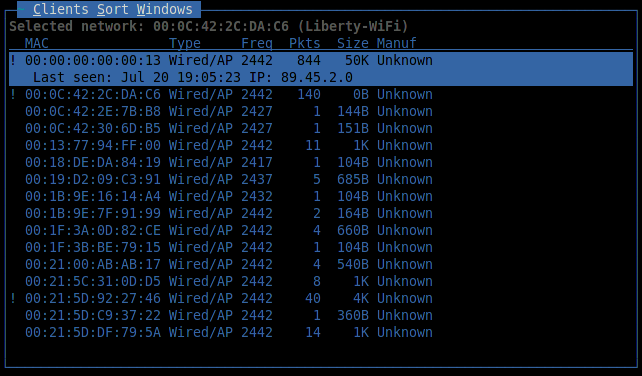
Here, in addition to the basic information, an important parameter is added: the client's IP address.
The last Kismet window displays customer information:
Using the program in practice
Conventionally, the tasks solved with the help of Kismet can be divided into two areas: analytics and protection. In the first case, the accumulated information must be processed by third-party applications, and in the second, Kismet works as a detector of various kinds of network attacks. Consider both profiles better with specific examples.
Geographic statistics collection
Most recently, the scandal has died down due to the collection by Google of information about Wi-Fi access points and the capture of part of the traffic. Indeed, according to Raphael Leiteritz, Google’s brand manager, Street View cars collected the coordinates of Wi-Fi points and GSM base stations for the sake of developing navigation service and a whole list of good deeds. Their system worked like this: the Google Street View car used the Maxrad BMMG24005 antenna for receiving the 802.11 broadcast and moved along the route, taking around itself all the data in the Wi-Fi range. The obtained data was processed by Kismet, which, in connection with the GPS receiver, allows you to build a high-quality interception station.
Create your own car Street View, which will deal with so-called. Vardrivingom not as difficult as it seems at first glance. Of the additional equipment, only a GPS receiver is required to bind data to a geographic location.
To begin collecting information, a GPS device must be connected and configured to work through the GPSD daemon. It should be noted that Kismet works with the JSON format and therefore it will not be possible to use GPS emulators for tests, unless the gpsfake utility is included in the GPSD package, which can play the existing logs of navigators. However, GPS tuning is beyond the scope of Kismet discussion.
This time the server must be started in the logging mode to start collecting information. By default, there will be 5 types of logs available: alarm protocol, geographic XML log, text list of detected networks, network XML log and package dump in Pcap format. It was because of the latter that Google was harassed by the public, since in theory this file could contain personal data flying over the air.
If everything is done correctly, then now the main window will display data on the current geographic location. Contrary to popular belief, Kismet does not know the coordinates of a Wi-Fi point, and geographic data is nothing more than the coordinates of a GPS receiver. And although in the presence of a large amount of information it is quite realistic to dispatch the point, the program does not set itself such a task - this is a matter of third-party products.
In the process of movement the logs will grow rapidly, so you should think about the free amount of memory.
The data received by the program is stored in a simple clear format. So, for example, the geographical XML-log we are interested in consists of many such elements:
< gps-point bssid ="00:0C:42:2C:DA:C6" source ="00:0C:42:2C:DA:C6" time-sec ="1280155487" time-usec ="724329" lat ="47.133453" lon ="28.504967" spd ="0.000000" heading ="0.200000" fix ="3" alt ="1225.000000" signal_dbm ="-61" noise_dbm ="0" />All attributes are intuitive and to understand the data will not be difficult for any programmer. How to use this data - the decision of the developer. You can build a Wi-Fi map of access points in your area, you can develop a direction finding system. Google said it was collecting data for pseudo-GPS navigation, when base stations are used as a guideline, not satellites. Combining data from various logs, you can collect statistics, analyze, make maps and graphs - everything is limited only by imagination. Anyone can build a part of Google Street View in their car and do some useful research.
Intrusion detection
Kismet has more serious, though less demanded functionality. It is no secret that many businesses use Wi-Fi for internal communication. Information in such networks is often not intended for the general public. Wireless air protection is no less important than any other measure aimed at maintaining the level of internal security. Kismet can detect a large list of network attacks at the channel and network level. To do this, the program has an alarm mechanism, or simply put it - alerts.
Alarm rules for a particular case are specified in the configuration file. Consider the operation of an intrusion detection system using the example of the APSPOOF rule. This is probably one of the easiest methods - it allows you to recognize the attack , during which the attacker acts as a fake access point.
The configuration of this rule looks like this:
apsproof=Rule1:ssid="Politia", validmacs="70:3A:02:01:CE:AF"Validmacs are valid MAC address values for an access point named “Politia” that must be protected. Kismet, provoked by Karma Tools, instantly detects and reports in the Alerts window and log.
Other alarm rules are configured in exactly the same way. Using Kismet to protect wireless networks is no more difficult than capturing packets, and when combined with other measures, the overall level of security becomes much higher.
From the stories of the former employee of the Information and Security Service of the Republic of Moldova. In 2005, a certain firm turned to the office asking for help. For almost a year, the company regularly had remittances in the wrong direction. The internal security service waved its hands: they checked the accountants from and to, there were no bank errors, but from somewhere there appeared payment orders in which the account numbers were changed. Everything turned out to be more than trivial: some enterprising guys rented a cabinet on the floor below, found out the password for the Wi-Fi network and sometimes changed the data in bills that the accountant meticulously saved in a shared folder, and then printed to a printer in an important office at a time. For the time being, the fraudsters managed to steal a rather large amount of money.
True or not, it is not known, but such a story could well have happened, and it is called upon once again to remind information security engineers of an important and vulnerable component of a modern corporate network, Wi-Fi wireless data transfer technology.
Conclusion
In fact, this small program can be discussed further. The article does not address the topic of plug-ins, greatly expanding its capabilities. Not so long ago, Kismet moved to a new core, so the number of plug-ins is not large, but among them there is a decent copy - DECT Sniffer, which allows using Kismet to work with telephone networks, there is a plug-in for Bluetooth. But this is a topic for a separate publication. And this article, I hope, has coped with its task - to acquaint Russian-speaking users with another good network development. Maybe Kismet will help someone in the work as it once helped me.
In preparing the article, Kismet documentation was used, which tells in great detail about working with the program; interesting Google letters ; materials from wve.org , where all types of network attacks on wireless networks are collected; The site of the GPSD project (very good documentation on GPS in Linux), personal experience, stories of friends and veterans, defenders of the network front.
The latest version of the program is always available at https://www.kismetwireless.net/download.shtml
UPD: Moved to the blog "Information Security".
Source: https://habr.com/ru/post/100503/
All Articles